The leaked October 2025 APT35 corpus documents a quota-driven, bureaucratic IRGC cyber-intelligence apparatus that weaponized Exchange (ProxyShell, Autodiscover, EWS) and Ivanti vulnerabilities, ran HERV-style phishing seeded from harvested Global Address Lists, and maintained persistent mailbox monitoring backed by centralized KPI reporting and on-premises operator attendance logs. #APT35 #ProxyShell
Keypoints
- Internal APT35 documents leaked on GitHub reveal a regimented, quota-driven cyber-operations unit with formal supervisor reviews, KPI templates, and attendance logs indicating a centralized workplace and chain of command.
- The group executed region-wide Exchange exploitation campaigns (ProxyShell, Autodiscover, EWS) to export Global Address Lists (GALs), then weaponized those contacts with HERV-style phishing for credential harvest and sustained HUMINT collection.
- Technical artifacts include LSASS memory dumps (plaintext creds/NTLM hashes), annotated ProxyShell target lists, Exchange GAL exports, web access logs showing RDP probes and .env/SendGrid fetches, and bespoke Ivanti exploit wrappers.
- Tooling comprised webshells (m0s.*), custom RAT family (RAT-2Ac2), Python operator clients using Accept-Language header carry, PowerShell loaders, and cloud-staged exfiltration (Mega, Dropbox, ProtonDrive).
- Personnel records and conference badges link named individuals (e.g., Engineer Kian, Engineer Reza, Abbas Rahrovi) to Unit 50 / IRGC IO structures, indicating state-directed operations rather than freelance actors.
- The leak exposes clear detection and deception opportunities: monitor GAL exports, anomalous Accept-Language header payloads, ProgramData stager paths, and correlate badge logs with intrusion timestamps for HUMINT-driven disruption.
- Operational evolution shows a move from manual, Exchange-focused intrusions in 2022 to hybrid large-scale reconnaissance, appliance RCEs (Ivanti), and repeatable KPI-driven campaign cycles through 2025.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Used to weaponize Exchange and Ivanti vulnerabilities for initial access (‘run ProxyShell, Autodiscover, and EWS attacks;’).
- [T1505.003] Web Shell – Public-facing webshells used for hands-on control and staging (webshell filename pattern ‘m0s.*’ observed across targets: ‘m0s.*’).
- [T1003.001] OS Credential Dumping: LSASS Memory – Memory dumps with plaintext credentials and NTLM hashes (LSASS dump ‘mfa.tr.txt’ containing plaintext creds & NTLM hashes: ‘LSASS dump (Mimikatz) from MFA.KKTC, Apr 2022 , plaintext creds & NTLM hashes.’).
- [T1566] Phishing – HERV-style phishing campaigns weaponized with harvested GAL contacts to collect credentials and drive persistent access (‘phishing herv.pdf … HERV, style lure templates, campaign metrics, and operational procedures for turning harvested GALs into active collection nodes.’).
- [T1114] Email Collection – Sustained mailbox monitoring and GAL exportation used for HUMINT collection (‘validate shells and extract Global Address Lists (GALs); weaponize harvested contacts with HERV phishing; and maintain sustained intelligence collection through mailbox monitoring.’).
- [T1071.001] Application Layer Protocol: Web Protocols – C2 and operator command channels over HTTP(S) using Accept-Language header and static header token (‘Python clients … embed the command inside an HTTP header (notably Accept-Language) … accompanied by a static header token’).
- [T1059.001] Command and Scripting Interpreter: PowerShell – PowerShell automation used for exploit chains, GAL exports, and in-memory loaders (‘weaponized PowerShell scripts for GAL exports’).
- [T1047] Windows Management Instrumentation – Remote execution and lateral movement via WMIC observed in operator tool UI and scripts (‘the operator then dispatches … WMIC and net use commands programmatically’).
- [T1021.001] Remote Services: SMB/Windows Admin Shares – Lateral movement using net use and SMB admin share mounts for remote execution (‘net use C$’ used to execute queued commands).’
- [T1550] Use of Valid Accounts – Credential reuse, token replay, and OAuth token abuse employed for persistence and pivoting (‘credential replay and reuse … OAuth token replay for persistent access’).
- [T1036] Masquerading – Stagers and persistence artifacts hidden under plausible system-like filenames and ProgramData paths (‘place[s] artifacts into ProgramData and masqueraded under plausible Windows service names … vmware-tools.exe’).
- [T1567.002] Exfiltration to Cloud Storage – Data staged to cloud services such as Mega/Dropbox/ProtonDrive using encrypted archives (‘exfiltration channels include encrypted 7zip archives staged to cloud storage (Mega, Dropbox, ProtonDrive)’).
Indicators of Compromise
- [IP Address ] operational relay / egress and target probes – 128.199.237.132 (RIPE, relay/egress), 212.175.168.58 (Türk Telekom, observed Exchange-target activity), and 5 more IPs in logs.
- [Domain ] targeted mail estates and gateways – mfa.gov.ct.tr, alrabie.com, and other mail hosts such as customs.gov.lb and mail.yousifi.com.kw (multiple government and commercial mail domains referenced).
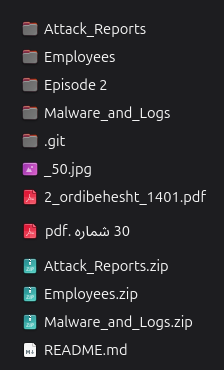
- [File name ] forensic artifacts and dumps – mfa.tr.txt (LSASS dump with plaintext creds), access.log.txt (Dec 2023–Jan 2025 web access logs), and several operational documents (phishing herv.pdf, Ivanti سند بررسی…pdf) among other files.
- [File path / stager ] persistence and masquerade paths – C:ProgramDataMicrosoftdiagnosticvmware-tools.exe, C:ProgramDataMicrosoftdiagnosticsvchost.bat (stager/dropper paths used for persistence).
- [Webshell / endpoint ] webshell naming and endpoints – m0s.* webshells and predictable ASPX paths (aspnet_client/, owa/auth/, exchange/temp/) used for remote command execution and staging.
- [HTTP header / token ] operator client fingerprint – static Accept-Captcha header token and use of Accept-Language to carry commands (static header token in Python clients observed), and long/encoded Accept-Language payloads.