Researchers observed malicious packages on npm, PyPI, and RubyGems using hard-coded Discord webhook URLs to exfiltrate sensitive files and host metadata during install or runtime. These packages collect configuration files, environment secrets, /etc/passwd, public IPs, and other system details and POST them to attacker-controlled Discord channels for telemetry or C2. #DiscordWebhook #sqlcommenter_rails
Keypoints
- Malicious packages across ecosystems (npm, PyPI, RubyGems) embed hard-coded Discord webhook URLs to exfiltrate data instead of using attacker-controlled servers.
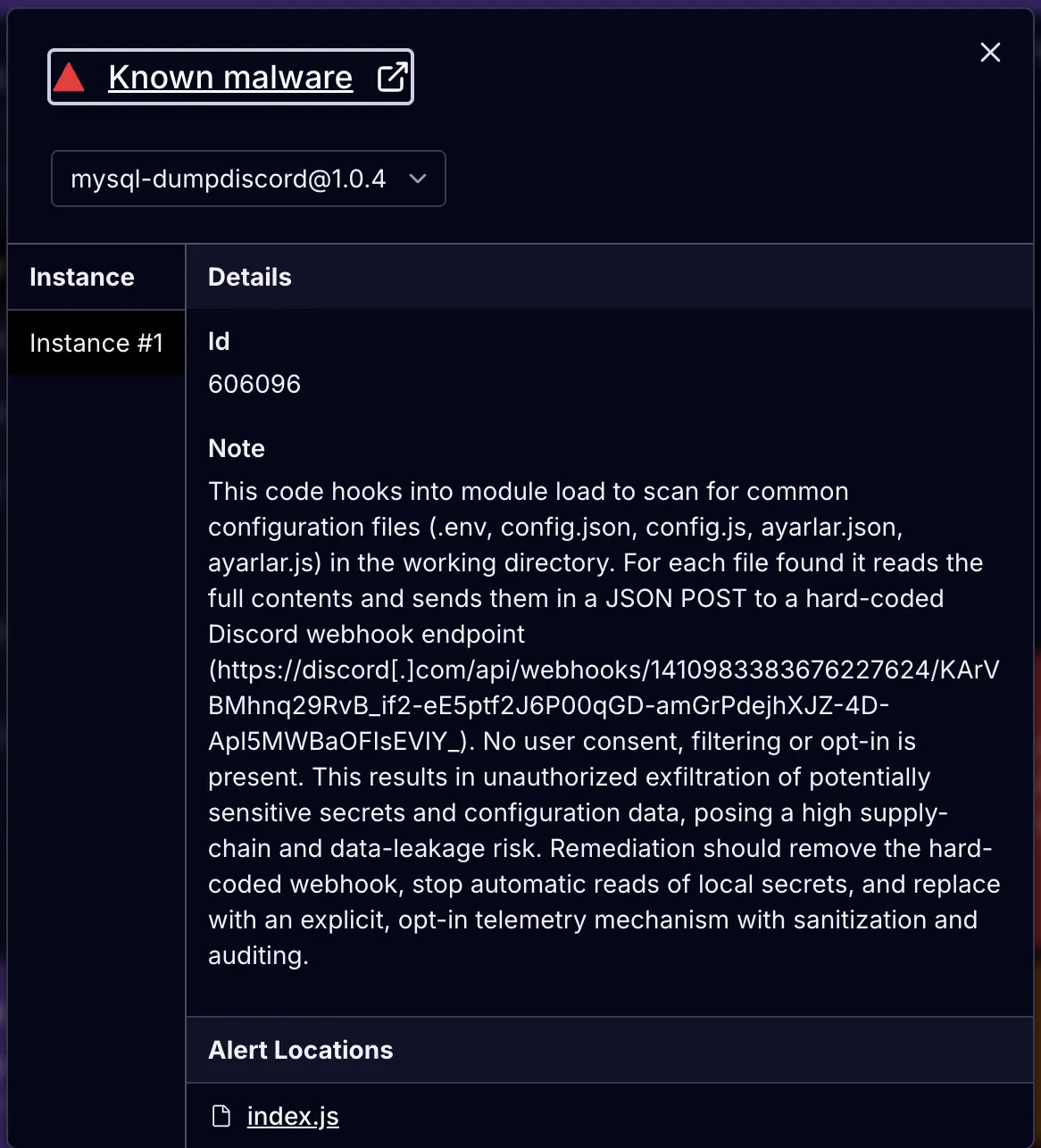
- Examples include an npm package (mysql-dumpdiscord) that reads config files (.env, config.json, ayarlar.js) and posts file contents to a Discord webhook.
