Socket’s Threat Research Team discovered 10 typosquatted npm packages that execute a multi-stage credential stealer via npm’s postinstall hook, using four layers of JavaScript obfuscation, a fake CAPTCHA prompt, IP fingerprinting, and a downloaded 24MB PyInstaller data_extracter binary to harvest credentials across Windows, Linux, and macOS. The campaign’s packages (published July 4, 2025) accumulated over 9,900 downloads, contact the npm registry was made for takedown, and the actor registered packages under the alias andrew_r1 (parvlhonor@gmx[.]com). #data_extracter #andrew_r1
Keypoints
- Ten malicious, typosquatted npm packages were published on July 4, 2025 and amassed over 9,900 downloads before being reported to the npm registry.
- Each package uses npm’s postinstall script to spawn a new terminal and run an obfuscated app.js that displays a fake CAPTCHA to socially engineer users and delay detection.
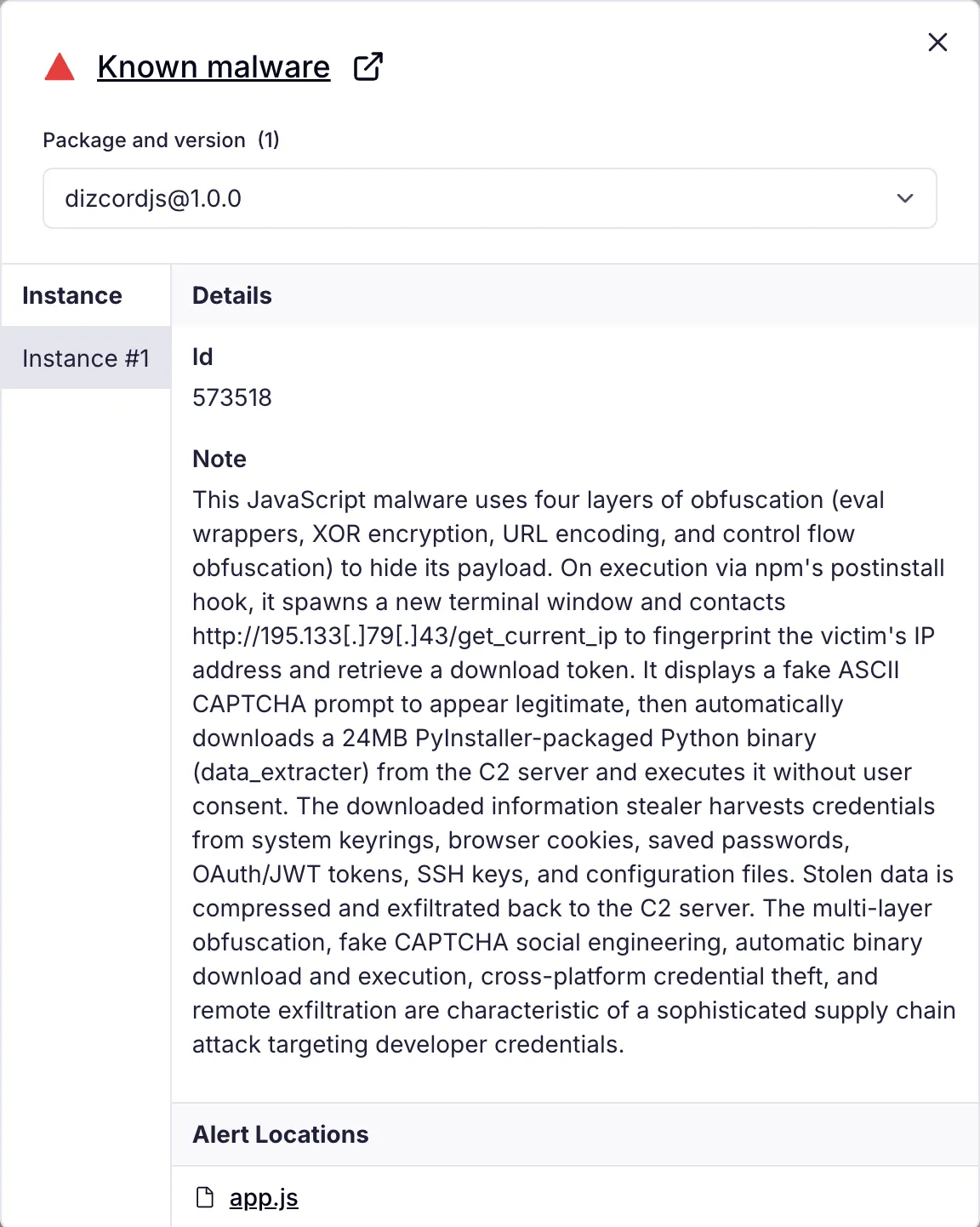
- app.js implements four obfuscation layers — eval wrapping, XOR decryption with a dynamic key, URL encoding, and control-flow obfuscation — to evade static analysis.
- The malware fingerprints victims by sending their IP to 195[.]133[.]79[.]43 before downloading a platform-specific 24MB PyInstaller binary named data_extracter which performs credential theft.
- data_extracter targets system keyrings, browsers (cookies and saved passwords), SSH keys, cloud config files (AWS, kube, Docker), OAuth/JWT tokens, and other credential stores, then compresses and exfiltrates them to the C2 server.
- Evidence includes a SHA256 for the binary (80552ce00e5d271da870e96207541a4f82a782e7b7f4690baeca5d411ed71edb), network requests to 195[.]133[.]79[.]43, and package names registered by npm alias andrew_r1 (parvlhonor@gmx[.]com).
