Gootloader, a JavaScript-based loader used by Storm-0494 to hand off access to Vanilla Tempest, has resurged with updated evasion including custom WOFF2 glyph-substitution fonts, XOR-encrypted ZIP payloads via compromised WordPress comment endpoints, and Startup-folder persistence enabling rapid reconnaissance and domain controller compromise. Post-intrusion, Vanilla Tempest commonly deploys Supper SOCKS5 backdoor (TextShell-obfuscated) and proceeds with AD enumeration, lateral movement (WinRM), privileged account creation, and ransomware deployment such as Rhysida and BlackCat. #Gootloader #Storm-0494 #Vanilla_Tempest #Supper_backdoor #Rhysida
Keypoints
- Gootloader returns with novel evasion: embedded custom WOFF2 fonts that perform glyph substitution to hide readable filenames in source code.
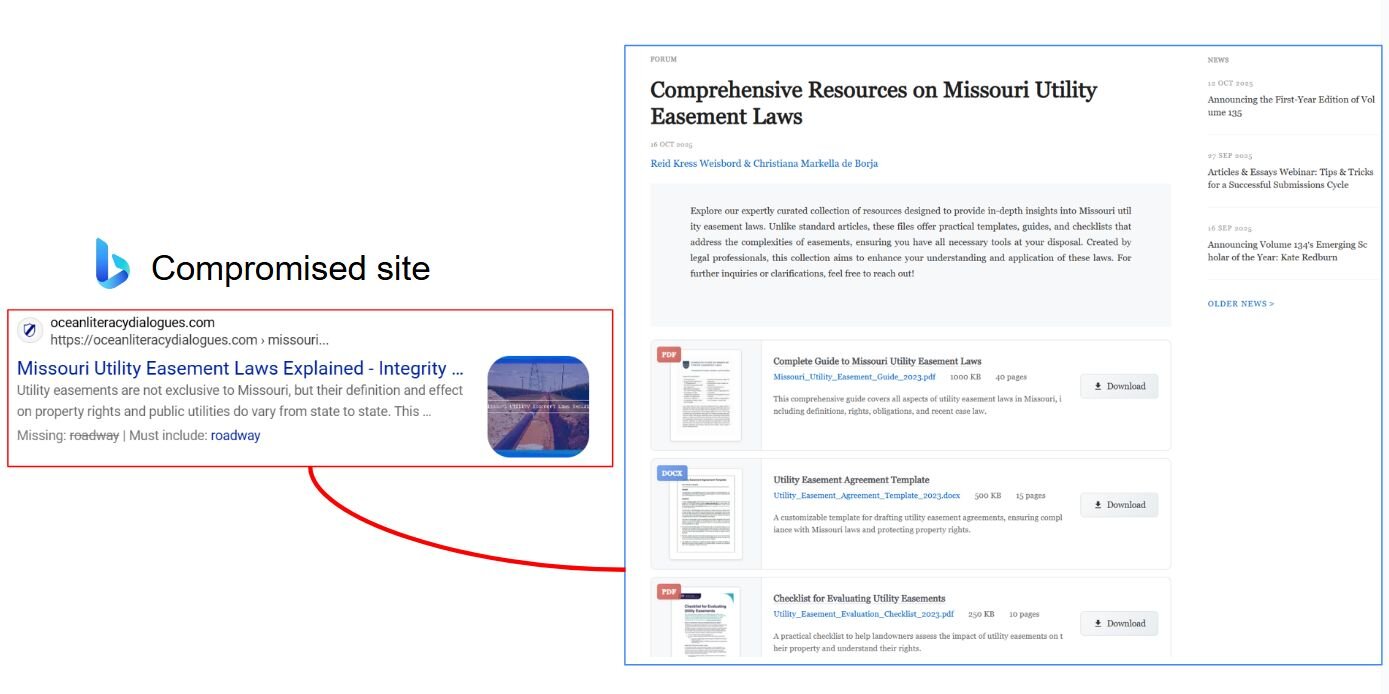
- Initial access delivered via SEO-poisoned compromised sites abusing WordPress /wp-comments-post.php to serve XOR-encrypted ZIP payloads with filename-derived keys.
- Persistence shifted from scheduled tasks to Startup folder shortcuts using Windows 8.3 short filenames; shortcuts launch JavaScript droppers under %AppData%.
- Storm-0494 uses Gootloader for initial access and frequently hands off to Vanilla Tempest (DEV-0832) which deploys Supper backdoor and various ransomware families (e.g., Rhysida, BlackCat).
- Supper SOCKS5 backdoor employs heavy obfuscation: API hammering, runtime shellcode construction, API hashing, and custom 2-byte LZMA header decompression with XOR-based C2 stream cipher.
