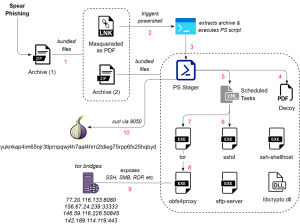
SEQRITE Labs identified a campaign called SkyCloak targeting Russian and Belarusian military personnel that uses spearphishing LNKs to execute PowerShell stages which deploy OpenSSH and Tor (with obfs4 bridges) to expose local services via onion addresses. The chain uses scheduled tasks for persistence, bundles legitimate OpenSSH/OpenSSL binaries for a stealthy SSH/SFTP server, and registers victims to yuknkap4im65njr3tlprnpqwj4h7aal4hrn2tdieg75rpp6fx25hqbyd.onion. #SkyCloak #yuknkap4im65njr3tlprnpqwj4h7aal4hrn2tdieg75rpp6fx25hqbyd.onion
Keypoints
- Targets military personnel of Russia and Belarus, specifically Russian Airborne Forces and Belarusian Special Forces, using decoy nomination and training letters.
- Initial access via spearphishing ZIPs containing double-extension LNK shortcuts that trigger PowerShell droppers and multi-stage archive extraction.
- PowerShell stager performs anti-analysis checks (Recent folder count, process count), creates mutex, reads XML task definitions, and concatenates strings to form an onion address for beaconing via local Tor SOCKS (port 9050).
- Persistence established through hidden scheduled tasks defined by XML files that run daily and on demand, launching deployed binaries from %AppData% paths.
- Attackers deploy a self-contained OpenSSH server (renamed binaries like githubdesktop.exe, googlemaps.exe, ssh-shellhost.exe) inside user profile directories and configure SSH to require public-key auth on port 20321.
- Tor is used with obfs4 pluggable transport (renamed obfs4proxy binaries confluence.exe/rider.exe) and bridges to hide outbound connections and expose multiple local services (SSH, SMB, RDP) as hidden services.
- Infrastructure includes specific Tor bridges and an onion registration address; attribution remains low-confidence though overlaps with Eastern European APT patterns are noted and SkyCloak remains unattributed.
MITRE Techniques
- [T1583 ] Acquire Infrastructure – The campaign configures Tor bridges, obfs4 proxies and an onion service to host command-and-control: ‘HiddenServiceDir “socketExecutingLoggingIncrementalCompiler/”‘ and Bridge entries for obfs4 endpoints.
- [T1566.001 ] Phishing: Spearphishing Attachment – Initial delivery via spearphishing ZIPs with decoy nomination/training documents and LNK shortcuts (‘The first lure is a nomination letter … The second decoy letter …’).
- [T1204.002 ] User Execution: Malicious File – Victims are lured to open decoy documents and execute shortcut-triggered payloads (‘Shortcut files … trigger PowerShell commands which act as the initial dropper stage’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell scripts perform extraction, anti-analysis checks, task registration, and beaconing via Tor (‘The command extracts the first archive … triggers PowerShell’, ‘The script starts by checking the Windows ‘Recent’ folder’).
- [T1106 ] Native API – Legitimate OpenSSH/OpenSSL binaries are used and launched with configuration arguments, leveraging native Windows services/APIs for SSH/SFTP functionality (‘legitimate “OpenSSH for Windows” binaries … PDB paths’).
- [T1053.005 ] Scheduled Task – Persistence via Windows scheduled task XML files that run daily and on demand (‘XML files are Windows scheduled task definitions that runs daily … These tasks are hidden and configured to run even when the computer is idle’).
- [T1547 ] Boot or Logon Autostart Execution – Attack sets tasks with logon triggers and hidden configuration to persist across logons (‘has a logon trigger for the user specified’).
- [T1027 ] Obfuscated Files or Information – Strings are concatenated and XMLs/text files are used to hide configuration and create onion addresses, adding obfuscation to operations (‘Multiple strings are concatenated to form the full onion address’).
- [T1036 ] Masquerading – Renaming legitimate binaries (ssh, sftp, tor, obfs4proxy) to benign names like githubdesktop.exe, googlemaps.exe, pinterest.exe to evade detection (‘githubdesktop.exe … pinterest.exe … confluence.exe renamed obfs4proxy’).
- [T1497 ] Virtualization/Sandbox Evasion – PowerShell checks Recent folder and process count to detect sandboxed environments and avoid execution (‘The script starts by checking the Windows ‘Recent’ folder and if it has more than ten shortcut files … Another check is done to see if the process count is greater than 50’).
