Salt Typhoon (aka Earth Estries / GhostEmperor / UNC2286) is a state-linked APT active since at least 2019 that has targeted telecoms, energy, and government systems worldwide using zero-day exploits, DLL sideloading, custom backdoors (SNAPPYBEE/Deed RAT), and obfuscated C2 channels. Darktrace observed a July 2025 intrusion against a European telco exploiting CVE-2025-5777 on Citrix NetScaler, delivering SNAPPYBEE via DLL side-loading and communicating with C2 domains such as aar.gandhibludtric[.]com. #SaltTyphoon #SNAPPYBEE
Keypoints
- Salt Typhoon is a highly persistent state-linked APT active since at least 2019 with global targeting across telecoms, energy, and government networks.
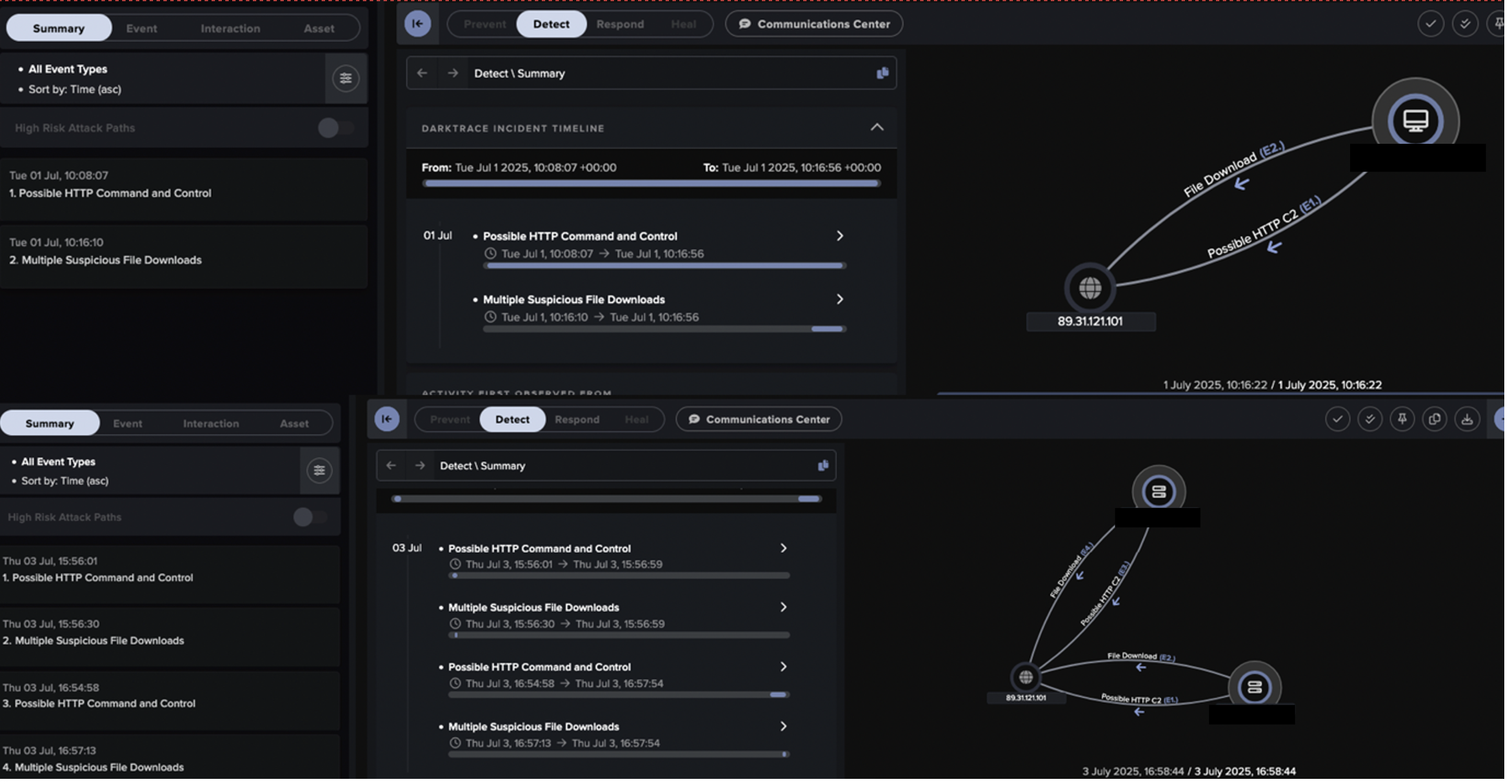
- Darktrace detected an intrusion in July 2025 that began with exploitation of CVE-2025-5777 affecting Citrix NetScaler Gateway appliances.
