Trend Micro and WhoisXML API investigations into the TAOTH Campaign found targeted social-engineering lures (fake software updates, cloud storage, and login pages) aimed at dissidents, journalists, researchers, and leaders across East Asia and overseas Taiwanese communities. The joint analysis identified domains, subdomains, and IPs tied to the campaign and enriched IoCs with WHOIS, DNS history, geolocation, and traffic-sample data to prioritize eight IoCs for further action. #TAOTH #auth-web[.]com
Keypoints
- Trend Micro named the intrusion cluster the “TAOTH Campaign,” which used fake update, cloud storage, and login page decoys to deliver malware and harvest credentials targeting Traditional Chinese users and dissidents.
- The initial Trend Micro report listed two domains, four subdomains, and five IP addresses as IoCs; WhoisXML API focused analysis on eight of those IoCs (three domains, five IPs).
- IASC DNS traffic samples showed 68 unique client IPs queried auth-web[.]com (89 DNS queries, 14–27 Aug 2025) and one potential victim IP communicated with IP IoC 45[.]32[.]117[.]177.
- First Watch feed flagged onedrive365-jp[.]com as likely to turn malicious 281 days before it was reported; WHOIS queries showed the three analyzed domains were created between Oct 2024 and Apr 2025 and used different registrars.
- DNS Chronicle and bulk IP geolocation revealed rich DNS histories: the five IP IoCs resolved to domains 447 times in total and were geolocated across the U.S., Russia, and Switzerland and hosted by multiple ISPs (including Amazon).
- WHOIS History and Reverse WHOIS queries produced 47 unique historical WHOIS emails (five public addresses collated), which expanded to 303 email-connected domains after filtering duplicates.
- The report provides downloadable supplemental artifacts and urges further investigation since some flagged entities may later be reclassified.
MITRE Techniques
- [T1204] User Execution – Attackers used fake software update, cloud storage, and login pages to trick victims into executing malicious content or providing credentials: ‘used fake software update, cloud storage, and login pages to distribute malware and collect sensitive information.’
- [T1598] Phishing for Information – Credential-harvesting decoys and login pages were employed to collect sensitive information from targeted users: ‘used … login pages to distribute malware and collect sensitive information.’
- [T1588] Obtain Capabilities via Operational Infrastructure – The campaign relied on domains, subdomains, and IP infrastructure (some possibly legitimate but compromised) to host lures and payloads: ‘identified two domains, four subdomains, and five IP addresses as indicators of compromise (IoCs).’
- [T1078] Valid Accounts (Account Discovery/Use) – Use of cloud-storage and login page impersonation indicates attempts to harvest or reuse legitimate credentials: ‘used … cloud storage, and login pages to distribute malware and collect sensitive information.’
Indicators of Compromise
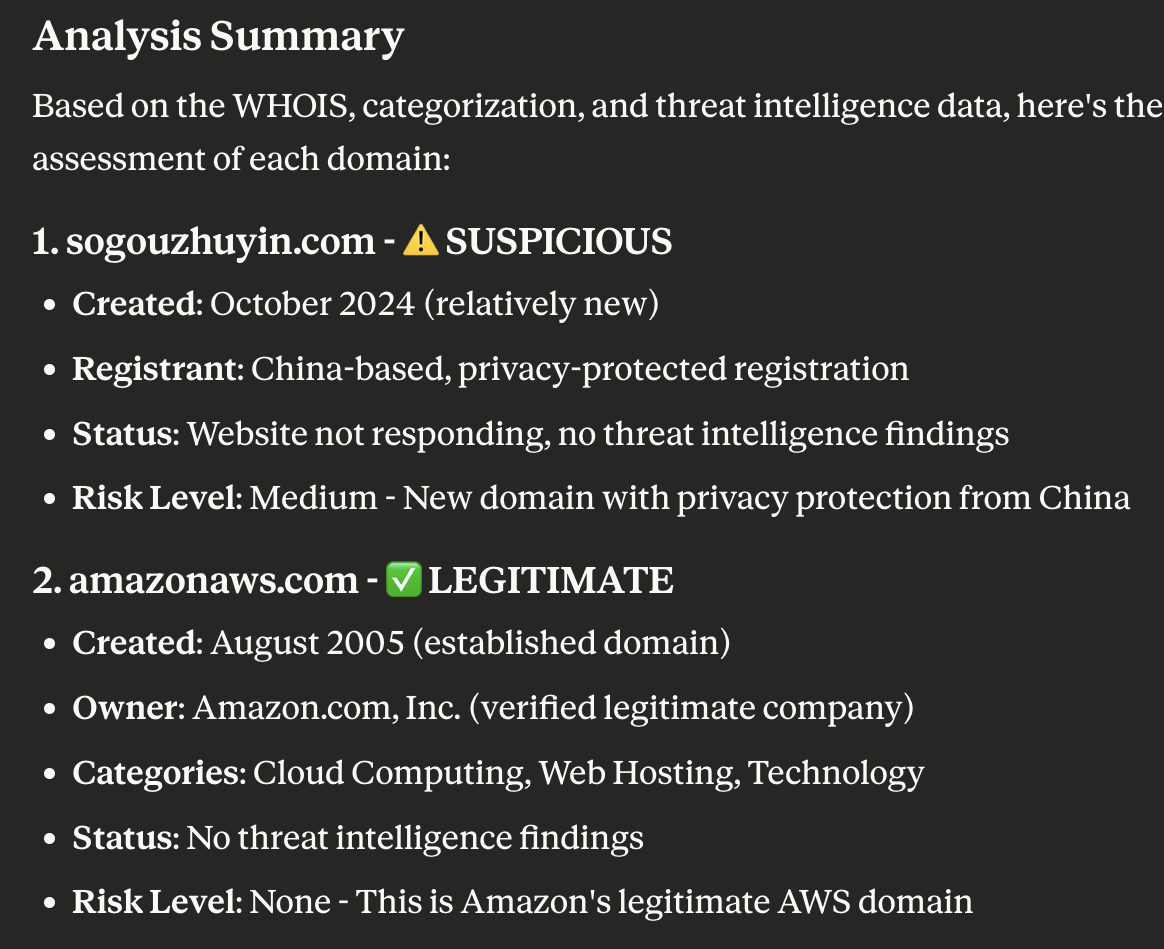
- [Domain] Domains used as lures or infrastructure – auth-web[.]com (malicious), onedrive365-jp[.]com (flagged as likely to turn malicious), sogouzhuyin[.]com
- [Subdomain] Compromised or impersonating subdomains – amazonaws.com (as a hosting platform observed in subdomains), and other subdomains tied to listed domains
- [IP Address] IPs used in campaign infrastructure and DNS resolutions – 45[.]32[.]117[.]177 (communicated with a potential victim), 154[.]90[.]62[.]210, and 192[.]124[.]176[.]51 (and 2 more IPs)
- [Email addresses] Historical WHOIS emails linked to domains – 5 public email addresses extracted from WHOIS history (expanded to 303 email-connected domains overall)
- [Traffic data] Client/ASN activity from IASC samples – 68 unique client IPs under one ASN queried auth-web[.]com (89 DNS queries between 14–27 Aug 2025)
Read more: https://circleid.com/posts/thumbing-through-the-dns-trail-of-the-taoth-campaign