BlueNoroff’s SnatchCrypto operation runs two linked campaigns — GhostCall and GhostHire — that use sophisticated social engineering (fake Zoom/Teams calls and fake recruiter assessments) to deliver multi-stage malware chains targeting Web3/blockchain executives and developers. The actor reuses recordings of real victims, leverages Telegram and GitHub for delivery, and deploys modular implants like DownTroy, ZoomClutch/TeamsClutch, CosmicDoor, RooTroy, SneakMain, and SysPhon while employing AI to refine lures and tooling. #BlueNoroff #DownTroy
Keypoints
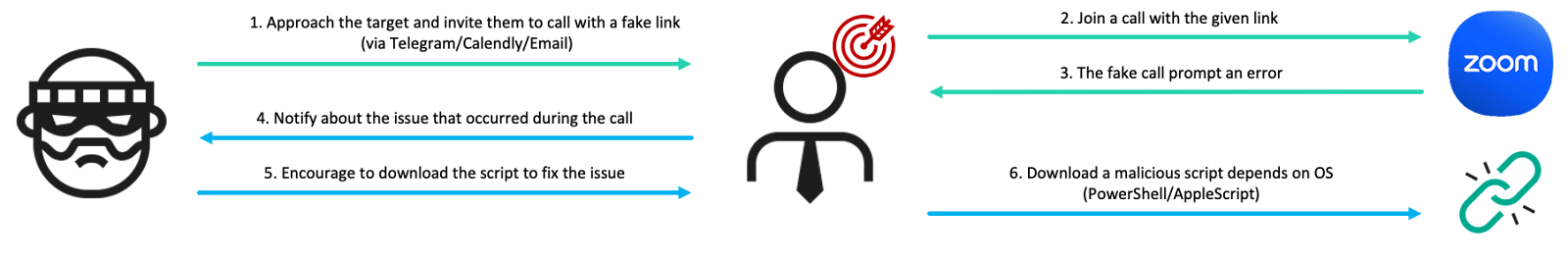
- BlueNoroff operates SnatchCrypto campaigns GhostCall (fake video meeting lures) and GhostHire (fake recruiter coding tests) to target Web3/blockchain executives and developers.
- GhostCall fakes live calls by replaying real webcam recordings of prior victims and prompts targets to download malicious “SDK update” AppleScript or trigger clipboard-based malware on Windows.
- Multiple modular macOS and Windows infection chains were observed (DownTroy, ZoomClutch/TeamsClutch, CosmicDoor, RooTroy, RealTimeTroy, SneakMain, SysPhon), often delivered from centralized file hosting servers.
- Stealer suite SilentSiphon exfiltrates extensive data (browser creds, Keychain, package managers, cloud keys, OpenAI API tokens, Telegram caches, notes, and crypto wallet data) enabling follow-on attacks and supply-chain abuse.
- Attackers use injectors (GillyInjector) and loaders (Nimcore, Nim-based loaders) to inject payloads into benign apps or processes and implement persistence via LaunchAgents/Daemons and Windows services.
- GhostHire abuses Telegram bots and malicious GitHub/TypeScript or Go projects with malicious dependencies (e.g., uniroute, sorttemplate) to execute OS-specific DownTroy downloaders; GhostCall primarily targets macOS.
- BlueNoroff employs AI for image enhancement and likely to generate or refine malicious scripts and social-engineering content, increasing operational efficiency and tailoring of lures.
MITRE Techniques
- [T1586] Compromise Infrastructure – Actor hosts malicious installers and payloads on file hosting servers and phishing domains to deliver multi-stage chains (“…downloads ZIP files that contain various individual infection chains from the actor’s centralized file hosting server…”).
- [T1192] Spearphishing via Service – Initial contacts via Telegram impersonating VCs/recruiters and use of Calendly and fake meeting links (“…reaches out to targets on Telegram by impersonating venture capitalists… use Calendly to schedule a meeting and then share a meeting link through domains that mimic Zoom”).
- [T1204] User Execution – Victims are socially engineered to execute AppleScript/PowerShell/other scripts disguised as Zoom/Teams updates or recruiter tasks (“…prompting them to download a Zoom SDK update file… downloads a malicious AppleScript file… bot sends either a ZIP file or a GitHub link… prompt with 30-minute time limit… run the malicious project”).
