XLab discovered RPX_Client, a previously undocumented PolarEdge relay component that onboards compromised IoT/edge devices into a proxy pool and enables remote command execution, linked to download infrastructure at 111.119.223.196 and corroborated by homology with known PolarEdge samples. The investigation identified 140 RPX_Server VPS nodes (port 55555) and over 25,000 infected devices across 40 countries, revealing an ORB network used for long-term stealth and traffic obfuscation. #PolarEdge #RPX_Client
Keypoints
- XLab detected IP 111.119.223.196 distributing an ELF named “w”, leading to discovery of RPX_Client, a PolarEdge relay component that enrolls compromised devices into a proxy pool.
- Correlation with scripts and sample homology links RPX_Client/RPX_Server to PolarEdge; 82.118.22.155 is identified as a historical downloader server tied to PolarEdge C2s.
- RPX_Server infrastructure: 140 confirmed VPS nodes (port 55555) concentrated in ASNs 45102, 37963, and 132203, hosted on Alibaba Cloud and Tencent Cloud.
- RPX_Client was found on 25,000+ infected devices across 40 countries (top affected: South Korea, China, Thailand) and primarily affects ktcctv and tvt device families.
- RPX system components: RPX_Server (proxy gateway), Go-Admin (management, session validation, Clash export), Nginx (reverse proxy), and Go-Shadowsocks (proxy service).
- RPX_Client uses .fccq encrypted config (XOR 0x25), registers on port 55555 for proxying, and connects to port 55560 for remote command execution (UUID-based authentication).
- RPX design provides multi-hop reverse-connection proxying that obscures true source IPs, undermining traditional IOC-based detection and attribution.
MITRE Techniques
- [T1525 ] Compromise of network infrastructure – RPX_Client and RPX_Server establish and manage an ORB/proxy network to hide source and relay traffic (“…adds the compromised device to the ORB network…”).
- [T1105 ] Ingress tool transfer – ELF file “w” and wget.tar were distributed and executed on target devices to deploy RPX_Client (“…distributed an ELF file named ‘w’… wget.tar archive contains rpx and rpx.sh”).
- [T1543 ] Create or modify system process – RPX_Client disguises process name as connect_server and uses /tmp/.msc PID file to enforce single-instance execution (“…disguises its process name as connect_server and uses the PID file /tmp/.msc…”).
- [T1112 ] Modify registry (or system configuration) / Persistence – rpx.sh is injected into /etc/init.d/rcS to achieve persistence (“echo “/bin/sh /mnt/mtd/rpx.sh &” >> /etc/init.d/rcS”).
- [T1572 ] Protocol Tunneling and Proxy – RPX_Server schedules registered proxy nodes to connect to targets and creates multi-hop proxy chains (Local proxy ←→ RPX Server ←→ RPX Client ←→ ipinfo.io) to obscure origin (“…schedules a registered proxy node to connect to the target… establishes a reverse connection back to a dynamically allocated temporary port on the gateway”).
- [T1041 ] Exfiltration over C2 channel (bidirectional C2) – RPX_Client maintains two persistent connections: one for registration/proxying (port 55555) and one for remote command execution (port 55560) to receive/execute commands (“…establishes two independent network connections to the C2 server…”).
- [T1106 ] Native API – Remote command execution and built-in commands (change_pub_ip, update_vps) enable operators to reconfigure and upgrade deployed clients (“…includes two special built-in commands: change_pub_ip – updates the C2 server address; update_vps – performs sample self-upgrade”).
Indicators of Compromise
- [IP Address ] download and C2 context – 111.119.223.196 (Singapore, AS136907 HUAWEI) distributed ELF “w” and hosted scripts; 82.118.22.155 (Poland, AS204957) acted as a historical downloader.
- [IP Address ] RPX Server nodes – examples: 47.79.7.193 (AS45102), 8.216.14.9 (AS45102) and 138 other confirmed RPX Server IPs (total 140 confirmed nodes).
- [File Name ] payload and persistence context – w (ELF downloader/connect-back module), rpx (RPX_Client binary), rpx.sh (persistence script).
- [Hashes ] sample and script context – RPX_Client: 7fa5fb15098efdf76e4c016e2e17bb38, additional RPX_Client: 571088182ed7e33d986b3aa2c51efd27; script q: 96b3be4cf3ad232ca456f343f468da0e; RPX_Server: 1fb2dfb09a31f0e8c63cc83283532f06.
- [Domain ] PolarEdge backdoor C2 context – beastdositadvtofm[.]site, missionim[.]cc, icecreand[.]cc, centrequ[.]cc (domains observed in PDNS and C2 configs).
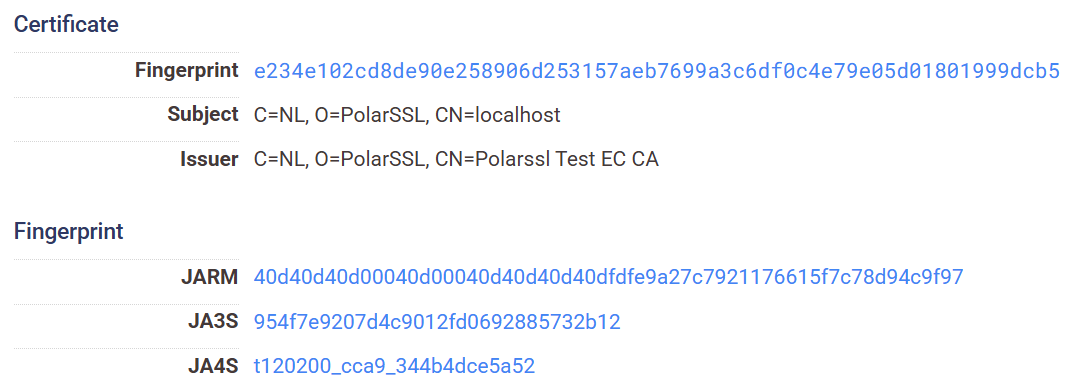
- [Certificate Fingerprint ] RPX Server / Nginx context – e234e102cd8de90e258906d253157aeb7699a3c6df0c4e79e05d01801999dcb5 (RPX_Server cert), 3f00058448b8f7e9a296d0cdf6567ceb23895345eae39d472350a27b24efe999 (Nginx cert).
Read more: https://blog.xlab.qianxin.com/smoking-gun-uncovered-rpx-relay-at-polaredges-core-exposed/