Two interconnected 2025 campaigns used large-scale brand impersonation to deliver Gh0st RAT variants to Chinese-speaking users, evolving from simple droppers to multi-stage chains that misuse signed software and cloud-hosted payloads for evasion. The campaigns registered thousands of disposable domains, hosted payloads on specific IPs and cloud buckets, and employed DLL side-loading and VBScript-based assembly to execute Gh0st RAT via signed binaries. #Gh0stRAT #DLLSideLoading
Keypoints
- Attackers ran two linked campaigns in 2025 (Campaign Trio: Feb–Mar; Campaign Chorus: May onward) targeting Chinese-speaking users with impersonated software lures.
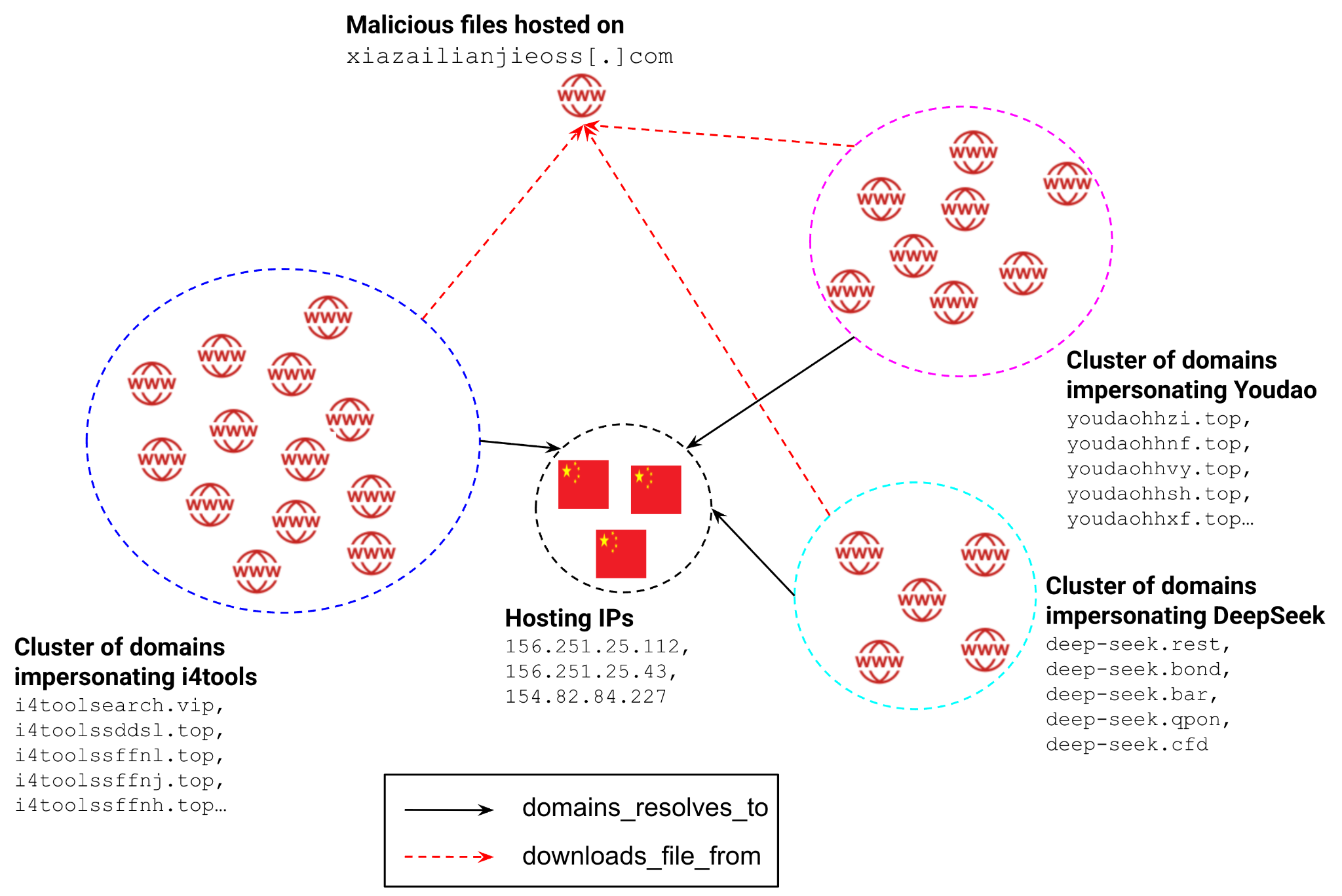
- Over 2,500 domains were programmatically registered (2,000+ in Campaign Trio), many resolving to a small set of core IPs (e.g., 156.251.25[.]112; 95.173.197[.]195).
