Global Group is a Ransomware-as-a-Service (RaaS) operation that surfaced in June 2025, offering cross-platform Go-based payloads, affiliate-friendly features (including AI-assisted extortion), and reuse of code and infrastructure linked to Mamona and BlackLock. AttackIQ published an emulation/attack graph to help organizations validate detection and prevention controls against Global Group behaviors. #GlobalGroup #Mamona #BlackLock
Keypoints
- Global Group publicly emerged in June 2025 as a commercial RaaS platform promoted by a Russian-speaking actor known as “$$$”.
- The operation shows strong overlaps with Mamona and BlackLock, including shared infrastructure, identical mutex, reused encryption and network code, and similar ransom note/negotiation styles.
- Payloads are written in Go for cross-platform support (Windows, Linux, macOS) and include features such as LDAP propagation, token impersonation, configurable execution modes, and AI-assisted negotiation/chatbot extortion.
- Encryption uses ChaCha20-Poly1305 with a speed-optimized approach (files <5 MB fully encrypted; larger files partially encrypted at ~20%), plus actions to disable recovery (clear event logs, delete shadow copies) and terminate AV/EDR processes.
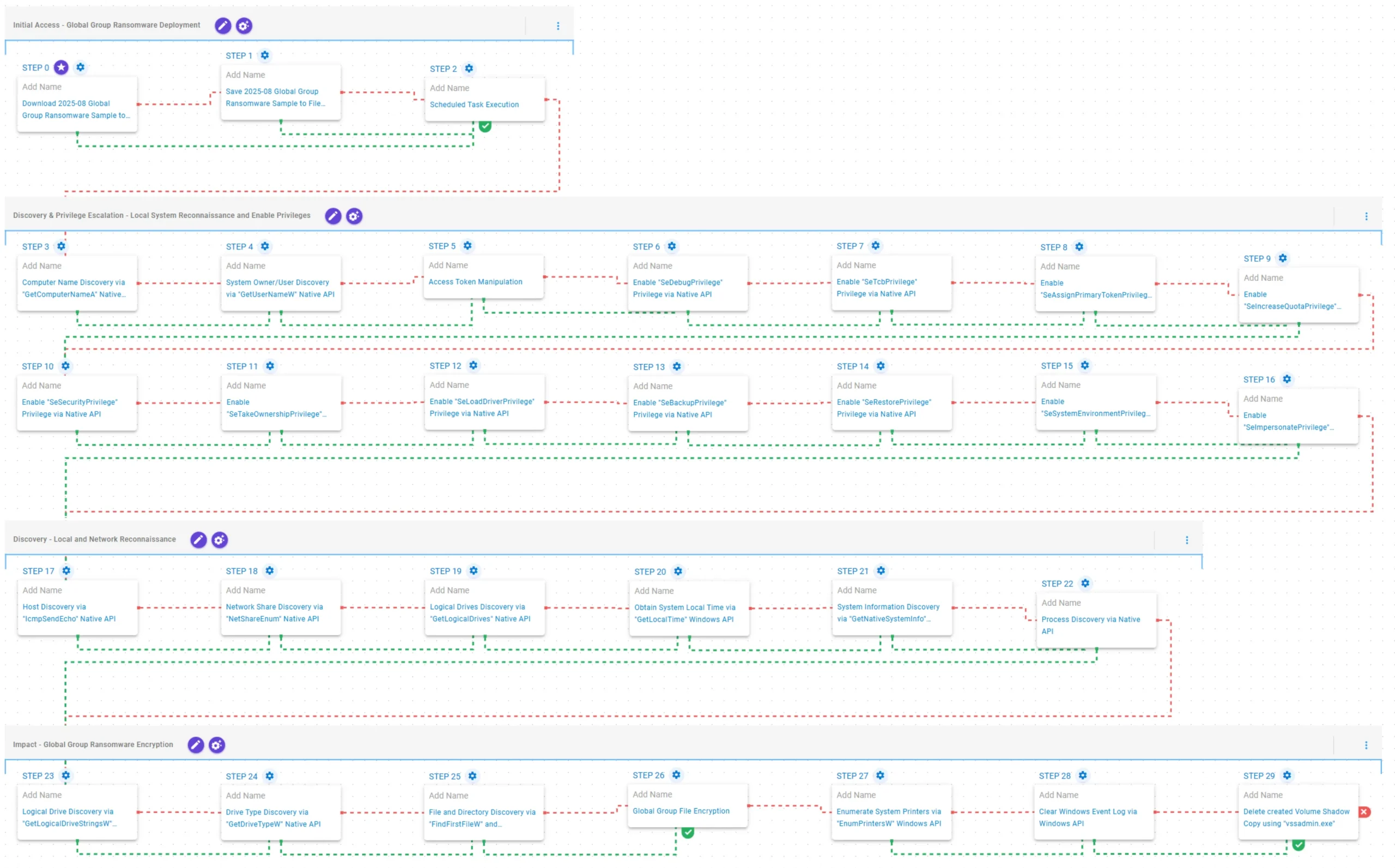
- AttackIQ released an emulation/attack graph (2025-09) that replicates Global Group TTPs to validate security controls, covering initial access, persistence, discovery, privilege escalation, and impact/encryption behaviors.
