Trend Research uncovered an evolved Water Saci campaign that uses WhatsApp Web to deliver malicious ZIPs containing an obfuscated VBS downloader which launches a fileless PowerShell payload that hijacks browser sessions, harvests contacts, and self-propagates. The campaign pairs a dual-channel C2 infrastructure (email/IMAP to retrieve C2 URLs and aggressive HTTP polling) with multi-vector persistence, anti-analysis checks, and a real-time remote control system that can pause/resume propagation across infected machines. #SORVEPOTEL #WaterSaci
Keypoints
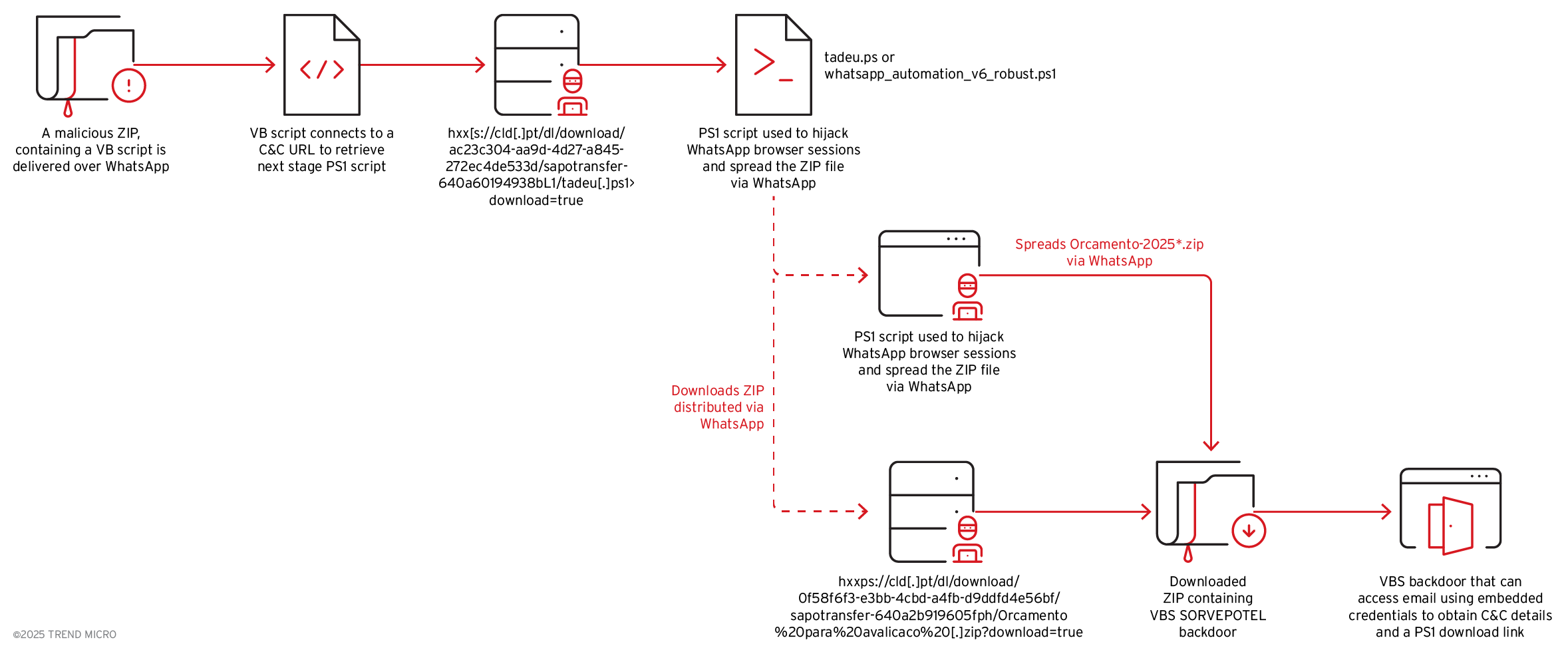
- Attack chain begins with Orcamento-2025*.zip delivered via WhatsApp Web, containing an obfuscated Orcamento.vbs that executes a fileless PowerShell script (tadeu.ps1) in memory.
- The PowerShell payload hijacks WhatsApp Web by copying Chrome profiles, installing ChromeDriver/Selenium, injecting WA-JS, harvesting contacts, and automatically sending malicious ZIPs to contacts.
- The malware uses a dual-channel C2 architecture: IMAP/email accounts (terra.com.br and others) to retrieve C2 URLs and aggressive HTTP POST polling to receive commands and report telemetry.
