Kaspersky GReAT discovered the Tsundere botnet in mid-2025, a Node.js-based botnet that installs via MSI or PowerShell, uses npm components (ws, ethers, pm2) for persistence, and retrieves WebSocket C2 addresses from an Ethereum smart contract. The botnet is linked to prior October 2024 typosquatting npm supply-chain activity and to a Russian-speaking actor potentially known as “koneko”, with shared infrastructure tied to the 123 Stealer panel. #Tsundere #123Stealer
Keypoints
- Tsundere is a Node.js-based botnet observed from mid-2025 that infects Windows primarily via MSI installers and PowerShell scripts and may be spread via RMM tools or game-themed lures.
- Early related activity (Oct 2024) used typosquatting npm packages (287 malicious packages targeting Puppeteer, Bignum.js, crypto libraries) to deliver payloads to Windows, Linux, and macOS before being removed.
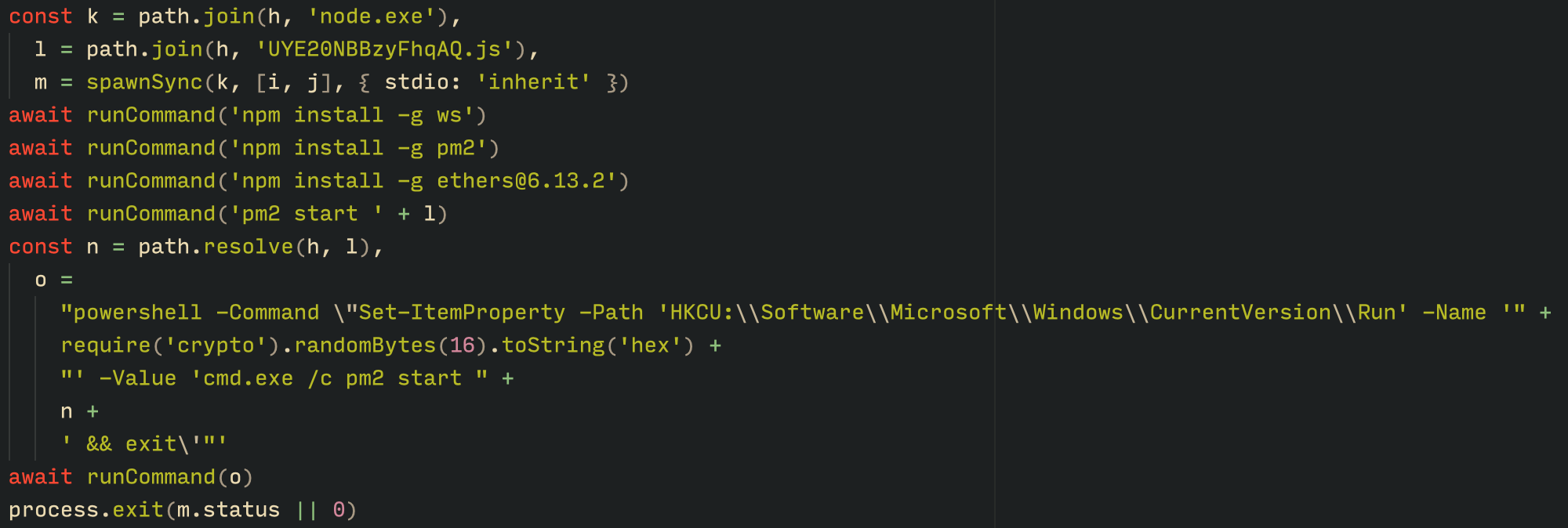
- MSI installers drop Node.js binaries and obfuscated JavaScript files into %LOCALAPPDATA%nodejs, execute a Base64-encoded PowerShell command to spawn a hidden node.exe process, and run a loader that decrypts the main bot and config using AES-256-CBC.
- The PowerShell infector can deploy Node.js from the official nodejs.org ZIP, decrypt embedded scripts, write package.json and dependencies (ws, ethers, pm2), and achieve persistence via HKCU Run registry entries and pm2 registry persistence.