- Recommended remediation: assume compromise if installed, rotate all credentials and tokens, enable MFA, audit access logs and lateral movement, block and monitor connections to 195[.]133[.]79[.]43, and deploy supply-chain defenses such as dependency scanning and runtime blocking.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – Malicious packages were published to npm under typosquatted names to deliver malware via package installation. Quote: “Socket’s Threat Research Team discovered 10 malicious npm packages…”
- [T1027 ] Obfuscated Files or Information – The JavaScript payload uses multiple obfuscation layers (eval wrapper, XOR, URL encoding, control-flow obfuscation) to hide behavior. Quote: “…four layers of obfuscation to hide its payload…”
- [T1027.002 ] Software Packing – The PyInstaller-packaged Python binary bundles the malware and libraries into a single executable to avoid detection. Quote: “PyInstaller bundles Python, all required libraries, and the malicious code into a single executable…”
- [T1204.002 ] User Execution: Malicious File – The postinstall hook spawns a terminal and displays a fake CAPTCHA to elicit user interaction and delay detection. Quote: “displays a fake CAPTCHA to appear legitimate”
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – The malicious code executes JavaScript (node app.js) from npm postinstall to run the payload. Quote: “postinstall’: ‘node install.js’ … exec(‘start cmd /k “node app.js”‘)”
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – The installer spawns platform-specific shells/terminals (gnome-terminal, x-terminal-emulator, osascript for Terminal.app) to run the payload. Quote: “exec(‘gnome-terminal — bash -c “node app.js”‘ … exec(‘x-terminal-emulator -e “bash -c ‘node app.js’”‘))”
- [T1059.006 ] Command and Scripting Interpreter: Python – The attacker delivers a Python-based PyInstaller binary (data_extracter) that executes Python code to harvest credentials. Quote: “data_extracter binary … PyInstaller-packaged Python application”
- [T1555 ] Credentials from Password Stores – The binary extracts credentials from OS keyrings (Windows Credential Manager, macOS Keychain, Linux SecretService/KWallet). Quote: “harvests credentials from system keyrings … Windows Credential Manager … Keychain Services API … SecretService D-Bus API”
- [T1555.003 ] Credentials from Web Browsers – The malware extracts saved passwords and cookies from Firefox and Chromium-based browsers. Quote: “Browser session cookies … Saved passwords from browser password managers”
- [T1555.001 ] Credentials from Keychain – Targets platform keychain APIs to retrieve stored secrets in decrypted form. Quote: “macOS: Keychain Services API”
- [T1539 ] Steal Web Session Cookie – The malware extracts browser session cookies to impersonate users and bypass MFA. Quote: “Browser cookies are particularly valuable because they contain active session tokens.”
- [T1552.001 ] Unsecured Credentials: Credentials In Files – The malware scans for plaintext config files (e.g., .env, .npmrc, .pypirc) and cloud credential files (AWS, kube, Docker). Quote: “~/.aws/credentials, ~/.kube/config, ~/.docker/config.json”
- [T1552.004 ] Unsecured Credentials: Private Keys – The malware searches for private SSH keys in ~/.ssh (id_rsa, id_ed25519) for repository and server access. Quote: “SSH key directories (~/.ssh/ containing id_rsa, id_ed25519)”
- [T1071.001 ] Application Layer Protocol: Web Protocols – The malware communicates with the attacker’s server over HTTP to fingerprint IP and exfiltrate data. Quote: “sends the victim’s IP address to … http://195[.]133[.]79[.]43/get_current_ip”
- [T1041 ] Exfiltration Over C2 Channel – Stolen credential archives are compressed and exfiltrated to the C2 server at 195[.]133[.]79[.]43. Quote: “This compressed archive is then transmitted back to the threat actor’s server at 195[.]133[.]79[.]43”
- [T1560.001 ] Archive Collected Data: Archive via Utility – The malware compresses collected credentials into ZIP archives in temporary directories for staging before exfiltration. Quote: “ZIP file creation and compression for collected credentials … Temporary file creation in /var/tmp, /usr/tmp”
- [T1027.009 ] Obfuscated Files or Information: Embedded Payloads – The app.js embeds multi-stage encoded payloads (URL-encoded strings decoded at runtime) requiring runtime evaluation to reveal. Quote: “The payload string is URL-encoded (%5E%0A%03%03%0D%15…), requiring URI decoding before XOR decryption.”
- [T1140 ] Deobfuscate/Decode Files or Information – The malware performs runtime decoding/deobfuscation (URI decoding, XOR decryption, eval) to reconstruct executable code. Quote: “The outermost layer wraps the entire payload … that reconstructs and evaluates itself”
- [T1082 ] System Information Discovery – The installer queries os.platform() to detect victim OS and select appropriate binary. Quote: “install.js script detects the victim’s operating system … const platform = os.platform();”
- [T1083 ] File and Directory Discovery – The binary performs recursive directory traversal (readdir, opendir) to locate credential files and browser profiles. Quote: “readdir, opendir for recursive directory scanning … ~/.mozilla/firefox/, ~/.config/google-chrome/”
Indicators of Compromise
- [Malicious npm Packages ] typosquatted package names used to distribute the malware – deezcord.js, dezcord.js (and 8 more packages listed in IOC section)
- [Network Infrastructure ] C2 server and payload hosting – 195[.]133[.]79[.]43 (GET /get_current_ip, /data_extracter)
- [File Hash ] primary malware binary SHA256 – 80552ce00e5d271da870e96207541a4f82a782e7b7f4690baeca5d411ed71edb (data_extracter)
- [File Name ] downloaded PyInstaller binary name – data_extracter (24MB PyInstaller-packed executable)
- [Threat Actor Identifiers ] package author alias and contact – npm alias: andrew_r1; email: parvlhonor@gmx[.]com
Read more: https://socket.dev/blog/10-npm-typosquatted-packages-deploy-credential-harvester