Huntress observed threat actors exploit a recently patched WSUS RCE vulnerability (CVE-2025-59287) to gain initial access and then install Velociraptor to establish command-and-control on the endpoint. The actors retrieved a malicious MSI from s3.wasabisys[.]com and configured Velociraptor to communicate with update[.]githubtestbak[.]workers[.]dev. #CVE-2025-59287 #Velociraptor
Keypoints
- Huntress detected an incident where actors exploited a WSUS deserialization RCE (CVE-2025-59287) to gain initial access to a server.
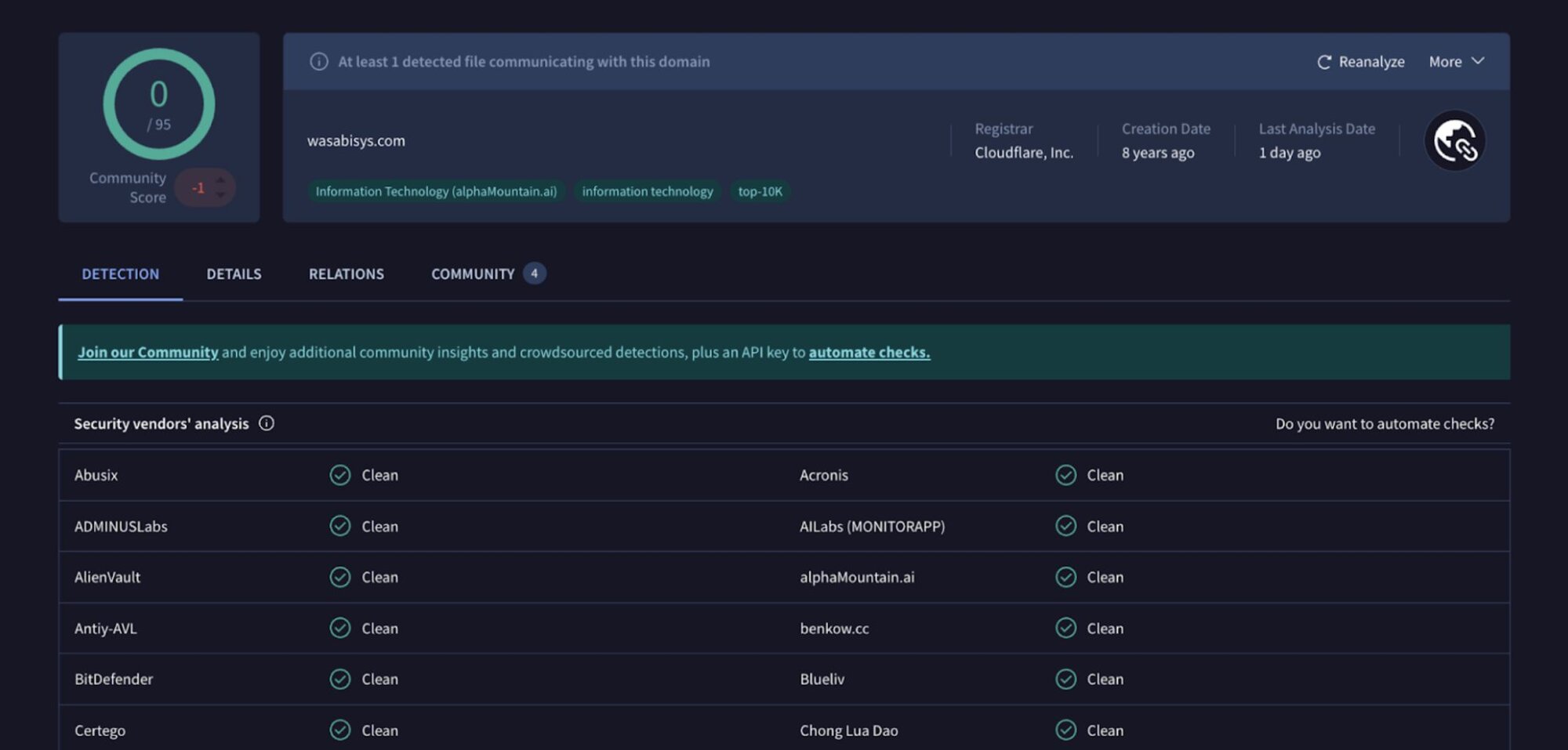
- After exploitation, the threat actors installed Velociraptor via a malicious MSI retrieved from s3.wasabisys[.]com.