- Payload delivery shifted from centralized self-hosted ZIP/MSI downloads (xiazailianjieoss[.]com) to cloud-hosted buckets fetched via redirection domains to bypass filters.
- Campaign Trio used MSI installers that executed secondary droppers; final payloads were Gh0st RAT samples that established encrypted TCP C2 on port 8080 and modified Defender exclusions.
- Campaign Chorus introduced a multi-stage chain: embedded VBScript in MSI to assemble/decrypt payload components from .cab parts and then execute via DLL side-loading using a signed wsc_proxy.exe and malicious wsc.dll.
- IOCs include specific hosting IPs, redirection/payload/C2 domains, and SHA256 file hashes for MSI/EXE/DLL artifacts; many domains impersonated popular Chinese apps (Youdao, i4tools, QQ Music, Sogou).
- Operational playbook shows burn-and-churn disposable frontend infrastructure with a two-tier model separating mass impersonation domains from more persistent payload/C2 infrastructure.
MITRE Techniques
- [T1583 ] Acquire Infrastructure – The actor programmatically registered thousands of domains and used multiple hosting IPs to host impersonation sites and C2 infrastructure. Quote: ‘acquired over 2,000 domains and multiple IP addresses to host malicious websites and C2 servers’
- [T1566 ] Phishing – Malicious websites impersonating legitimate software lured users into downloading trojanized installers from mimic download portals. Quote: ‘Malicious websites impersonating legitimate software were used to lure users into downloading trojanized installers’
- [T1204.002 ] User Execution: Malicious File – Victims were induced to execute downloaded MSI or EXE installers which launched multi-stage malware. Quote: ‘The infection chain relies on the user executing a downloaded MSI or EXE file’
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Post-infection PowerShell was used to add Windows Defender exclusions to impair detection. Quote: ‘PowerShell was used post-infection to add Windows Defender exclusions for the malware payload’
- [T1059.005 ] Command and Scripting Interpreter: Visual Basic – VBScript embedded as an MSI custom action assembled and decrypted split payload components into the next-stage binary. Quote: ‘VBScript was embedded as a custom action in MSI installers to act as a multi-stage dropper’
- [T1218.007 ] System Binary Proxy Execution: Msiexec – Malicious MSI installers used msiexec/custom actions to run embedded droppers and bootstrap the infection chain. Quote: ‘Malicious MSI installers were used as the primary delivery vehicle for the initial droppers’
- [T1574.001 ] Hijack Execution Flow: DLL Side-Loading – A signed legitimate executable (wsc_proxy.exe) was placed alongside a malicious wsc.dll so the legitimate binary loaded the attacker’s DLL. Quote: ‘a legitimate, signed AVAST executable (wsc_proxy.exe) was used to load a malicious DLL (wsc.dll) to execute the final payload’
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – Malware added exclusions to Windows Defender to prevent detection of its components. Quote: ‘The malware adds exclusions to Windows Defender to prevent detection of its components’
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 communication used standard TCP/HTTP protocols for command and control traffic. Quote: ‘C2 traffic was observed using standard TCP and HTTP protocols’
- [T1573.001 ] Encrypted Channel: Symmetric Cryptography – C2 channels over TCP port 8080 were encrypted to evade inspection. Quote: ‘C2 communication over TCP port 8080 was encrypted to evade network inspection’
Indicators of Compromise
- [Hosting IP ] Campaign Trio hosting – 156.251.25[.]112, 154.82.84[.]227
- [Hosting IP ] Campaign Chorus hosting – 95.173.197[.]195
- [Payload/C2 Domain ] Download and distribution – xiazailianjieoss[.]com (payload ZIP hosting), fs-im-kefu.7moor-fs1[.]com (malware distribution)
- [Redirection Domain ] Cloud/bucket redirection – yqmqhjgn[.]com, djbzdhygj[.]com
- [C2 Domain/IP ] Command and control – xiaobaituziha[.]com (resolves to 103.181.134[.]138), xiaofeige[.]icu
- [File Hash – MSI/EXE ] Known malicious installers and payloads – 495ea08268fd9cf5… (i4Tools8_v8.33_Setup_x64.msi), 7267a303abb5fcae… (YoudaoDictSetup.msi), and 299e6791e4eb8561… (svchos1.exe / Gh0st RAT)
- [File Hash – DLL/EXE ] Side-loading artifacts – bd4635d582413f84… (wsc_proxy.exe), 1c3f2530b2764754… (wsc.dll)
Read more: https://unit42.paloaltonetworks.com/impersonation-campaigns-deliver-gh0st-rat/