A multi-stage campaign uses malicious Word documents hosted on an open directory at office-theme[.]com to deliver a loader chain that ultimately executes the Comebacker payload in memory, targeting aerospace and defense-related organizations. The malware chain includes VBA droppers, a ChaCha20-decrypted USOPrivate.dll loader, and HTTPS AES-128-CBC C2 communications to hxxps://hiremployee[.]com. #Comebacker #USOPrivate.dll
Keypoints
- Malicious .docx files hosted in an open directory on office-theme[.]com contain VBA macros that decrypt and drop a loader DLL and decoy document when macros are enabled.
- The initial dropper writes a loader to C:ProgramDataWPSOfficewpsoffice_aam.ocx and a decoy document to C:ProgramDataDocumentEDGE_Group_Interview_NDA.docx and then executes the loader via LoadLibraryA.
- The stage 1 loader (wpsoffice_aam.ocx) uses ChaCha20 (static key/IV/counter) and zlib decompression to write C:ProgramDataUSOSharedUSOPrivate.dll and creates a Startup .lnk to execute it via rundll32.exe.
- USOPrivate.dll (stage 2) reuses the same ChaCha20 parameters to decrypt and load the final Comebacker payload directly into memory, calling its GetWindowSizedW export with argument “1282”.
- Comebacker generates a unique victim ID and beacons over HTTPS to hxxps://hiremployee[.]com, encrypting outbound data with AES-128-CBC (same value used for key and IV) and Base64-encoding it.
- The C2 protocol uses structured query strings and a response format that encodes control commands; responses can instruct sleep behavior, termination, or file download-and-execute operations.
- Downloaded payloads are integrity-checked via MD5, decrypted with ChaCha20 using the same static parameters, loaded into memory, executed via a specified export, and results are reported back to the C2.
MITRE Techniques
- [T1204] User Execution – Malicious Word documents require the user to open the .docx and enable macros to trigger the VBA dropper (“When a victim opens one of the malicious .docx files and enables macros, the embedded VBA code executes.”)
- [T1127] Trusted Developer Utilities Proxy Execution – The loader uses rundll32.exe to execute USOPrivate.dll via a Startup shortcut (“$s.TargetPath = ‘C:WindowsSystem32rundll32.exe’; $s.Arguments = ‘”[USOPrivate.dll path]” LoadMimi “C:WindowsSystem32cmd.exe”‘”)
- [T1055] Process Injection – Final Comebacker payload is loaded and executed directly in memory by the loader (USOPrivate.dll loads the final Comebacker payload into memory and transfers execution to it.)
- [T1036] Masquerading – Decoy documents impersonate legitimate organizations (Edge Group, IIT Kanpur, Airbus) to lure targets (“decoy documents leveraging themes related to the aerospace and defense sectors”)
- [T1573] Encrypted Channel – C2 communications use AES-128-CBC and Base64 over HTTPS to conceal data in transit (“All C&C communications occur over HTTPS. The outbound data is first encrypted with AES-128-CBC and then Base64-encoded.”)