- [T1059] Command and Scripting Interpreter – Use of AppleScript, PowerShell, bash, VBScript and other scripts as downloaders and payloads (DownTroy, AppleScript downloaders, init.ps1, init.vbs) (“…AppleScript ‘Zoom SDK Update.scpt’… PowerShell code is XOR-encrypted… VBScript version of DownTroy”).
- [T1555] Credentials from Password Stores – ZoomClutch and stealers exfiltrate macOS passwords, Keychain, and other vault data (“…ZoomClutch steals macOS passwords… logs to ~/Library/Logs/keybagd_events.log and upload… targets Keychain: /Library/Keychains/System.keychain and ~/Library/Keychains/login.keychain-db”).
- [T1218] System Binary Proxy Execution – Use of legitimate-sounding binaries (e.g., fake zoom.app in /tmp, ChromeUpdate, Computerdefaults.exe) and process injection into legitimate processes (cmd.exe, notepad.exe) to run malicious code (“…suspicious application resembling a Zoom client executing from /tmp… injects the payload into cmd.exe process… creates notepad.exe in suspended mode and injects payload”).
- [T1055] Process Injection – GillyInjector and peshooter-style injection to inject encrypted payloads into benign processes at runtime (“…GillyInjector designed to run a benign Mach-O app and inject a malicious payload into it at runtime… peshooter to execute an additional payload into memory”).
- [T1547] Boot or Logon Autostart Execution – Persistence via LaunchAgents/LaunchDaemons plists on macOS and Windows services (NetCheckSvc) (“…creates plist files to ensure automatic restart… installs Launch Daemons… service named NetCheckSvc to run RooTroy.Windows”).
- [T1112] Modify Registry or Configuration – Offline edits to macOS TCC.db to grant automation and file access permissions enabling AppleEvents and folder access without prompts (“…renaming the user’s com.apple.TCC directory and then performing offline edits to the TCC.db database… executes INSERT OR REPLACE statements… grants AppleEvents permissions…”).
- [T1496] Resource Hijacking – Reuse of real victim webcam recordings as convincing meeting participants to deceive other victims (“…videos were, in fact, real recordings secretly taken from other victims… uploaded to attacker-controlled infrastructure, and reused to deceive other victims”).
- [T1609] Data from Information Repositories – SilentSiphon harvests notes, package manager files, cloud configs, DevOps secrets, OpenAI tokens, and messenger caches (“…targets Apple Notes, package managers, cloud/infrastructure configs, .openai, Telegram cached resources…”).
- [T1176] Browser Extensions – Steals browser extension data and IndexedDB for crypto wallet extensions (cpl.sh targeting Local Extension Settings and IndexedDB for Exodus, Coinbase Wallet, Crypto.com, Manta Wallet, etc.) (“…targets Local Extension Settings directory… IndexedDB directories of Exodus Web3 Wallet, Coinbase Wallet extension…”).
- [T1588] Obtain Capabilities – Actor leverages AI for image enhancement and script generation to produce lures and malicious scripts (“…images whose filenames were set to the target’s name… enhanced with GPT-4o… comments that appear to be AI-generated in the secrets stealer module”).
Indicators of Compromise
- [File hash] malware samples and scripts – examples: AppleScript Zoom SDK Update.scpt (hash e33f942cf1479ca8530a916868bad954), ZoomClutch binary (hash 7f94ed2d5f566c12de5ebe4b5e3d8aa3).
- [File hash] stealer scripts – examples: upl.sh (hash e8680d17fba6425e4a9bb552fb8db2b1), secrets.sh (hash 38c8d80dd32d00e9c9440a498f7dd739).
- [Domain] C2 and file hosting – examples: dataupload[.]store (file hosting), safeupload[.]online (ZoomClutch/TeamsClutch upload endpoint), and other C2s like signsafe[.]xyz and safefor[.]xyz.
- [URL] fake meeting pages used to deliver AppleScript – examples: hxxp://web071zoom[.]us/fix/audio/4542828056, hxxps://support.ms-live[.]us/update/02583235891.
- [File name / path] persistence and implant paths – examples: /Library/Application Support/Logitechs/bin/Update Check (Nimcore loader location), /private/tmp/[random].zip (temporary staged installer), and ~/Library/CoreKit/CoreKitAgent (DownTroy v2 components).
Read more: https://securelist.com/bluenoroff-apt-campaigns-ghostcall-and-ghosthire/117842/