- [T1083 ] File and Directory Discovery – Stager inspects folders (Recent, various AppData directories) and reads/writes hostname file written by Tor (‘The script starts by checking the Windows ‘Recent’ folder’ and ‘it waits until the hostname file exists’).
- [T1046 ] Network Service Discovery – Configuration exposes local services (SSH, SMB, RDP) via Tor hidden service ports to enable remote access (‘HiddenServicePort … 127.0.0.1:445 … 127.0.0.1:3389’).
- [T1033 ] System Owner/User Discovery – The beacon format includes username and onion address to identify infected host (‘creates an identification beacon in a specific format ‘::3-yeeifyem’’).
- [T1021 ] Remote Services – Deployment of OpenSSH and exposing ports over Tor enables remote services for lateral movement and administration (‘deploys a self-contained OpenSSH server inside a user’s profile directory using Tor’).
- [T1119 ] Automated Collection – The deployed SSH/SFTP services and configured subsystems can support automated data collection and transfer over the Tor channel (use of SFTP subsystem and authorized keys files in configuration).
- [T1071 ] Application Layer Protocol – Use of HTTP-like application-layer communication via curl over Tor SOCKS for beaconing and C2 (‘uses curl via local Tor SOCKS listener on port 9050’).
- [T1090 ] Proxy – Use of Tor and obfs4 bridges acts as a proxying technique to hide C2 communications (‘creates an onion service and exposes SSH, SMB, RDP and other ports over Tor’ and ClientTransportPlugin obfs4 entries).
- [T1571 ] Non-Standard Port – SSH listens on non-standard port 20321 internally and hidden-service ports map to non-standard ports for exposed services (‘Port 20321 … HiddenServicePort 20322 127.0.0.1:20321’).
- [T1041 ] Exfiltration Over C2 Channel – The Tor-hidden service with SSH/SFTP and automated beaconing implies use of C2 channels for potential exfiltration (‘creates an identification beacon … uses curl via local Tor SOCKS listener’ and SFTP subsystem present).
Indicators of Compromise
- [Archive (ZIP) ] Phishing archives uploaded from Belarus – 952f86861feeaf9821685cc203d67004 (ТЛГ на убытие на переподготовку.pdf), d246dfa9e274c644c5a9862350641bac (persistentHandlerHashingEncodingScalable.zip).
- [Shortcut (LNK) ] Weaponized LNK shortcuts triggering PowerShell – 32bdbf5c26e691cbbd451545bca52b56 (ТЛГ на убытие на переподготовку.pdf.lnk), 2731b3e8524e523a84dc7374ae29ac23 (Исх №6626 … .pdf.lnk).
- [PowerShell (PS1) ] Stager scripts – 39937e199b2377d1f212510f1f2f7653 (scalingEncryptingEncoding.ps1), 9242b49e9581fa7f2100bd9ad4385e8c (responsiveHashingSocketScalableDeterministic.ps1).
- [XML ] Scheduled task and persistence XMLs – b61a80800a1021e9d0b1f5e8524c5708 (loadingBufferFunctionHashing.xml), b52dfb562c1093a87b78ffb6bfc78e07 (incrementalRedundantRendering.xml).
- [PE (EXE/DLL) ] Renamed legitimate binaries used for SSH/Tor/obfs4 – f6c0304671c4485c04d4a1c7c8c8ed94 (githubdesktop.exe / googlemaps.exe – sshd), cdd065c52b96614dc880273f2872619f (pinterest.exe / googlesheets.exe – tor.exe), 664f09734b07659a6f75bca3866ae5e8 (confluence.exe / rider.exe – obfs4proxy.exe), and libcrypto.dll (664f097… listed separately).
- [Text / Key files ] SSH key and config filenames in AppData – redundantOptimizingInstanceVariableLogging, redundantExecutingContainerIndexing, incrementalMergingIncrementalImmutableProtocol (private/pub keys and authorized_keys files).
- [Network / Tor ] Tor bridges and onion address – 77.20.116.133:8080, 156.67.24.239:33333 (bridge endpoints) and yuknkap4im65njr3tlprnpqwj4h7aal4hrn2tdieg75rpp6fx25hqbyd.onion (registration beacon).
Read more: https://www.seqrite.com/blog/operation-skycloak-tor-campaign-targets-military-of-russia-belarus/