CERT-AGID has observed a new PagoPA-themed phishing campaign that uses Google open-redirect parameters to make malicious links appear legitimate and bypass automated checks. The attack chain leverages legitimate services (Google adservice, bio.site, privatedns.org) to host intermediate pages and a final phishing form that harvests personal and payment card data. #PagoPA #adservice.google.be
Keypoints
- CERT-AGID detected a new phishing variant targeting PagoPA that reuses a fines-themed lure to trick users.
- Attackers abuse Google open-redirects (e.g., adservice.google.be) so malicious URLs appear to point to Google services.
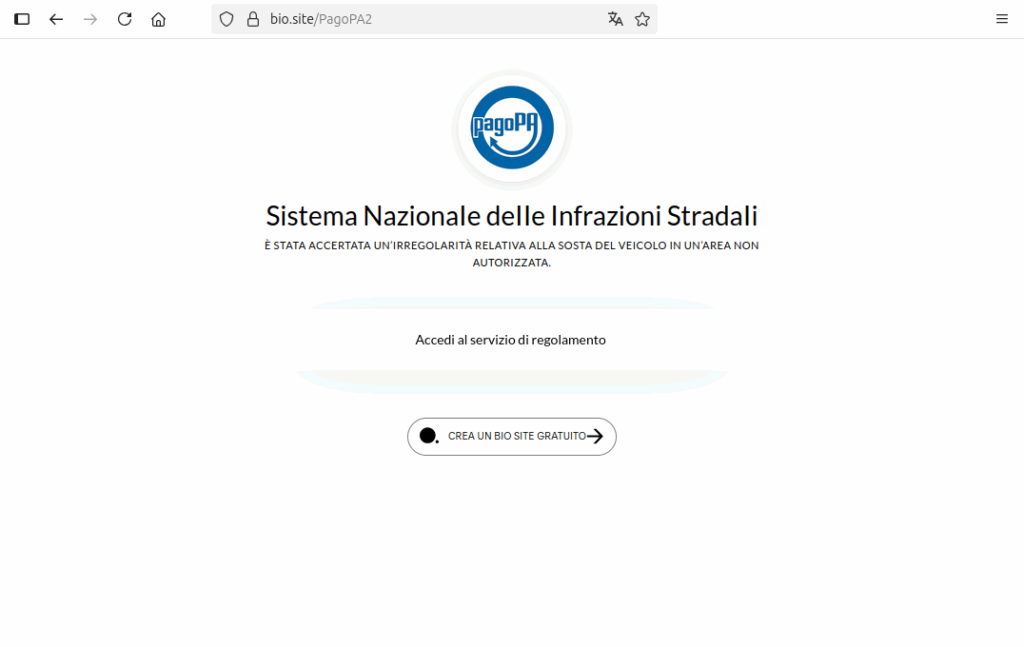
- An intermediate page hosted on bio.site is used to display a convincing PagoPA logo and a call-to-action button.
- The final phishing page, hosted on privatedns.org subdomains, imitates the official PagoPA portal and collects personal and payment card details.
- This chain exploits legitimate platforms (Google adservice, bio.site, privatedns.org) to increase trust and evade automated defenses.
- Similar abuse of Google open-redirects was documented in 2023 (e.g., adservice.google.de) and remains present across domains like .it and .com.
- Since March 2025, CERT-AGID has observed 220 PagoPA-related phishing campaigns and shared 2,574 IOCs with authorities and accredited entities.
MITRE Techniques
- [T1090] Proxy: External Proxy – Attackers route victims through legitimate services (Google adservice, bio.site, privatedns.org) to mask final phishing destinations and leverage service reputation. Quote: “…the parameter allows performing an open redirect, enabling redirection to any URL on a third-party domain.”
- [T1204] User Execution – Phishing – Victims are induced to click a deceptive link and press a button labeled “Access the settlement service” to access what appears to be a PagoPA service. Quote: “…inviting the user to click on a button with the wording ‘Access the settlement service.’”
- [T1555] Credentials from Web Forms – Input Capture – The final phishing page imitates the official portal to collect personal data and electronic payment card information. Quote: “…collects personal data and electronic payment card data.”
- [T1608] Modify Cloud Compute Infrastructure – Abuse of Legitimate Services – Adversaries misuse legitimate hosting/redirect services (bio.site, privatedns.org, Google adservice) as part of the infrastructure to host intermediate and final phishing pages. Quote: “…privatedns.org…often abused by malicious actors because it allows creating addresses difficult to trace or block centrally.”
Indicators of Compromise
- [Domain ] intermediate hosting and final phishing hosts – bio.site (intermediate page imitation), privatedns.org (final phishing subdomains).
- [Campaign counts ] operational context – 220 phishing campaigns targeting PagoPA since March 2025, and 2,574 shared IOCs with administrations and accredited entities.
<li [URL ] example of open-redirect abuse – hxxps://adservice.google.be/clk/408533097;208818505;l;?//evilwebsite.tld/page (open-redirect parameter used to forward to malicious site).
Read more: https://cert-agid.gov.it/news/phishing-contro-pagopa-abusa-di-open-redirect-google/