Threat actors used malicious SVG image attachments in phishing emails to gain remote control of victims’ devices, collect sensitive information, and deliver additional malware, with FortiGuard Labs identifying 26 IoCs (25 domains and one IP). Investigations revealed domain registration and resolution patterns, connections to multiple IPs and email-linked domains, and early detection indicators from threat feeds and WHOIS/DNS data. #ms-team-ping2[.]com #109.176.207.110
Keypoints
- Attackers distributed malicious SVG files via email attachments instead of typical PNG/JPG images to execute remote control and further payload delivery.
- FortiGuard Labs identified 26 IoCs: 25 domains and one IP address (109.176.207.110) tied to the campaign.
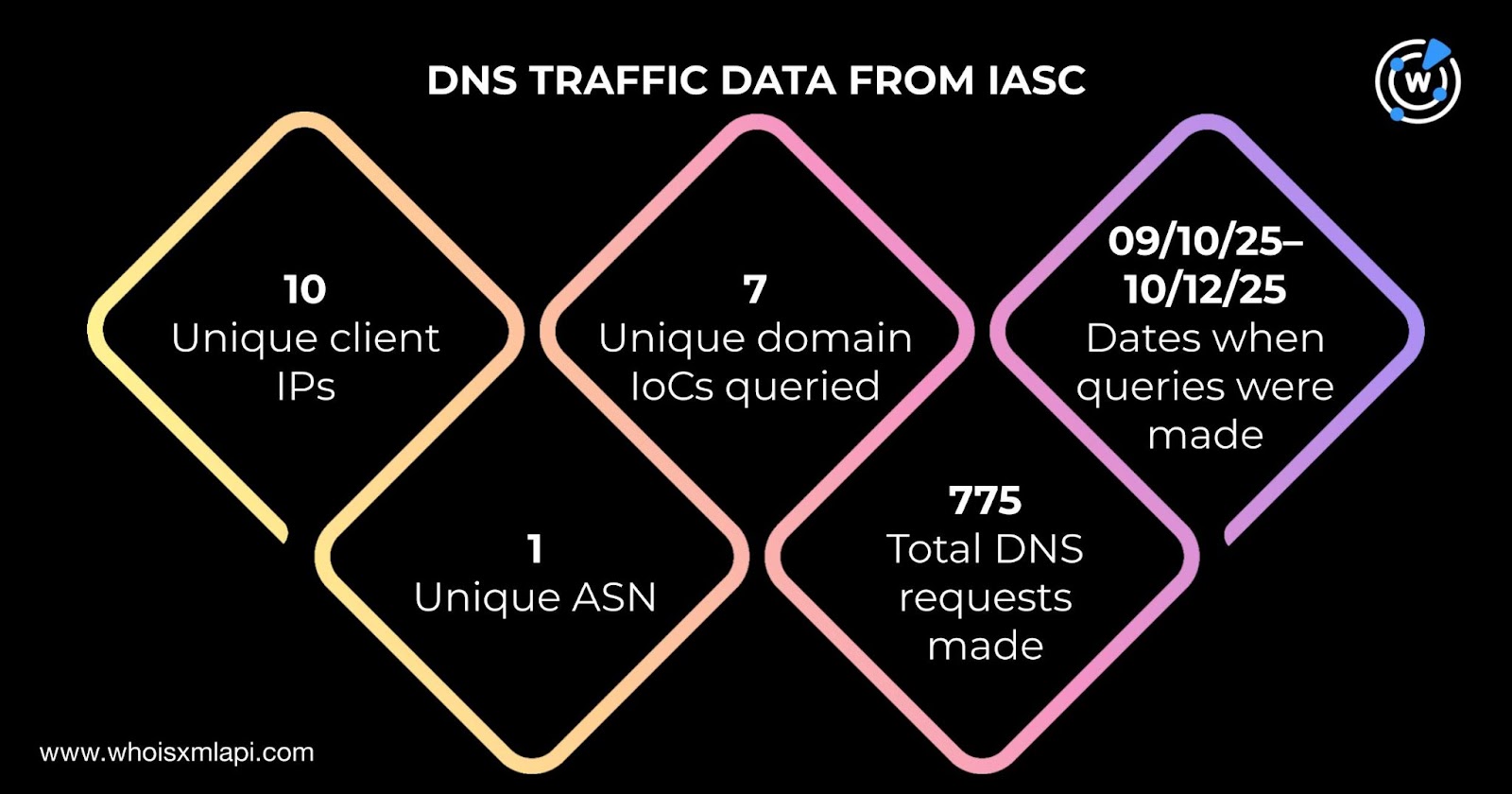
- IASC network traffic showed 10 unique client IPs communicated with seven IoC domains via 775 DNS queries between 10 Sep and 12 Oct 2025, all under one ASN.
