A cluster of 131 rebranded Chrome extensions share a single codebase that injects into WhatsApp Web to automate bulk messaging and scheduling, enabling large-scale spam and evasion of WhatsApp anti-spam controls while violating Chrome Web Store and WhatsApp policies. The operation uses a white‑label reseller/franchise model (DBX Tecnologia / Grupo OPT) to distribute near-identical clones across dozens of listings and marketing sites, accounting for at least 20,905 active users. #DBXTecnologia #GrupoOPT
Keypoints
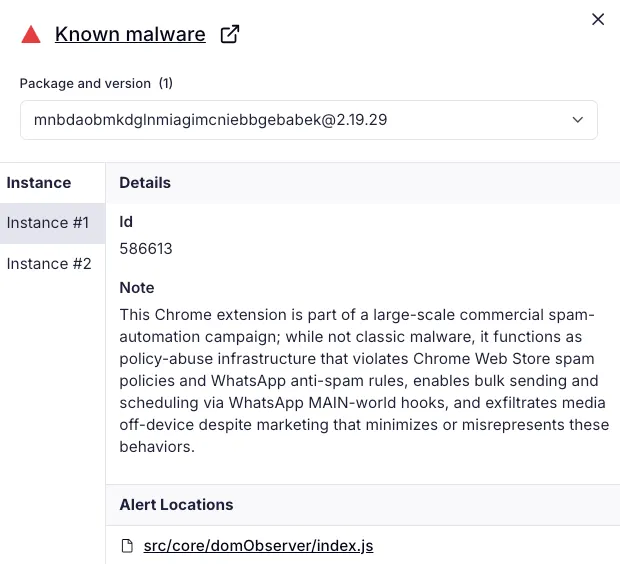
- 131 Chrome extensions are rebrands of a single WhatsApp Web automation tool that injects code into web.whatsapp.com to automate bulk outreach and scheduling.
- The extensions are marketed for aggressive outbound messaging and include tutorials that describe tuning send intervals and batching to evade WhatsApp anti-spam systems.
- The cluster is distributed via a white-label/reseller franchise model run by DBX Tecnologia and Grupo OPT, enabling affiliates to rebrand and resell identical builds.
- All listings collectively show at least 20,905 active users; many clones were live simultaneously in the Chrome Web Store and updated regularly over at least nine months.
- The operation violates Chrome Web Store Spam & Abuse policies (duplicate experiences, spam, sending messages without confirmation) and WhatsApp Business Messaging policies (required opt-in and anti-spam rules).
- Two developer accounts ([email protected] and [email protected]) published the cluster, with the dominant publisher label WL Extensão/WLExtensao appearing across 83 listings.
- Recommendations include inventorying extensions, enforcing allowlists and permissions controls, blocking risky updates, and monitoring lookalike domains and publisher activity.
MITRE Techniques
- [T1176.001] Software Extensions: Browser Extensions – Browser extension code injects into WhatsApp Web (document-start injection) and runs alongside WhatsApp scripts to automate messaging (“document-start injection into WhatsApp Web”).
- [T1204] User Execution – Extensions operate within the user’s browser and require user installation to execute automation features that send messages on the user’s behalf (marketing and reseller model encourages installs and subscriptions).
- [T1059.007] Command and Scripting Interpreter: JavaScript – The tool uses JavaScript helpers (window.WPP.*) to dispatch messages and implement scheduled send logic (“use of window.WPP.* helpers for message dispatch, and scheduled send logic via a Manifest V3 service worker”).
- [T1217] Browser Information Discovery – The extension accesses WhatsApp Web DOM and browser context to enumerate and interact with conversations and contacts for bulk messaging (injection into web.whatsapp.com and automated message dispatch).
- [T1005] Data from Local System – Extensions may route media and message content through vendor infrastructure and interact with local browser storage or files as part of automation and scheduling (features route media to vendor infrastructure and backend communication with DBX-controlled services).
Indicators of Compromise
- [Email Address] publisher/developer accounts – [email protected], [email protected]
- [Chrome Extension ID / name / active users] examples of rebranded extension listings and user counts – mnbdaobmkdglnmiagimcniebbgebabek (Organize-C) — 5,000 users; mkbjflhgpickfellipdmpcnhkmmdcojl (YouSeller) — 10,000 users (and many other extension IDs listed, totaling 131 entries).
- [Domain / marketing site] reseller and marketing pages – zapvende[.]com (Zap Vende), lobovendedor[.]com[.]br (Lobo Vendedor) — used to promote rebranded clones.
- [Domain / operator site] operator infrastructure – dbx[.]global/whats/ (DBX Whats) — backend services that branded builds contact for updates and feature use.
- [Chrome Extension IDs] additional sample IDs and contexts – cjdcglineikacjboikmchenneanfegoo (ZappSeller) — 296 users; ofmoeicegmlaleajnpcbddiaomnfmfkp (DBX Whats) — 1,000 users (and 100+ other extension IDs listed).
Read more: https://socket.dev/blog/131-spamware-extensions-targeting-whatsapp-flood-chrome-web-store