CyberProof observed a surge in a Remcos infostealer campaign in Sep–Oct 2025 that used malicious email attachments, obfuscated PowerShell, and process hollowing of msiexec into RMClient.exe to deploy Remcos and harvest browser-stored credentials. The operation used compromised or malicious domains (e.g., icebergtbilisi.ge) to host payloads and employed continuous download-and-execute loops to ensure delivery. #Remcos #icebergtbilisi.ge
Keypoints
- Remcos RAT activity spiked in September–October 2025, representing the top infostealer in the dataset (~11% share).
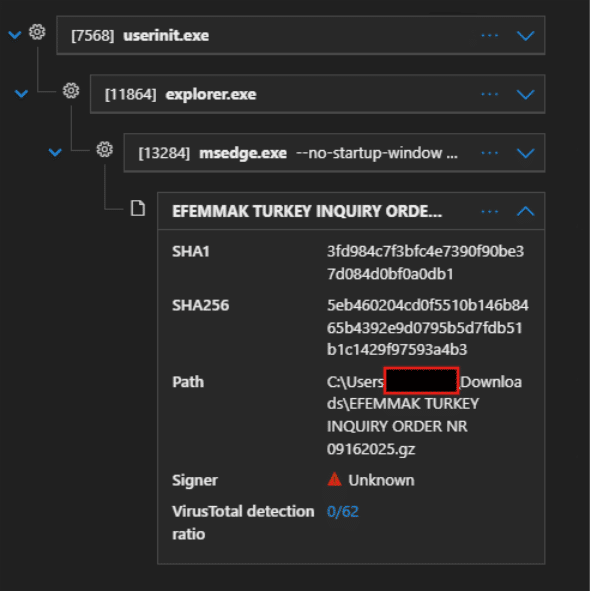
- Initial access occurred via phishing email with archive attachment named “EFEMMAK TURKEY INQUIRY ORDER NR 09162025.gz”.
- The archive dropped a batch file that launched an obfuscated PowerShell script which downloaded, base64-decoded, decompressed, and executed a payload from hxxps://icebergtbilisi.ge/Sluknin.afm.
- PowerShell launched msiexec.exe, which performed process hollowing to inject Remcos into RMClient.exe (Microsoft-distributed binary), enabling browser credential theft attempts.
- Partial EDR alerts triggered when browser files were accessed, enabling MDR detection of suspicious activity despite heavy obfuscation.
- IOC set includes malicious domains (icebergtbilisi[.]ge, ydns subdomains), attachment and script hashes, and specific file names used in the campaign.
- Campaign appears opportunistic credential theft focused, with potential for escalation to broader targeted intrusions if credentials are abused.
MITRE Techniques
- [T1566] Phishing – Email with an archive attachment “EFEMMAK TURKEY INQUIRY ORDER NR 09162025.gz” was used to deliver the initial payload.
- [T1204.002] User Execution: Malicious File – The victim extracted and executed a batch file from the archive which launched the next-stage PowerShell script.
- [T1059.001] PowerShell – Obfuscated PowerShell script executed hidden PowerShell process, used custom de-obfuscation and Invoke-Expression to run downloaded payload (‘…the script reads the content of this file, Base64 decodes it, and then attempts to decompress it using GZip…passed to Invoke-Expression…’).
- [T1105] Ingress Tool Transfer – The PowerShell script downloaded Sluknin.afm from hxxps://icebergtbilisi.ge and repeatedly retried until successful (‘…attempts to download a file from hxxps://icebergtbilisi.ge/Sluknin.afm to this path in a continuous loop…’).
- [T1569.002] Service Execution: Msiexec – PowerShell launched msiexec.exe to run the next-stage payload (PowerShell launches msiexec.exe as shown…).
- [T1055.012] Process Hollowing – msiexec.exe performed process hollowing to inject code into RMClient.exe to execute Remcos (‘…msiexec.exe used process hollowing to inject itself into RmClient.exe.’).
- [T1083] File and Directory Discovery / [T1530] Data from Information Repositories – Remcos attempted to access browser saved password files to steal credentials (the injected code is Remcos RAT trying to access browser saved password files…).
- [T1071.001] Application Layer Protocol: Web Protocols – msiexec initiated HTTP GET requests to C2 domains with custom User-Agent while retrieving random file names (GET request to malicious C2 domain and User-Agent used…).
Indicators of Compromise
- [Domain ] Malicious hosting/C2 – icebergtbilisi[.]ge, Ablelifepurelife[.]ydns.eu
- [Domain ] Additional C2/redirect – ablelifepurelifebk[.]ydns.eu, and other ydns subdomains
- [File name ] Malicious attachment and dropped scripts – EFEMMAK TURKEY INQUIRY ORDER NR 09162025.gz, EFEMMAK TURKEY INQUIRY ORDER NR 09162025.bat
- [File hash ] Attachment/script/powershell hashes – Attachment hash 5eb460204cd0f5510b146b8465b4392e9d0795b5d7fdb51b1c1429f97593a4b3, Batch script hash 5cb34177d0289e9737e5a261b8d1aac227656b96c768f789d6fcc9bc20adb05e, PowerShell content hash 3ec5b13ee66d84dd75ac619ebb79c64cef7986dd6e8049f689f9ac39c272fea2
- [File path ] Dropped/install path – C:UsersAppDataRoamingHereni.Gen (target install location created by script)
- [Filename ] Downloaded payload/component – Sluknin.afm hosted on icebergtbilisi[.]ge
- [File names ] Other benign-likely lure filenames used in campaign – LAUFENDES PROJEKT 092225 NORDRHEIN WESTFALEN CHARGE MATERIALIEN…js, ON GOING PROJECT 091704…js, and 3 more benign-looking filenames
Read more: https://www.cyberproof.com/blog/fileless-remcos-attacks-on-the-rise/