- WhoisXML/First Watch data indicated nine domains were flagged as likely to turn malicious 14–105 days before formal reporting, with specific examples such as ms-team-ping2[.]com.
- WHOIS queries found 13 domains with current records; 11 were created in 2025 while two dated from 2005 and 2018; NiceNIC International Group registered eight of the domains.
- DNS Chronicle showed 13 of the domains had 1,124 domain-to-IP resolutions in total, with acqua-tecnica[.]it having 297 resolutions dating back to 2017.
- Additional artifact discovery yielded 22 email-connected domains and 18 additional malicious IPs; all 18 were associated with previous malicious campaigns.
MITRE Techniques
- [T1193] Spearphishing Attachment – Malicious SVG image attachments were sent in phishing emails to deliver and execute remote-control malware (“malware-laced Scalable Vector Graphics (SVG) in place of the typical PNG or JPG files”).
- [T1204] User Execution – The attack relied on recipients opening image attachments (SVG files) to trigger the malicious behavior (“email-image file attachment combo … distributed malware-laced Scalable Vector Graphics (SVG)”).
- [T1071] Application Layer Protocol – DNS queries and domain communications were used for C2 or artifact retrieval, as evidenced by “775 DNS queries” and numerous domain-to-IP resolutions in DNS Chronicle data.
- [T1588] Obtain Capabilities – Domains and IP infrastructure were registered and used to host or deliver malware, indicated by registration and resolution records for 25 domains and one IP (“FortiGuard Labs identified 26 indicators of compromise (IoCs) comprising 25 domains and one IP address”).
- [T1087] Account Discovery (WHOIS/Email Harvesting) – Historical WHOIS and Reverse WHOIS queries uncovered public email address reuse and 22 email-connected domains, enabling expansion of the artifact set (“a public email address in the historical WHOIS record” and “22 email-connected domains”).
Indicators of Compromise
- [Domain ] Identified malicious domains associated with the campaign – ms-team-ping2[.]com, ms-team-ping3[.]com, and 22 other domains (total 25 domains).
- [IP Address ] Primary IoC IP geolocated and associated ISP – 109.176.207.110 (Nasstar, Netherlands); plus 18 additional malicious IPs discovered via Threat Intelligence API.
- [Domain-to-IP Resolutions ] High-resolution counts showing historical mappings – acqua-tecnica[.]it (297 resolutions), phuyufact[.]com (240 resolutions), and other domain-to-IP records totaling 1,124 resolutions.
- [WHOIS Registrars ] Registrar metadata linked to IoCs – NiceNIC International Group (8 domains), Web Commerce Communications (3 domains), and others from Aruba Business and NetEarth One.
- [Email-Connected Domains ] Domains discovered via Reverse WHOIS from a public WHOIS email – 22 email-connected domains related to the campaign (examples available in analysis artifacts).
Read more: https://circleid.com/posts/spelunking-into-svg-phishing-amatera-stealer-and-pureminer-dns-deep-dive