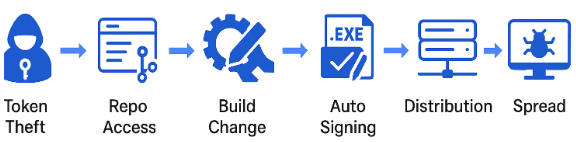
Cato researchers found two default-configuration flaws in Anthropic’s MCP SDK that enable browser-based OAuth token theft, allowing attackers to hijack developer identities and inject malicious code into CI/CD pipelines. The issue can lead to signed, tampered software updates being distributed across vendor-managed supply chains. #AnthropicMCP #CatoCTRL
Keypoints
- Cato CTRL and Cato Application Security discovered two interconnected vulnerabilities in Anthropic’s MCP SDK (v1.10.1) that enable token exfiltration and OAuth hijacking.
- Insecure default CORS configuration (allow_origins=”*”) on /register, /authorize, and /token endpoints allows any website to send cross-origin requests to sensitive OAuth endpoints.
- Unvalidated redirect URIs in the SDK allow attacker-registered clients to set malicious redirect domains (e.g., http://evil.com) and capture authorization tokens.
- A browser-based proof-of-concept demonstrates silent client registration, OAuth flow completion, token exchange, and exfiltration when a logged-in developer visits a malicious page.
- Stolen tokens can grant full repository access (e.g., Bitbucket), enabling repository modification, build tampering, automated signing of malicious binaries, and distribution via vendor update channels.
- The attack leverages benign SDK behavior and permissive defaults rather than a zero-day: a “confused deputy” scenario where trusted automation and identity build a chain of trust abuse.
- Recommended mitigations include strict CORS origin whitelisting, redirect URI validation (restricting schemes/hosts), and applying network-level GenAI security controls (Cato SASE) to monitor and block suspicious MCP activity.
MITRE Techniques
- [T1606] Forge Web Credentials – Exploit of permissive OAuth defaults and unvalidated redirect URIs to obtain valid developer tokens via a malicious webpage: ‘a malicious website takes advantage of the SDK’s permissive defaults… silently registers a rogue client, completes the OAuth flow, and steals a valid developer access token.’
- [T1553] Create or Modify System Process – Using stolen tokens to trigger CI/CD builds and alter build artifacts so automated signing produces malicious binaries: ‘they modify build scripts or source code to embed a malicious payload… the CI/CD pipeline… automatically signs the altered binary.’
- [T1195] Supply Chain Compromise – Abuse of trusted update infrastructure to distribute signed, malicious artifacts to customers via vendor-managed update servers: ‘the signed artifact is published to the vendor’s update or artifact server… customer tenants… install the threat actor’s version.’
- [T1588] Obtain Capabilities via Misconfiguration – Token exfiltration enabled by insecure CORS (allow_origins=”*”) and unvalidated redirect URIs, i.e., leveraging SDK misconfiguration rather than exploit code: ‘This wildcard setting… allows any website to send cross-origin requests… and does not enforce validation by scheme, origin, or host.’
Indicators of Compromise
- [Configuration ] Insecure MCP SDK defaults – allow_origins=”*” on /register, /authorize, /token endpoints (enables cross-origin token requests).
- [Configuration ] Unvalidated redirect URIs – attacker-controlled redirect URI examples such as http://evil.com used to capture tokens.
- [Access Token ] Stolen developer tokens – granted Bitbucket API permissions (used to list, modify, and write repositories) — example context: PoC obtained tokens allowing full Bitbucket API access.
- [Artifact ] Tampered signed binaries – maliciously modified build artifacts signed by CI/CD pipelines and distributed via vendor update servers (example context: signed update delivered to customer tenants).
Read more: https://www.catonetworks.com/blog/cato-ctrl-two-vulnerabilities-in-anthropics-mcp-sdk/