- Velociraptor was configured as a service and used to communicate with a C2 endpoint at update[.]githubtestbak[.]workers[.]dev.
- Post-install activity included Velociraptor spawning base64-encoded PowerShell child processes that performed discovery queries (user, services, SPNs, network configuration).
- Event log artifacts showed MSI installer events, Service Control Manager entries for Velociraptor service creation and start, and Velociraptor startup arguments.
- Huntress contained the actor’s activity during this incident and notes a recent uptick in Velociraptor misuse over the prior three months.
- Velociraptor joins other legitimate dual-use tools (e.g., Cobalt Strike, Mimikatz) that threat actors commonly abuse for remote access and post-exploitation.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Threat actors exploited a WSUS deserialization vulnerability (CVE-2025-59287) to gain initial access. Quote: ‘the deployment of Velociraptor by threat actors after they had gained initial access through exploitation of a flaw in WSUS (Microsoft’s centralized update distribution service…)’
- [T1105] Ingress Tool Transfer – Malicious MSI retrieved from an external storage domain and installed on the host. Quote: ‘installing a malicious MSI package from s3[.]wasabisys[.]com.’
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys and Startup Folder (service) – Velociraptor was installed as a service and configured for auto start. Quote: ‘Service Control Manager/7045;Velociraptor Service…user mode service,auto start,LocalSystem’
- [T1059.001] Command and Scripting Interpreter: PowerShell – Velociraptor spawned base64-encoded PowerShell commands to perform discovery. Quote: ‘we observed a number of base64-encoded PowerShell commands, which were child processes of Velociraptor.exe’
- [T1083] File and Directory Discovery – Commands launched to enumerate system information and configurations (e.g., ipconfig, quser). Quote: ‘These commands launched a series of discovery queries, allowing the threat actor to gather information about users, running services, configurations, and more.’
- [T1016] System Network Configuration Discovery – Use of ipconfig to collect network configuration as part of discovery. Quote: ‘”C:Windowssystem32ipconfig.exe” /al’
- [T1033] System Owner/User Discovery – Use of quser to enumerate logged-on users. Quote: ‘”C:Windowssystem32quser.exe”‘
- [T1087.002] Account Discovery: Domain Account – Use of net.exe to query domain groups and setspn to find service accounts. Quote: ‘”C:Windowssystem32net.exe” group “domain computers” /do’ and ‘”C:Windowssystem32setspn.exe” -Q VeeamBackupSVC/*”‘
Indicators of Compromise
- [Domain] Malicious MSI hosting and retrieval – s3[.]wasabisys[.]com (source of v4.msi)
- [Domain] Velociraptor C2 – update[.]githubtestbak[.]workers[.]dev (configured C2 endpoint)
- [File path / Service] Installed binary and service – “C:Program FilesVelociraptorVelociraptor.exe” configured with “C:Program FilesVelociraptor/client.config.yaml” and registered as Velociraptor Service
- [Event logs] Installer and service events – MsiInstaller/1040 referencing https://s3.wasabisys.com/kiessler/v4.msi and Service Control Manager/7045 and /7036 events showing service installation and running
- [Command lines] Suspicious PowerShell and discovery commands – base64-encoded PowerShell execution examples and commands such as quser.exe, setspn.exe -Q VeeamBackupSVC/*, ipconfig.exe /al
Read more: https://www.huntress.com/blog/velociraptor-misuse-part-one-wsus-up