- The emulation demonstrates specific techniques including scheduled task execution for persistence, token manipulation and AdjustTokenPrivilege calls for privilege escalation, and native API calls for discovery and encryption routines.
- Using the AttackIQ assessment helps teams evaluate control performance, continuously validate detection/prevention pipelines, and improve incident response and security posture against opportunistic ransomware actors.
MITRE Techniques
- [T1105 ] Ingress Tool Transfer – The Global Group sample (SHA256: 23b43226d53e2c8cd9519d785ba75b833fbd11939cd1d70999f84c1365b2da5d) is downloaded to memory and saved to disk: ‘The Global Group Ransomware sample … is downloaded to memory and saved to disk’.
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – Persistence and execution are emulated by creating and running a scheduled task with schtasks: ‘scheduling and executing a task using the Windows utility schtasks’.
- [T1082 ] System Information Discovery (GetComputerNameA/GetNativeSystemInfo/GetLogicalDrives) – Local host and drive information are gathered via GetComputerNameA, GetNativeSystemInfo, and GetLogicalDrives: ‘calls the GetComputerNameA Windows API to gather the NetBIOS name’ / ‘GetNativeSystemInfo Native API call to retrieve information associated with the system’ / ‘GetLogicalDrives Windows API call to retrieve the currently available disk drives’.
- [T1033 ] System Owner/User Discovery (GetUserNameW) – The emulation retrieves the logged-on account name using GetUserNameW: ‘executes the GetUserNameW Windows native API call to retrieve the account name associated with the local computer’.
- [T1134 ] Access Token Manipulation – The scenario lists and duplicates access tokens and enables multiple privileges via AdjustTokenPrivilege to escalate and impersonate: ‘lists and duplicates access tokens … impersonating a logged-in user’ and ‘enables the SeDebugPrivilege privilege … using the AdjustTokenPrivilege Windows API’.
- [T1046 ] Network Service Discovery (IcmpSendEcho) – Host discovery is conducted with ICMP probes using IcmpSendEcho to scan local networks: ‘executes the IcmpSendEcho Windows API call to perform a discovery scan on local networks’.
- [T1135 ] Network Share Discovery (NetShareEnum) – Network shares are enumerated via NetShareEnum: ‘executes the NetShareEnum Windows native API call to enumerate network shares from the local computer’.
- [T1057 ] Process Discovery (CreateToolhelp32Snapshot/Process32FirstW/Process32NextW) – Running processes are enumerated by taking a snapshot and iterating entries: ‘executes the CreateToolhelp32Snapshot Windows native API call to receive a list of running processes and iterates … with Process32FirstW and Process32NextW’.
- [T1120 ] Peripheral Device Discovery (GetLogicalDriveStringsW/GetDriveTypeW/EnumPrintersW) – Drive and printer enumeration use GetLogicalDriveStringsW, GetDriveTypeW, and EnumPrintersW during impact: ‘executes the GetLogicalDriveStringsW Windows native API call …’ and ‘executes the EnumPrintersW Windows API to enumerate available printers’.
- [T1083 ] File and Directory Discovery (FindFirstFileW/FindNextFileW) – File system enumeration is performed with FindFirstFileW and FindNextFileW to identify encryption targets: ‘executes the FindFirstFileW and FindNextFileW Windows native API calls to enumerate the file system’.
- [T1486 ] Data Encrypted for Impact – Files matching an extension list are encrypted in place using ChaCha20-Poly1305 and a partial-encryption strategy for large files: ‘performs the file encryption routines … Files matching an extension list are identified and encrypted in place using similar encryption algorithms as used by Global Group ransomware’.
- [T1070.001 ] Clear Windows Event Logs – The emulation clears Windows Event Logs via ClearEventLogW to hinder forensic analysis: ‘executes the ClearEventLogW Windows API to clear Windows Event Logs’.
- [T1490 ] Inhibit System Recovery (vssadmin.exe) – The scenario deletes Volume Shadow Copies using vssadmin.exe to prevent recovery: ‘executes the vssadmin.exe utility to delete a recent Volume Shadow Copy’.
Indicators of Compromise
- [File Hash ] Global Group sample used in emulation – 23b43226d53e2c8cd9519d785ba75b833fbd11939cd1d70999f84c1365b2da5d
- [File Name/Utility ] Recovery and system utilities used by the ransomware – vssadmin.exe (used to delete shadow copies), schtasks (used to create/execute scheduled tasks)
- [API Calls / Artifacts ] Notable native API usage indicating ransomware behavior – GetComputerNameA, GetUserNameW, AdjustTokenPrivilege (access token/privilege manipulation)
Read more: https://www.attackiq.com/2025/10/16/emulating-global-group-ransomware/