WaterPlum Cluster B (BlockNovas) has been observed distributing a new Node.js RAT/infostealer named OtterCandy across Windows, macOS, and Linux to steal browser credentials, crypto wallets, and files via Socket.IO-connected C2 servers. An August 2025 update (v2) added client_id for improved victim identification, expanded browser-extension theft targets, full Chromium data exfiltration, and enhanced deletion of persistence traces. #OtterCandy #WaterPlum
Keypoints
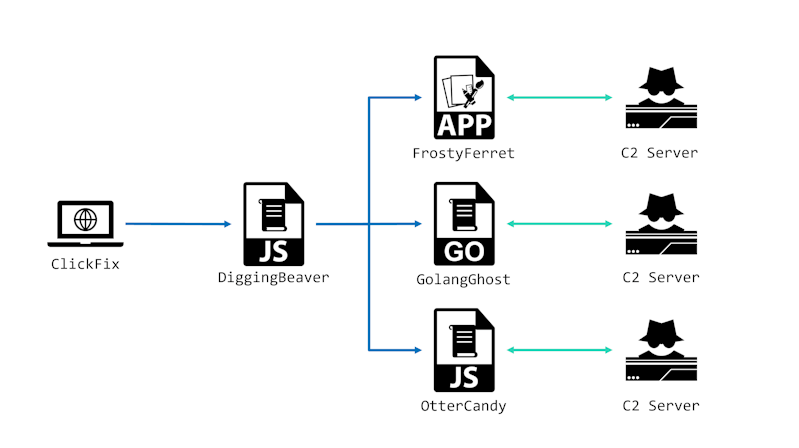
- WaterPlum Cluster B (aka BlockNovas) is actively involved in the ClickFake Interview campaign and has distinct tooling and malware development within the WaterPlum umbrella.
- OtterCandy is a Node.js-based RAT and infostealer that reuses ideas from RATatouille and OtterCookie and communicates with C2 via Socket.IO.
- OtterCandy targets browser credentials, cryptocurrency wallets, and confidential files; it accepts commands from C2 to perform these actions.
- Earlier samples were observed as early as February 2025; the codebase remained largely unchanged until an August 2025 update (v2) aside from C2 address changes.
- v2 changes include adding a client_id for improved victim identification, increasing hardcoded browser extension IDs from four to seven, and switching to full Chromium data exfiltration.
- v2 also extended ss_del functionality to remove registry keys, files, and directories used for persistence, and OtterCandy also persists via DiggingBeaver and a simple SIGINT fork routine.
- Multiple IoCs (IP addresses) linked to OtterCandy/C2 activity have been identified and should be monitored.
MITRE Techniques
- [T1071 ] Application Layer Protocol – OtterCandy connects to its command-and-control server via Socket.IO to receive commands and exfiltrate data; “…accepts commands when connected to the C2 server via Socket.IO.”
- [T1056 ] Input Capture – The malware steals browser credentials and cryptocurrency wallet data by targeting browser storage and extensions; “…to steal browser credentials, cryptocurrency wallets, and/or confidential files from the victim’s device.”
- [T1105 ] Ingress Tool Transfer – OtterCandy was distributed to victims across Windows, macOS, and Linux as part of ClickFake Interview campaigns; “…since around July 2025, OtterCandy has been distributed for Windows, macOS, and Linux.”
- [T1543 ] Create or Modify System Process – OtterCandy implements persistence by forking on SIGINT and relies on DiggingBeaver for persistence; “…when it receives SIGINT event via process.on, it folks itself again.”
- [T1070 ] Indicator Removal on Host – v2 added deletion of registry keys, files, and directories in the ss_del command to remove traces of persistence; “Deletion of registry keys used for persistence, as well as the deletion of files and directories are added to ss_del command…”
- [T1036 ] Masquerading – OtterCandy incorporates code and features from RATatouille and OtterCookie, blending with existing toolsets within WaterPlum clusters to evade attribution; “…combines elements of RATatouille and OtterCookie.”
Indicators of Compromise
- [IP Address ] C2 and related infrastructure – 162[.]254.35.147, 4[.]119.194.205
- [IP Address ] Additional infrastructure – 172[.]86.114.311, 139[.]60.163.206
- [IP Address ] Further observed hosts – 212[.]85.29.133, 80[.]209.243.85
- [File/Sample ] Early submitted sample context – a February 2025 OtterCandy sample on VirusTotal (identified as same sample mislabelled as OtterCookie in prior reporting)
Read more: https://jp.security.ntt/insights_resources/tech_blog/ottercandy_malware_e