- Reconnaissance begins within ~20 minutes and Domain Controller compromise can occur in as little as 1–17 hours via repeatable actions: AD enumeration (Kerberoast/SPN), domain-wide local-admin scanning, WinRM lateral movement, and privileged account creation.
- Observed IOCs include multiple JavaScript droppers, SHA256 hashes, hardcoded C2 domains and IPs, and file paths for dropped backdoor artifacts under user AppData and %TEMP%.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Gootloader abuses WordPress comment endpoints (/wp-comments-post.php) to deliver XOR-encrypted ZIP payloads via POST requests: ‘the loader abuses WordPress’s comment submission endpoint (/wp-comments-post.php) to deliver encrypted payloads.’
- [T1204.002] User Execution: Malicious File – Victims click fake “Download” pop-ups triggering JavaScript that serves and decrypts payloads: ‘The user sees a convincing pop-up displaying a download progress indicator… while the site serves an XOR-encrypted ZIP archive.’
- [T1036.005] Masquerading: Match Legitimate Name or Location – Malicious JavaScript masquerades as jQuery v3.0.0 and embeds obfuscated malicious code in noisy string fragments: ‘This JavaScript file masquerades as jQuery v3.0.0 while embedding heavily obfuscated malicious code…’
- [T1059.001] Command and Scripting Interpreter: PowerShell – Second-stage PowerShell beacons, enumerates environment/processes, and executes received commands from C2: ‘we were able to produce a readable second-stage PowerShell script… the script executes received PowerShell commands.’
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Persistence created via Startup folder shortcuts launching JavaScript under %AppData% using Windows 8.3 short filenames: ‘approximately 10-20 minutes later, two persistence mechanisms would be created leveraging Startup folder (T1547.001)…’
- [T1046] Network Service Discovery – Actor performs domain-wide local admin scanning and AD enumeration (SPN scanning) to identify high-value targets: ‘This command scans all domain computers to find where the current user has local admin access.’
- [T1021.006] Lateral Tool Transfer: Windows Remote Management – Lateral movement via WinRM to reach the Domain Controller: ‘the threat actor moved laterally via WinRM (Windows Remote Management) to the Domain Controller.’
- [T1136.001] Create Account: Local Account – Threat actor created local/domain privileged accounts such as sccmad and bpadmin and added them to Domain Admins or Remote Desktop Users: ‘net USER sccmad /ADD … net group “Domain Admins” sccmad /ADD /DOMAIN’.
- [T1003.003] OS Credential Dumping: NTDS – Actor used ntdsutil to dump NTDS.dit on the Domain Controller for potential credential extraction: ‘the threat actor used ntdsutil to dump the NTDS.dit database (T1003.003)’.
- [T1070.001] Indicator Removal on Host: Clear Windows Event Logs – Post-operation cleanup included clearing event logs and deleting Terminal Server client registry keys: ‘performed cleanup activities… including clearing event logs and deleting registry keys related to Terminal Server client connections (T1070.001).’
- [T1105] Ingress Tool Transfer – Deployment of Supper backdoor and proxy DLL on compromised hosts to enable remote control and tunneling: ‘Supper SOCKS5 backdoor is commonly used by Vanilla Tempest. The backdoor has remote control capabilities over compromised hosts and facilitates the tunneling of network traffic.’
Indicators of Compromise
- [File hash] Dropped JavaScript/loader – example SHA256: cf44aa11a17b3dad61cae715f4ea27c0cbf80732a1a7a1c530a5c9d3d183482a, SHA256: ad88076fd75d80e963d07f03d7ae35d4e55bd49634baf92743eece19ec901e94
- [File hash] Secondary droppers – example SHA256: b9a61652dffd2ab3ec3b7e95829759fc43665c27e9642d4b2d4d2f7287254034, SHA256: 2f056ce0657542da3e7e43fb815a8973c354624043f19ef134dff271db1741b3
- [Domain] Compromised sites hosting Gootloader – example hxxps://cortinaspraga.com/, hxxps://filmcrewnepal.com/ (and many other compromised domains listed)
- [IP addresses] C2 servers and backdoor IPs – example 103.253.42[.]91, 91.236.230[.]134 (and additional IPs 213.232.236[.]138, 146.19.49[.]177, 178.32.224[.]219, 37.59.205[.]2, 193.104.58[.]64)
- [File path / filename] Backdoor and droppers on host – example C:UsersusernameAppDataRoamingISIS DriversOutreach Services.lnk (TextShell sample Failover Dependency Zoxsimio.ulb), C:UsersusernameAppDataRoamingNuanceEMC ControlCenter.js
- [Temp file] Backdoor config files – example %TEMP%s01bafg, %TEMP%orl used to store encrypted backup C2 IPs
Read more: https://www.huntress.com/blog/gootloader-threat-detection-woff2-obfuscation