WiFi client isolation can be bypassed by manually crafting and injecting frames in monitor mode, allowing direct communication between attacker and victim without the access point’s involvement. The article details the underlying mechanisms, tools, and mitigations, including how WPA2-PSK handshakes and key derivation enable the attack and why WPA3 or Enterprise authentication is recommended. #WiFiClientIsolation #WPA2-PSK
Keypoints
- Client isolation blocks direct device-to-device traffic on shared WiFi networks, but can be bypassed through crafted frames in monitor mode.
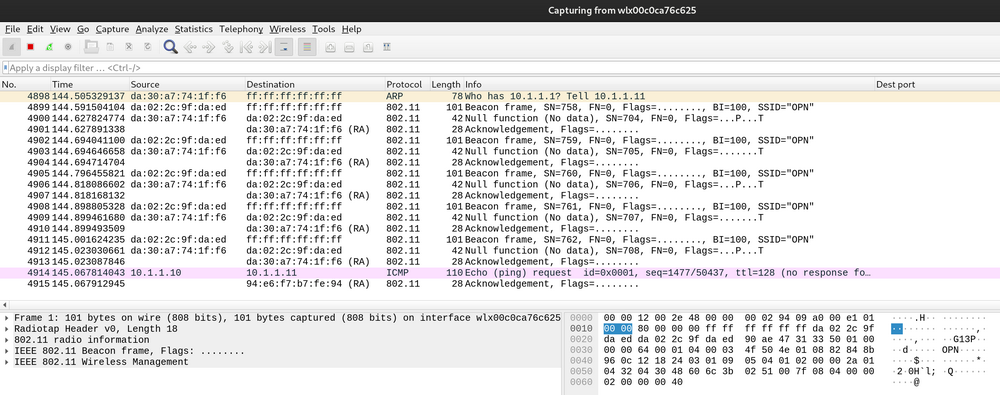
- The attack uses DS framing (From-DS/To-DS) to masquerade frames as AP-originated, enabling direct client communication.
- On WPA2-PSK networks, capturing the 4-way handshake allows deriving PMK, PTK, and GTK to decrypt and inject traffic.
- A TAP interface and a monitor‑mode NIC, combined with Scapy, are used to bridge attacker and victim traffic and bypass the AP.
- Mitigations include upgrading to WPA3 (SAE with Perfect Forward Secrecy) or Enterprise authentication; PPSK with VLAN isolation may help in WPA2 environments.
Read More: https://pulsesecurity.co.nz/articles/bypassing-wifi-client-isolation