- A PyPI package overrides setuptools install to POST an install-time notification to a Discord webhook, demonstrating a supply-chain install-time exfiltration risk.
- The RubyGem (sqlcommenter_rails) collects extensive host data ( /etc/passwd, DNS servers, hostname, user, current/home dir, public IP) and sends it to a webhook.
- Webhook URLs require no authentication beyond possession and ride over HTTPS, making them effective, low-cost exfiltration/C2 channels that often bypass simple network or signature blocking.
- Defensive recommendations: treat webhooks as potential data-loss channels, enforce egress controls and allow-lists, pin and vet dependencies, scan installs/PRs for network calls and secrets access, and rotate developer credentials.
- Socket tools (GitHub App, CLI, Firewall, browser extension, MCP) are positioned to detect hard-coded webhooks, install-time hooks, and outbound network calls to block or flag these malicious packages.
MITRE Techniques
- [T1005 ] Data from Local System – Packages read local files like config.json, .env, ayarlar.js, and /etc/passwd to collect sensitive content (“reads the file contents” / “File.read(‘/etc/passwd’)”).
- [T1016 ] System Network Configuration Discovery – Ruby example reads DNS servers from /etc/resolv.conf to enumerate network configuration (“File.readlines(‘/etc/resolv.conf’).select { |line| line.start_with?(‘nameserver’) }”).
- [T1020 ] Automated Exfiltration – Exfiltration is automated by code that POSTs collected data to hard-coded Discord webhooks during install or runtime (“POSTs that message as JSON to the Discord webhook”).
- [T1033 ] Account Discovery – The Ruby script collects the current username and home directory to identify accounts on the host (“Etc.getlogin || ‘Unknown’”; “Dir.home”).
- [T1059 ] Command and Scripting Interpreter – Malicious behavior is implemented via scripting languages and install-time hooks that execute code (Node.js modules, Python setuptools override, Ruby scripts) to perform collection and network calls (“overrides the setuptools install command to run a post-install side effect”).
- [T1059.006 ] Command and Scripting Interpreter: Python – The PyPI example uses Python setuptools and urllib to run code at install time and send webhook POSTs (“urllib.request.urlopen(req)”).
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – npm examples use Node.js to read files and send HTTP POSTs to Discord webhooks (“fs.readFileSync” and “fetch(WEBHOOK_URL, { method: ‘POST’ })”).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Exfiltration uses HTTPS POST requests to Discord webhook endpoints (“https://discord[.]com/api/webhooks/…”).
- [T1082 ] System Information Discovery – The RubyGem collects system information like hostname, current directory, home directory, and user info (“Socket.gethostname”, “Dir.pwd”, “Dir.home”).
- [T1119 ] Automated Collection – Packages automatically gather multiple data items (files, system metadata, IP) into a formatted payload before exfiltration (“Collect all tracking data” and formatted_message).
- [T1195.002 ] Supply Chain Compromise: Compromise Software Supply Chain – Malicious packages on official registries execute during install or are distributed as dependencies, enabling wide-scale supply chain compromise (“executes during install without user consent” / “supply chain risk”).
- [T1552.001 ] Unsecured Credentials: Credentials In Files – Packages target common credential storage files (.env, config files) to harvest API keys and credentials (“targets configuration files, like config.json, .env, ayarlar.js”).
- [T1567 ] Exfiltration Over Web Service – Exfiltration occurs over web services (Discord webhooks and other modern webhook providers like Slack, Telegram, GitHub) to transmit stolen data (“abuse of Discord webhooks as C2” / “POSTs the same text as JSON to the webhook”).
Indicators of Compromise
- [Webhook URLs ] Hard-coded Discord webhook endpoints used for exfiltration – https://discord[.]com/api/webhooks/1410983383676227624/KArVBMhnq29RvB_if2-eE5ptf2J6P00qGD-amGrPdejhXJZ-4D-Apl5MWBaOFIsEVlY_, https://discord[.]com/api/webhooks/1410258094511882250/fPTbDPbFfrSaOKDwXDfeqfwlKlhdS5tpev8nD7giRFhAldmRpJaGlI6Y5IWqOpdxYNbx (multiple other webhook URLs listed).
- [File names ] Targeted configuration or sensitive files – config.json, .env, ayarlar.js, ayarlar.json (attacker reads and posts their contents).
- [Package names / authors ] Malicious packages and actor handles – malinssx / maladicus (PyPI examples), mysql-dumpdiscord (npm example), sqlcommenter_rails (RubyGem); actor alias sdadasda232323 referenced.
- [Network endpoints ] External services contacted for telemetry – https://api.ipify.org used to determine public IP (observed in Ruby script).
Read more: https://socket.dev/blog/weaponizing-discord-for-command-and-control