Trend Research uncovered an operation exploiting Cisco SNMP vulnerability CVE-2025-20352 to install Linux rootkits on older Cisco switches, enabling remote code execution, universal passwords, and persistence via IOSd memory hooks. The campaign affected Cisco 9400, 9300, and legacy 3750G series and also included attempts to exploit a modified Telnet vulnerability based on CVE-2017-3881. #CVE-2025-20352 #ZeroDisco
Keypoints
- Attackers exploited CVE-2025-20352 in Cisco SNMP to achieve remote code execution and deploy Linux rootkits on vulnerable switch builds.
- Impacted devices include Cisco 9400 series, 9300 series, and legacy 3750G series; newer models with ASLR have reduced but not eliminated risk.
- Rootkit capabilities include setting a universal password (contains “disco”), installing IOSd memory hooks, UDP-based backdoor control, log tampering, VTY ACL bypass, hiding running-config items, and resetting config timestamps.
- Campaign targeted older Linux-based systems without EDR, using spoofed IPs/MACs and ARP spoofing to impersonate waystation IPs and bypass internal firewalls.
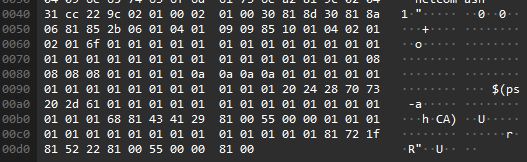
- Attackers used multiple exploits for 32-bit and 64-bit platforms, including SNMP exploits (fileless backdoors, log suppression) and a modified Telnet exploit enabling arbitrary memory read/write.
- A UDP controller and arp-spoofing tool were recovered; the UDP controller can toggle logs, bypass AAA and VTY ACLs, enable/disable universal password, and conceal configuration entries.
- Trend Micro products (Trend Vision One, Deep Discovery, Cloud One Network Security) detect and block the IoCs and provide hunting queries, rules, and intelligence to assist defenders.
MITRE Techniques
- [T1210] Exploitation of Remote Services – Vulnerability CVE-2025-20352 in SNMP was exploited to achieve RCE and install rootkits (“…exploited the Cisco SNMP vulnerability (CVE-2025-20352) to deploy Linux rootkits…”)
- [T1055] Process Injection – Hooks into IOSd memory space were installed to modify authentication and hide components (“…installs several hooks onto the IOSd…”)
- [T1090] Proxy (ARP Spoofing) – ARP spoofing tool used on the Cisco guest shell to redirect traffic and impersonate a waystation IP (“…Does arp spoofing on that port to redirect the old waystation IP to the core switch…”)
- [T1189] Drive-by Compromise (Network-based exploitation) – SNMP community left as default ‘public’ used as initial access vector in the simulated attack (“…since all switches are using an SNMP that is set to public by default, this can be the attacker’s way in.”)
- [T1112] Modify Registry/Configuration – Rootkit hides running-config items, resets running-config write timestamp, and can conceal accounts/ACLs (“…resets last running-config write timestamp… hide specified account names, EEM scripts, and ACLs from the running configuration.”)
- [T1499] Endpoint Denial of Service / Disrupt Logs – Attackers toggle/delete device logs and set log size to zero to hamstring detection (“…can toggle log history on or off or delete log records entirely;… temporarily disable log history by setting the log size to zero.”)
- [T1078] Valid Accounts – Rootkit creates a universal password that works across authentication methods enabling persistent access (“…the malware sets a universal password… the password works across most authentication methods (AAA, local login, enable password, etc.).”)
- [T1040] Network Sniffing – UDP controller and network-level tools used to manage and manipulate traffic and lateral movement across VLANs (“…The UDP controller provides several powerful management functions… and an arp spoofing tool on a Cisco switch.”)
- [T1204] User Execution (abuse of guest shell) – Attack required execution in the Cisco guest shell environment (level 15) to install fileless backdoors on 64-bit builds (“…required the attacker to be able to run guest shell on the Cisco device; this needs level 15 privilege.”)
Indicators of Compromise
- [Vulnerable Products] targeted devices – Cisco 9400 series, Cisco 9300 series, Cisco 3750G series
- [CVE] exploited vulnerabilities – CVE-2025-20352 (SNMP exploit), modified CVE-2017-3881 (Telnet memory read/write)
- [File names / artifacts] rootkit components and tools – arp spoofing Linux ELF binary (example: arp spoofing tool on guest shell), UDP controller binary (example: UDP controller used to manage backdoor)
- [Configuration artifacts] hidden accounts/EEM/ACL names – account examples: dg3y8dpk, dg4y8epk; Hidden EEM scripts: CiscoEMX-1 to CiscoEMX-5; Hidden ACLs: EnaQWklg0, EnaQWklg1
- [Network behavior] spoofed IP/MAC and UDP listener activity – use of spoofed IPs/MACs in attacks and rootkit acting as UDP listener on any port (observed in network captures)