- C2 addresses are stored and rotated via an Ethereum smart contract (contract 0xa1b4…6c6b) updated by wallet 0x73625B6c…4a32; bots fetch the WebSocket C2 (e.g., ws://185.28.119[.]179:1234) through public RPC providers.
- Communication uses WebSockets with an initial AES key exchange, encrypted messaging thereafter, periodic encrypted ping/pong keepalive, and remote evaluation of dynamic JavaScript sent by the C2 (ID=1) to perform arbitrary actions.
- The Tsundere control panel (“Tsundere Netto” v2.4.4) includes an open registration build system and marketplace, ties builds to unique build IDs, and shares infrastructure with the 123 Stealer panel, linking the actor to “koneko”.
MITRE Techniques
- [T1553] Create or Modify System Process – Installer and loader create persisted Node.js processes and use pm2 to ensure the bot restarts and persists (installer runs node.exe to spawn loader; “pm2 helps achieve persistence on the system by writing to the registry and configuring itself to restart the process upon login”).
- [T1059.007] Command and Scripting Interpreter: JavaScript – The bot executes dynamic JavaScript received from C2 by evaluating functions sent with ID=1 (“the message is evaluated as a new function and then executed”).
- [T1505.003] Server Software Component: Web Server – Uses WebSocket servers as C2 endpoints for command-and-control communication (C2 located at addresses such as ws://185.28.119[.]179:1234 and others listed).
- [T1573.002] Encrypted Channel: Symmetric Cryptography – Communication after connection is encrypted using AES (server sends nonce/IV and AES key used for subsequent encrypted messages: “An AES key is transmitted… The server then sends a nonce (IV), enabling the use of encrypted communication”).
- [T1204.002] User Execution: Malicious File – MSI installers disguised as game installers and PowerShell scripts lure users into executing malicious installers (“installer was often disguised as a fake installer for popular games” and PowerShell droppers deploy Node.js and scripts).
- [T1071.004] Application Layer Protocol: Web Protocols – Uses WebSocket protocol for C2 traffic and keepalive ping/pong messages to maintain active bot lists (“The Tsundere bot establishes a WebSocket connection… keep-alive messages are sent every minute using ping/pong messages”).
- [T1608.002] Compromise Infrastructure: Use of Third-party Infrastructure – Stores and rotates C2 addresses in an Ethereum smart contract, leveraging blockchain immutability and public RPC endpoints to retrieve C2 (“the Tsundere botnet utilizes the Ethereum blockchain… state variable param1 … used by the Tsundere botnet administrators to store new WebSocket C2 servers”).
- [T1078] Valid Accounts – Open registration in the control panel allows creation of builds and accounts to manage bots and marketplace offerings (“it has an open registration system… any user… can register and gain access to the panel”).
Indicators of Compromise
- [File Hash ] Malware sample hashes – 235A93C7A4B79135E4D3C220F9313421760B026E… (single long hash shown), and other hashes (and 2 more hashes available to customers).
- [File Path ] Installation path used by MSI/PowerShell infectors – %APPDATA%LocalNodeJS (contains node.exe, npm.cmd, npx.cmd and malicious JS files).
- [Domain/IP ] WebSocket C2 servers – ws://185.28.119[.]179:1234, ws://196.251.72[.]192:1234, and others such as ws://103.246.145[.]201:1234, ws://193.24.123[.]68:3011, ws://62.60.226[.]179:3001.
- [Smart Contract / Wallet ] Blockchain C2 retrieval – Contract 0xa1b40044EBc2794f207D45143Bd82a1B86156c6b and wallet 0x73625B6cdFECC81A4899D221C732E1f73e504a32 used to store/rotate C2 addresses.
- [File Name ] Dropped and executed files – examples include pdf.msi (downloaded via compromised site), game-themed sample names like “valorant”, “cs2”, “r6x” used as lure filenames.
Read more: https://securelist.com/tsundere-node-js-botnet-uses-ethereum-blockchain/117979/