- The actor pivoted to Citrix VDA hosts in an MCS subnet and likely used SoftEther VPN-related infrastructure to obscure initial access and staging.
- Attackers delivered the SNAPPYBEE (Deed RAT) backdoor to internal hosts via DLL side-loading paired with legitimate antivirus executables (e.g., Norton, Bkav, IObit).
- C2 communications used both HTTP (with IE User-Agent and URIs like /17ABE7F017ABE7F0) and an unidentified TCP-based protocol, contacting domains such as aar.gandhibludtric[.]com (38.54.63[.]75).
- Darktrace’s Cyber AI Analyst and detection models produced high-confidence alerts that enabled early discovery and remediation before wider escalation.
- Assessment links the activity to Salt Typhoon/Earth Estries based on overlaps in TTPs, infrastructure, and malware, underscoring the need for anomaly-based detection.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Compromised Citrix NetScaler Gateway via CVE-2025-5777; “…exploitation of CVE-2025-5777, a vulnerability affecting Citrix NetScaler Gateway appliances…”
- [T1105 ] Ingress Tool Transfer – Delivery of backdoor to internal Citrix VDA hosts as DLL payloads; “…delivering a backdoor assessed with high confidence to be SNAPPYBEE…to multiple Citrix VDA hosts.”
- [T1665 ] Hide Infrastructure – Use of SoftEther VPN-related endpoint suggesting infrastructure obfuscation for initial access/C2 staging; “…originated from an endpoint potentially associated with the SoftEther VPN service, suggesting infrastructure obfuscation…”
- [T1574.001 ] Hijack Execution Flow: DLL – Execution through DLL side-loading using legitimate antivirus executables (Norton, Bkav, IObit); “…delivered to these internal endpoints as a DLL alongside legitimate executable files for antivirus software…indicates…DLL side-loading…”
- [T1095 ] Non-Application Layer Protocol – Use of an unidentified TCP-based protocol for C2 communications alongside HTTP; “…communicating over both HTTP and an unidentified TCP-based protocol.”
- [T1071.001 ] Web Protocols – HTTP-based C2 using POST requests with Internet Explorer User-Agent and URI patterns like /17ABE7F017ABE7F0; “The HTTP communications displayed by the backdoor included POST requests with an Internet Explorer User-Agent header and Target URI patterns such as ‘/17ABE7F017ABE7F0’.”
- [T1571 ] Non-Standard Port – Use of port 443 for unencrypted HTTP traffic to evade detection; “Port 443 for unencrypted HTTP traffic” (noted in MITRE list and observed URIs on :443).
Indicators of Compromise
- [IP ] Possible C2 and staging – 89.31.121[.]101 (C2/staging hosting multiple payload URIs), 38.54.63[.]75 (aar.gandhibludtric[.]com C2)
- [Domain ] C2 hostname – aar.gandhibludtric[.]com – linked to Salt Typhoon activity
- [URI / filenames ] Likely payloads and side-loading artifacts – hxxp://89.31.121[.]101:443/WINMM.dll, hxxp://89.31.121[.]101:443/DgApi.dll (DLLs and executables used for side-loading)
- [File hash ] Malware sample – b5367820cd32640a2d5e4c3a3c1ceedbbb715be2 (SHA1) – likely SNAPPYBEE download
- [URI ] C2 callback pattern – hxxp://156.244.28[.]153/17ABE7F017ABE7F0 and hxxp://89.31.121[.]101:443/17ABE7F017ABE7F0 (observed C2 request URIs)
Read more: https://www.darktrace.com/blog/salty-much-darktraces-view-on-a-recent-salt-typhoon-intrusion