Cofense PDC discovered a phishing campaign delivering a malicious Chrome extension named “Mac Spoofer” via a ZIP attachment that, when sideloaded, captures credentials and exfiltrates them to reader.hibarriotech[.]com/api/send-anything. The extension was distributed with step-by-step installation instructions and a social-engineering lure promising $50,000 to compel installation and 30 days of use. #MacSpoofer #hibarriotech
Keypoints
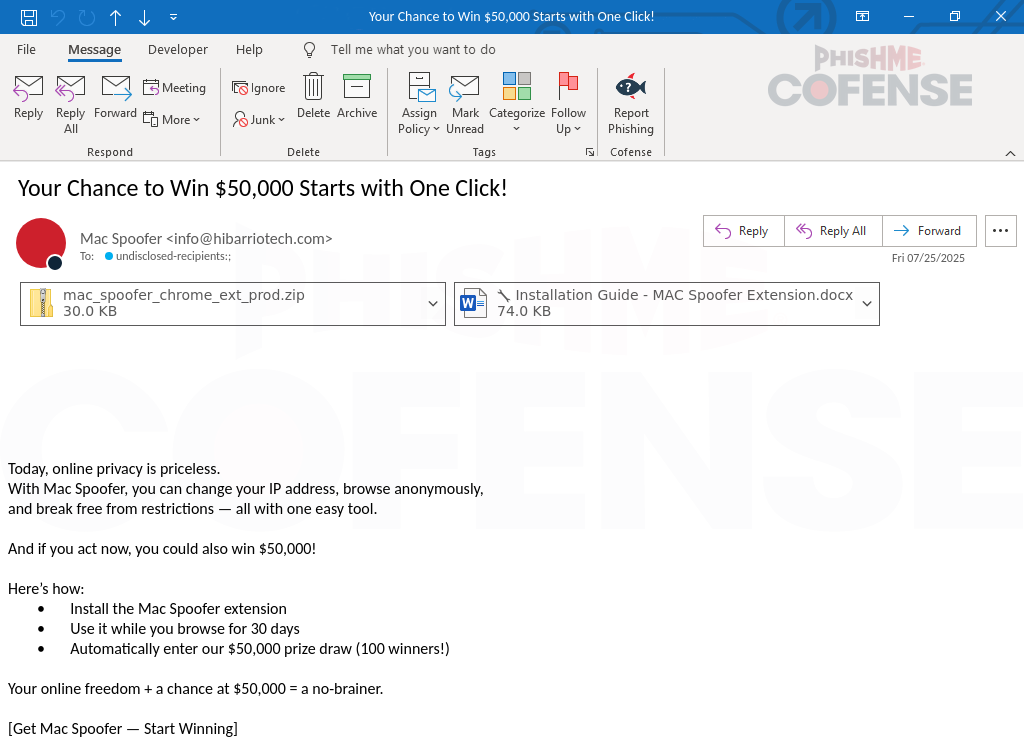
- The campaign delivered a Chrome extension packaged in mac_spoofer_chrome_ext_prod.zip that requires manual sideloading rather than the Chrome Web Store.
- The email lure offered a $50,000 prize and claimed the extension randomizes MAC addresses to browse anonymously, creating urgency to lower user scrutiny.
- The ZIP contained extension files (index.js, manifest.json, index.html) and two notable scripts: content.js (core functionality) and main.min.js (support library).
- content.js contained Base64-encoded values that decode to a POST request to hxxps[:]//reader.hibarriotech[.]com/api/send-anything, observed being called during login attempts, indicating credential capture and exfiltration.
- The domain hibarriotech[.]com (registered Feb 2025) and the provided installation guide were used to create legitimacy and instruct users how to enable developer mode and sideload the extension.
- Observed IOCs include the infection URL reader.hibarriotech[.]com/api/send-anything and IP 194[.]146[.]41[.]102, plus file artifacts and hashes for mac_spoofer_chrome_ext_prod.zip, content.js, and main.min.js.
- Cofense notes that SEGs can miss such threats and recommends human analysis and managed phishing defenses to detect and remediate sideloaded-extension attacks.
MITRE Techniques
- [T1218] Signed Binary Proxy Execution – The extension uses legitimate JavaScript execution within the browser to run malicious code; content.js contains encoded values that decode to an exfiltration POST to ‘…reader.hibarriotech[.]com/api/send-anything…’ demonstrating abuse of normal execution to perform malicious actions.
- [T1056] Input Capture – The extension captures credentials during login attempts and sends them to the actor’s endpoint: ‘…observed calls to the hxxps[:]//reader.hibarriotech[.]com/api/send-anything URL was observed upon attempting to complete the login…’.
- [T1195] Supply Chain Compromise (Browser Extensions) – The actor distributed a malicious browser extension outside the official store, providing installation instructions to bypass normal distribution safeguards: ‘…must be manually installed…include instructions on how to do that.’
- [T1078] Valid Accounts – The extension captures user credentials for later use, as evidenced by attempts to log in to services resulting in credential exfiltration: ‘…suggest the extension intends to capture credentials for later use by the threat actor…’.
- [T1204] User Execution – Social engineering lure promising $50,000 and instructions to sideload the extension coerced user action: ‘…offering a chance at $50,000 if they leave it installed and use it for 30 days.’
Indicators of Compromise
- [URL] exfiltration endpoint – hxxps[:]//reader.hibarriotech[.]com/api/send-anything
- [IP] associated server – 194[.]146[.]41[.]102
- [Domain] threat actor domain – hibarriotech[.]com (registered Feb 2025)
- [File] malicious attachment – mac_spoofer_chrome_ext_prod.zip (SHA256: a377f9aa7492df77f2937be41298ac7928… , size 2.5 KB)
- [File] extension script – content.js (SHA256: 139783895fc2f0d21af6cfd9c042e520697 Bytes; MD5: Ce9e91bd98c87974e9f458127eb80564) and main.min.js (SHA256: b5cdef228778407896d95c36fcadcfec71…; MD5: Aa5a66f28b015503b26e63c0c9922f74)