- Remote control supports real-time pause/resume via config checks (config.php?chave=envio_ativo) and continuous polling, allowing coordinated botnet-like operations and detailed campaign statistics reporting.
- Persistence is multi-vector: scheduled tasks and registry entries using a dropped WinManagers.vbs in C:ProgramDataWindowsManager, plus WMI-based single-instance enforcement.
- Anti-analysis and targeting checks include Portuguese locale enforcement, debugger/tool detection (ollydbg, idaq, x32dbg, etc.), and self-destruct cleanup behavior if analysis is detected.
- Backdoor capabilities are extensive (INFO, CMD, POWERSHELL, SCREENSHOT, file upload/download, REBOOT/SHUTDOWN, UPDATE, CHECK_EMAIL), enabling full remote management and data exfiltration.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – PowerShell/VBS used to execute the payload and perform automation (“…fileless execution via New-Object Net.WebClient to download and execute a PowerShell script named tadeu.ps1 directly in memory…”).
- [T1105] Ingress Tool Transfer – Downloads of WA-JS library, Bin.zip and payloads from remote servers/GitHub (“…downloads the latest WhatsApp automation library (WA-JS) from GitHub, and retrieves a malicious ZIP payload and saves it as Bin.zip in C:temp.”).
- [T1071] Application Layer Protocol – HTTP(S) polling for commands and result submission via POST requests (“…every five seconds, the malware sends HTTP POST requests to the extracted C&C servers, querying for pending commands using the action parameter get_commands.”).
- [T1102] Web Service – Abuse of WhatsApp Web session hijacking and WA-JS injection to propagate malicious ZIPs (“…hijack WhatsApp Web sessions, harvest all contacts from the victim’s account, and automatically distribute malicious ZIP files…”).
- [T1110] Brute Force (credential access to mail) / Valid Accounts – Use of hardcoded IMAP credentials to terra.com.br accounts to retrieve C2 URLs (“…leverages IMAP connections to terra.com.br email accounts using hardcoded email credentials to connect to the email account and retrieve commands.”).
- [T1543] Create or Modify System Process – Persistence via scheduled tasks and registry modifications using WinManagers.vbs (“…auto-installation routine establishes a foothold through both registry modifications and scheduled task creation using a dropped copy of itself named WinManagers.vbs saved in C:ProgramDataWindowsManager.”).
- [T1497] Virtualization/Sandbox Evasion – Debugger and analysis tool detection with self-destruct if detected (“…actively scanning for common analysis tools such as ollydbg.exe, idaq.exe, x32dbg.exe, x64dbg.exe, windbg.exe, processhacker.exe, and procmon.exe…creates a batch file to delete itself and execute cleanup operations.”).
- [T1036] Masquerading – Deceptive banner and filename patterns (Orcamento-2025*.zip) to appear legitimate (“…displaying a deceptive banner claiming to be ‘WhatsApp Automation v6.0’…files named Orcamento-2025*.zip.”).
- [T1112] Modify Registry – Registry autorun entries used as part of multi-vector persistence (“…persistence strategy includes registry modifications…”).
- [T1562] Impair Defenses – Session hijacking and copying Chrome profile cookies/tokens to bypass authentication (“…copies the victim’s legitimate Chrome profile data…This technique allows the malware to bypass WhatsApp Web’s authentication entirely…”).
Indicators of Compromise
- [File Name] WhatsApp-distributed ZIPs and dropped files – Orcamento-2025*.zip, Bin.zip, WinManagers.vbs.
- [Domains/URLs] C2 and config endpoints – miportuarios[.]com/sisti/config.php, miportuarios.com/sisti/config.php?chave=envio_ativo, hxxps://miportuarios[.]com/sisti/config[.]php (and other extracted URLs via email channel).
- [Email/IMAP accounts] Email C2 retrieval – terra[.]com[.]br accounts with hardcoded credentials and additional attacker-controlled emails (other domains observed and used with MFA later).
- [Scripts] Loader filenames and scripts – Orcamento.vbs (VBS downloader), tadeu.ps1 / whatsapp_automation_v6_robust.ps1 (PowerShell payload) and references to WA-JS library.
- [Artifacts/Paths] Persistence and workspace paths – C:temp (Bin.zip, Chrome profile copies), C:ProgramDataWindowsManagerWinManagers.vbs (and scheduled task/registry entries).
Read more: https://www.trendmicro.com/en_us/research/25/j/active-water-saci-campaign-whatsapp-update.html