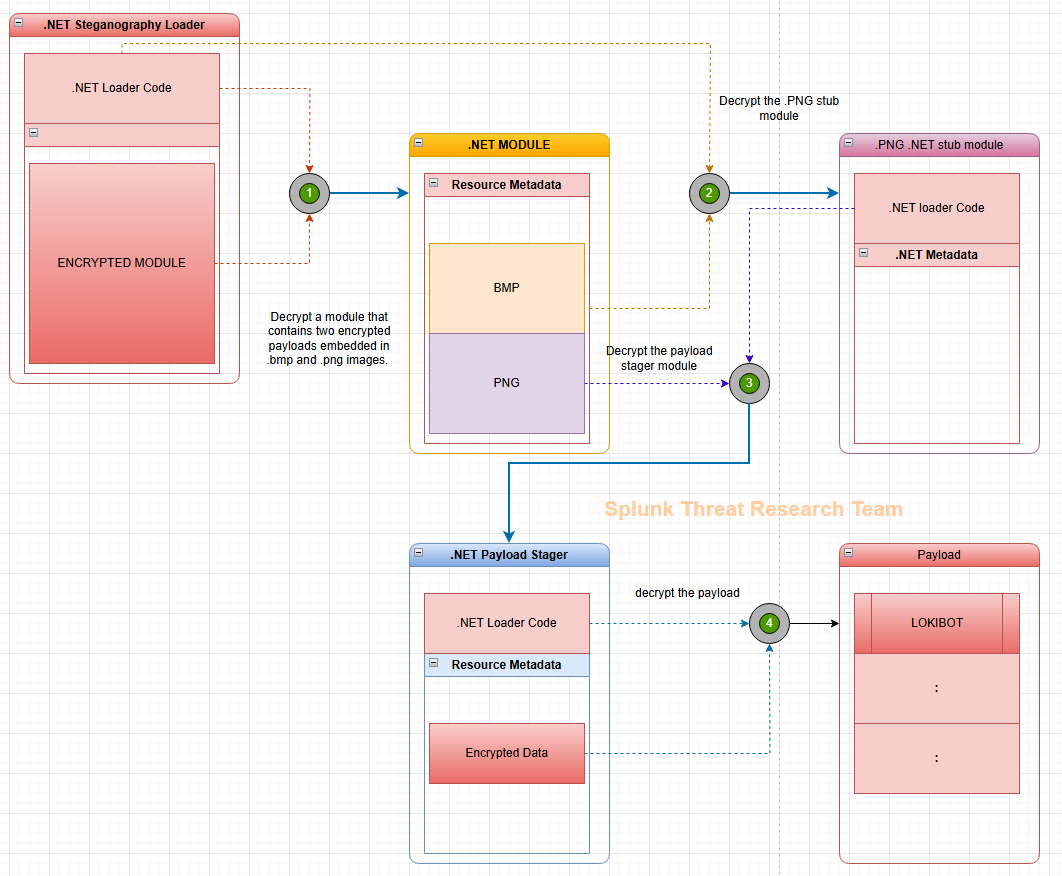
Splunk Threat Research Team analyzed a new .NET steganographic loader variant that decrypts and loads a container module at runtime to hide two image-embedded stagers, one of which yielded a Lokibot payload. The report details the loader’s steganography, extraction attempts with PixDig, Lokibot capabilities (credential theft, injection, scheduled task persistence, downloading additional payloads) and mapped MITRE techniques to support detection development. #Lokibot #QuasarRAT
Keypoints
- The analyzed .NET steganography loader disguises itself as a business document and uses resource metadata images to hide stager modules.
- This loader variant decrypts and loads a separate container module at runtime, increasing difficulty for static detection and automated payload extraction.
- STRT modified their PixDig tool and scripts to extract two stager modules from embedded BMP/PNG images and successfully decrypted a Lokibot payload.
- Lokibot functions observed include system information discovery, stealing credentials from browsers/clients/password managers, process injection, token manipulation, scheduled task persistence, and downloading additional components.
- The report maps multiple observed behaviors to MITRE ATT&CK techniques and provides 26 Splunk detections covering those tactics and techniques for operational detection use.
- The report includes example SHA256s for the steganography loader samples and guidance to implement detections via Splunk Enterprise Security Content Updates or Splunk Security Essentials.
MITRE Techniques
- [T1497.003 ] Time Based Evasion – Lokibot checks for a “-u” parameter and if present sleeps for 10 seconds before executing main code. Quote: ‘the malware will pause for 10 seconds before running its main code.’
- [T1082 ] System Information Discovery – Lokibot collects username, token membership, native system details, OS version, and machine GUID used to create a mutex. Quote: ‘collects various system information… machine GUID, which it uses to generate a mutex.’
- [T1555 ] Credentials from Password Stores – Lokibot targets browsers, FTP clients, vaults, and password managers to harvest stored credentials and related data. Quote: ‘functions designed to collect sensitive information from various sources, including web browsers, FTP clients, vaults, and password managers.’
- [T1105 ] Ingress Tool Transfer – Lokibot downloads additional malware/plugins using UrlDownloadToFileW() and saves files to %temp% with random names before executing them. Quote: ‘capable of downloading additional malware, plugins, or malicious components… using the UrlDownloadToFileW() Windows API.’
- [T1134 ] Access Token Manipulation – Lokibot attempts to enable SeDebugPrivilege to gain elevated permissions for interacting with protected processes. Quote: ‘attempts to enable the SeDebugPrivilege token to gain higher-level permissions on the compromised system.’
- [T1055 ] Process Injection – Lokibot injects shellcode into lsass.exe for credential dumping and the loader injects Lokibot into a newly created vbc.exe process. Quote: ‘injecting shellcode into the lsass.exe process… loader injects Lokibot into a newly created vbc.exe process.’
- [T1552.002 ] Credentials in Registry – Lokibot reads Outlook profile registry entries to extract email account credentials and server settings. Quote: ‘accesses Outlook profile information stored in the Windows registry to extract email account credentials, server settings, and other configuration data.’
- [T1053 ] Scheduled Task/Job – Lokibot creates a scheduled task pointing to a dropped copy of itself to maintain persistence across reboots. Quote: ‘creates a scheduled task that points to a dropped copy of itself on the compromised host.’
Indicators of Compromise
- [File Hash ] Steganography loader and Lokibot samples – 6b8cd32010895abeebbe3f8acfc9718748dfaa7b6a6a5994178b5b1712121c02 (Steganography Loader with Lokibot), dce6b152b3a0a2aef99b6b837813d9bb8335d4de7555af0e175c84a137380dd5 (Steganography Loader)
- [File Hash ] Additional loader hashes – afadf2ba580bb4b4ebf838defaa64f03da77b6a0418f9fab29fea55558ebfcf7, d8fcaf8be0aa2646663d12005285f5afc10a2ed324fc963b50adcd79802a716 (more steganography loader samples)
- [File Names / Artifacts ] Embedded resource image names – “crc” (.bmp) and “IVBD” (.png) used as containers for stager modules extracted from the loader resources.
- [API / Function ] Download and persistence artifacts – use of UrlDownloadToFileW() saving files to %temp% with random filenames (indicative of subsequent payloads), and scheduled task creation via schtasks.exe with /xml parameter.