- [T1105] Ingress Tool Transfer – Malware can download additional payloads from the C2 server and execute them after integrity checks (“downloads the encrypted file from the C&C server and executes it… calculates the MD5 hash… decrypts the payload using ChaCha20”)
- [T1497] Virtualization/Sandbox Evasion (behavioral) – The C2 can command the malware to sleep, retry, or terminate based on encoded responses to manage timing and avoid detection (“First value is 13 = Terminates process… ‘0’ = Enter a sleep-retry loop… after 20 consecutive ‘0’ responses, the sleep interval increases to 20 minutes”)
Indicators of Compromise
- [Domain] C2 domain – hiremployee[.]com (hardcoded HTTPS C2 server used for beaconing and payload delivery)
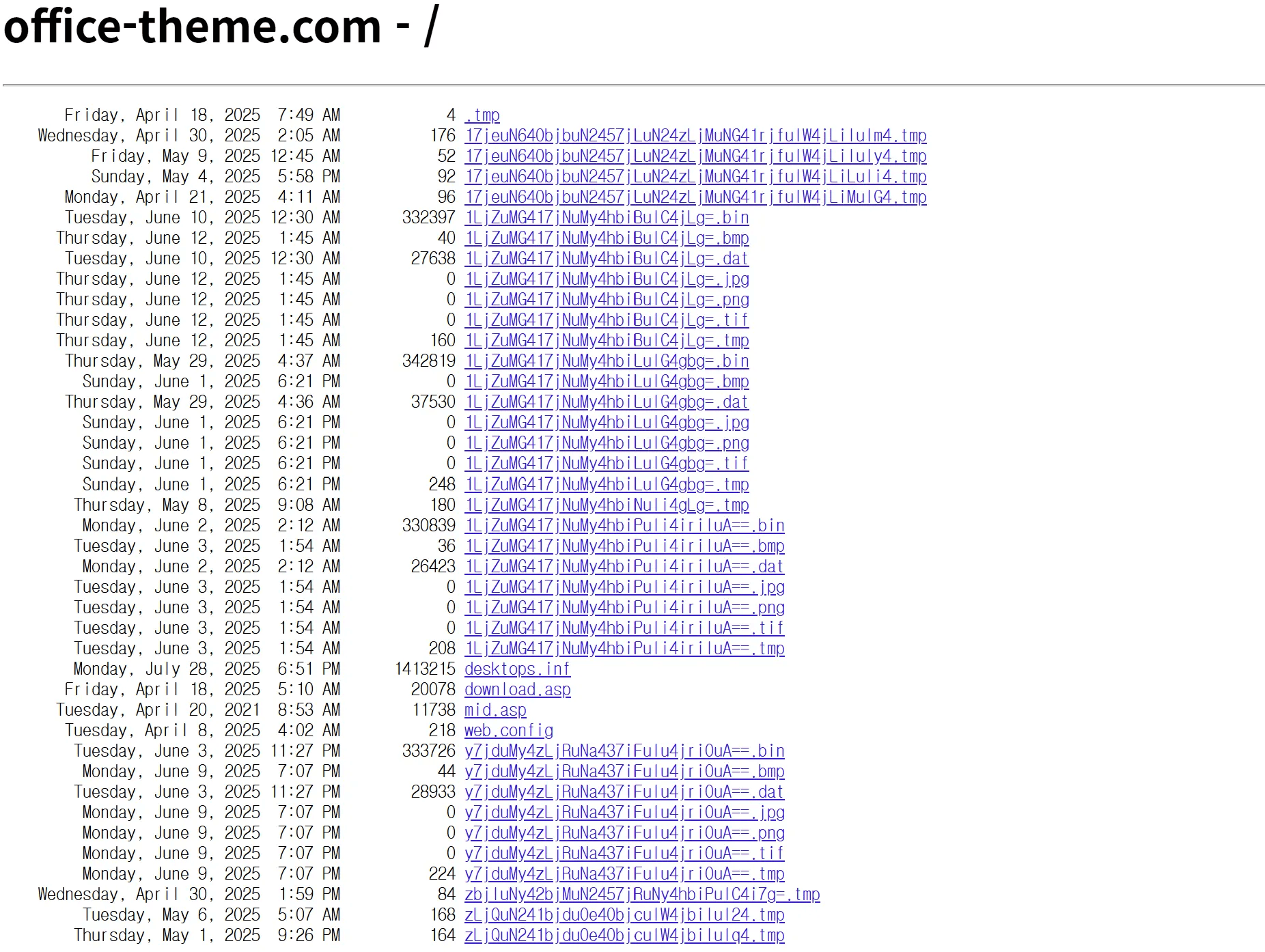
- [Domain] Open directory host – office-theme[.]com (staging/open directory hosting malicious .bin/.docx droppers)
- [File path] Dropped loader/decoy paths – C:ProgramDataWPSOfficewpsoffice_aam.ocx, C:ProgramDataDocumentEDGE_Group_Interview_NDA.docx
- [File path] Stage 2 loader path – C:ProgramDataUSOSharedUSOPrivate.dll (final loader that decrypts and executes Comebacker)
- [Crypto key/IV] Static ChaCha20 parameters – key: ad9c5aca9977d04c73be579199a827049b6dd9840091ffe8e23acc05e1d4a657, iv: edc9ce049daeba35b8687740 (used across loader stages and payload decryption)
- [Encryption material] AES-CBC key/IV (used for C2 traffic) – x!P<&}mjH2YHRQ’ (same value used for both key and IV in C2 encryption)