A malicious npm package named https-proxy-utils was published and used to deliver the AdaptixC2 post-exploitation agent via a post-install script that deployed OS-specific payloads for Windows, macOS, and Linux. The campaign abused trusted open-source package names and supply-chain mechanisms, using DLL sideloading on Windows, LaunchAgents on macOS, and /tmp delivery on Linux to achieve persistence and remote access. #AdaptixC2 #https-proxy-utils
Keypoints
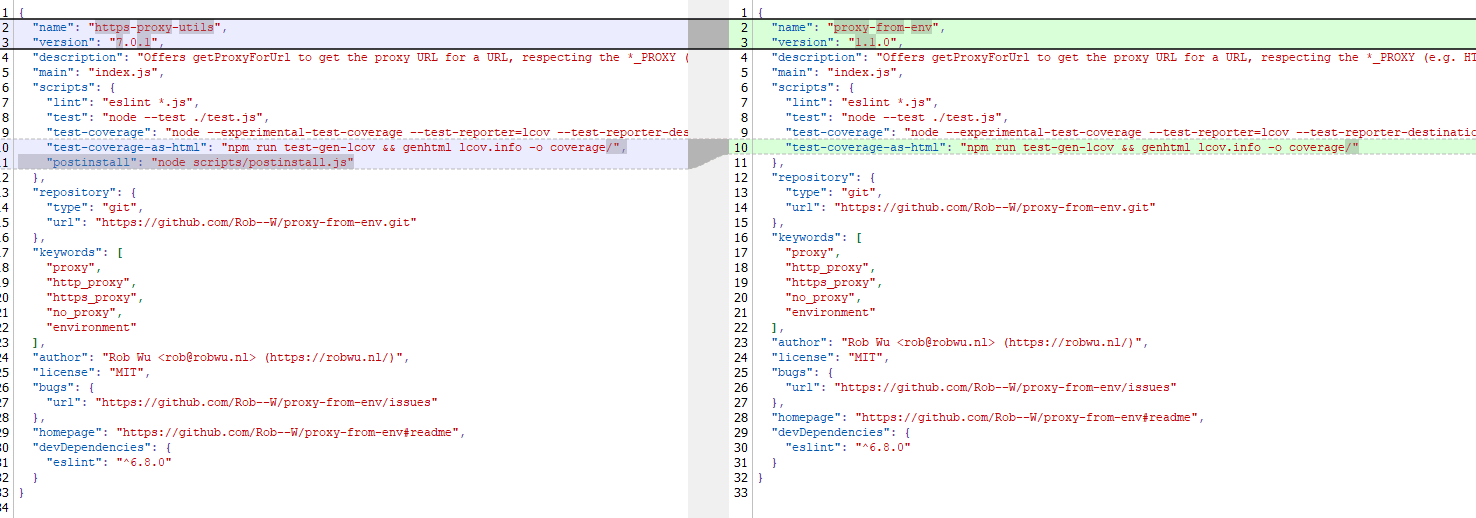
- A malicious npm package, https-proxy-utils, impersonated legitimate proxy packages and was removed after discovery by Kaspersky in October 2025.
- The package contained a post-install.js script that downloaded and executed an AdaptixC2 agent, a post-exploitation framework similar to Cobalt Strike.
- Payload delivery was OS-specific: Windows uses DLL sideloading in C:WindowsTasks, macOS uses Library/LaunchAgents with plist autorun, and Linux places an executable in /tmp/.fonts-unix with executable permissions.
- The actor checked CPU architecture (x64 vs ARM) and fetched corresponding binary variants for each OS before execution.
- Once deployed, AdaptixC2 provided remote access, command execution, file/process management, persistence, network reconnaissance, and the ability to deploy follow-on stages.
- The incident follows a pattern of npm registry abuse (e.g., the recent Shai-Hulud worm campaign) and highlights supply-chain risks in open-source ecosystems.
- Recommendations: verify exact package names, scrutinize new or unpopular repositories, and monitor feeds for compromised or frequently updated packages.
MITRE Techniques
- [T1553] Subvert Trust Controls – The malicious package impersonated popular legitimate packages (e.g., http-proxy-agent, https-proxy-agent) and cloned functionality from proxy-from-env to appear legitimate; “the threat actor injected a post-install script into https-proxy-utils, which downloads and executes a payload containing the AdaptixC2 agent.”
- [T1218] Signed Binary Proxy Execution (Msdtc.exe DLL sideloading) – On Windows the script copied msdtc.exe and executed it to load a malicious DLL from C:WindowsTasks via sideloading; “The JS script copies the legitimate msdtc.exe file to the same directory and executes it, thus loading the malicious DLL.”
- [T1543] Create or Modify System Process (Launch Agents/Plist) – On macOS the postinstall script dropped a plist into Library/LaunchAgents to achieve autorun and executed a downloaded payload; “the script downloads the payload as an executable file into the user’s autorun directory: Library/LaunchAgents” and “drops a plist autorun configuration file into this directory.”
- [T1158] Hidden Files and Directories (use of system/user directories) – The actor placed binaries in OS-specific directories to hide and run the agent (C:WindowsTasks, Library/LaunchAgents, /tmp/.fonts-unix); “the AdaptixC2 agent is dropped as a DLL file into the system directory C:WindowsTasks” and “the framework’s agent is downloaded into the temporary directory /tmp/.fonts-unix.”
- [T1105] Ingress Tool Transfer – The post-install script downloaded payload binaries from attacker-controlled network locations (cloudcenter[.]top paths) to the victim for execution; “the post-install script … downloads and executes a payload containing the AdaptixC2 agent.”
- [T1547] Boot or Logon Autostart Execution (plist autorun on macOS) – The use of a LaunchAgents plist to establish persistence on macOS; “drops a plist autorun configuration file into this directory.”
- [T1059] Command and Scripting Interpreter – The npm package’s post-install JavaScript was used to perform installation-time scripting to fetch and execute platform-specific binaries; “the post-install script … downloads and executes a payload containing the AdaptixC2 agent.”
Indicators of Compromise
- [Package name] malicious npm package – https-proxy-utils
- [File hashes] package and artifact hashes – DFBC0606E16A89D980C9B674385B448E, B8E27A88730B1248…(additional long hash) and other single package blob hashes
- [URL/Domain] C2 and payload hosting – cloudcenter[.]top/sys/update, cloudcenter[.]top/macos_update_arm, cloudcenter[.]top/macos_update_x64, and other cloudcenter[.]top paths
- [File paths] deployment locations used by installer – C:WindowsTasks (DLL + msdtc.exe copy), Library/LaunchAgents (payload + plist), /tmp/.fonts-unix (Linux binary)
Read more: https://securelist.com/adaptixc2-agent-found-in-an-npm-package/117784/