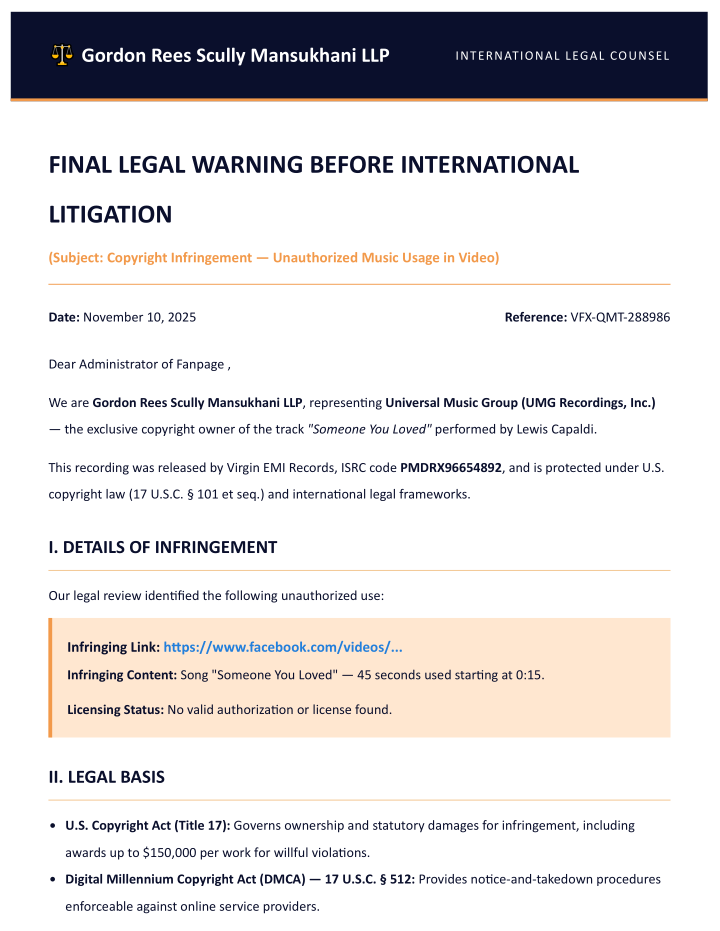
Italian CERT-AGID warned of a phishing campaign impersonating legal notices from Universal Music Group to trick victims into clicking a PDF attachment and submitting Facebook credentials. The attack uses a fake reCAPTCHA and a realistic-looking but fraudulent Facebook login popup to harvest credentials and send them to an attacker C2 server. #UniversalMusicGroup #Facebook
Keypoints
- The campaign delivers emails alleging a copyright violation for the song “Someone You Loved” to pressure recipients into opening an attached PDF titled “Final Legal Warning – Video Copyright”.
- The PDF contains a link that redirects victims to a page mimicking Meta’s environment, including a fake reCAPTCHA to create a sense of legitimacy.
- A simulated browser popup displays a non-interactive URL bar showing “facebook.com” with HTTPS and a padlock, while the underlying page is a phishing form capturing credentials.
- When victims enter email/phone and password and click “Log In”, credentials are transmitted to the attackers’ command-and-control (C2) server.
- CERT-AGID has shared IoCs with accredited organizations and published detected indicators to inform the public.
MITRE Techniques
- [T1222] User Execution – The campaign uses a PDF attachment titled “Final Legal Warning – Video Copyright” to entice users to click a link and proceed to the phishing site (“the mail presents an attachment PDF… containing a link to view the alleged post”).
- [T1192] Spearphishing Link – Emails contain a malicious link in the PDF that redirects the victim to a fraudulent Meta-like page (“once clicked the link, the victim is redirected to a page that reproduces the Meta environment”).
- [T1204] User Execution: Malicious Link – The fake reCAPTCHA and simulated login prompt encourage users to interact and submit credentials (“a fake reCAPTCHA… designed to convey an illusion of legitimacy”).
- [T1531] Account Discovery / Credential Harvesting – The phishing page collects Facebook login credentials (email/phone and password) and sends them to a C2 server (“the data are sent to the attackers’ command and control server”).
- [T1078] Valid Accounts – Stolen Facebook credentials enable use of valid accounts for further malicious activity (credentials harvested from the fake login can be used to access the victim’s Facebook account).
Indicators of Compromise
- [Attachment/File name] Phishing lure – “Final Legal Warning – Video Copyright” PDF attachment (used to deliver the phishing link).
- [URLs/Links] Redirect to fake Meta login – link embedded in the PDF that leads to a fraudulent page mimicking Facebook (specific URL examples were shared with accredited organizations; public report references “Download IoC”).
- [Network/Infrastructure] C2 server – credentials are sent to attackers’ command-and-control server (specific IPs/domains were disclosed to accredited parties and in the IoC download).