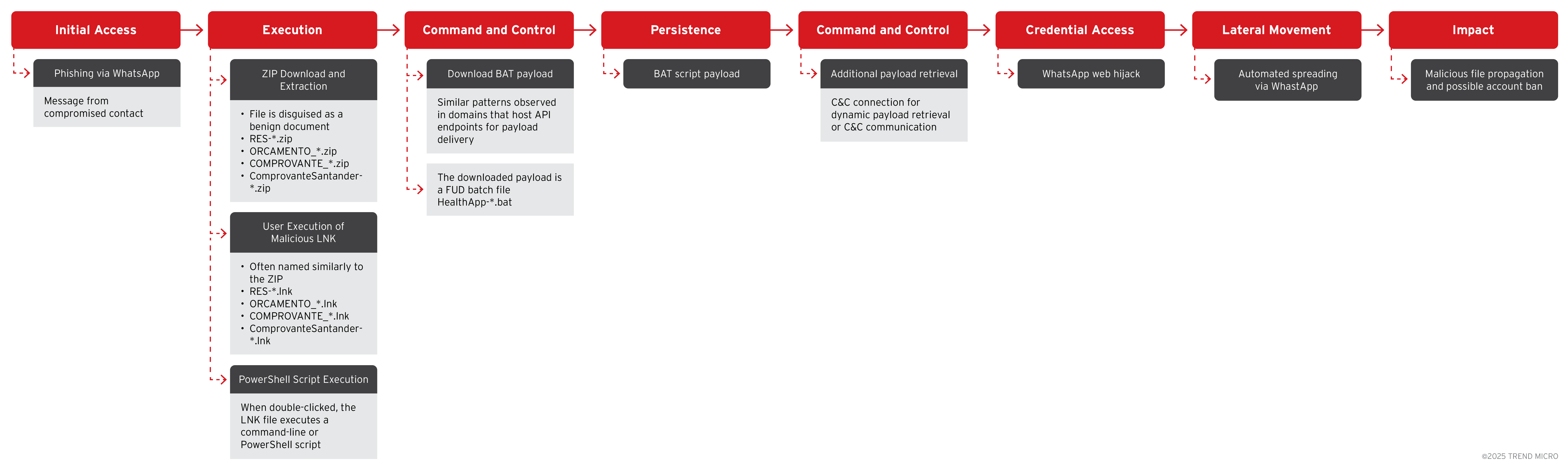
Trend Research identified the SORVEPOTEL campaign spreading via WhatsApp and malicious ZIP attachments that, when opened on Windows desktops, establish persistence and hijack WhatsApp Web sessions to automatically forward the ZIP to all contacts and groups. The campaign is highly active in Brazil, targets enterprises and public-sector organizations, and uses LNK shortcuts, PowerShell/Base64 obfuscation, and typo-squatted domains for rapid propagation. #SORVEPOTEL #WhatsAppWeb
Keypoints
- SORVEPOTEL spreads through convincing WhatsApp messages and ZIP attachments that instruct users to open the file on a PC, indicating an enterprise targeting focus.
- When executed, the ZIP extracts a .LNK shortcut that runs obfuscated PowerShell/command scripts to download a BAT payload and establish persistence via the Windows Startup folder.
- The malware detects active WhatsApp Web sessions and leverages them to automatically send the same malicious ZIP to all contacts and groups, enabling rapid propagation and causing account bans from spam activity.
- Trend Research telemetry shows a regional concentration in Brazil (457 of 477 detected cases) and impact across government, public services, manufacturing, technology, education, and construction sectors.
- Delivery and C2 infrastructure use typo-squatted and obfuscated domains (e.g., sorvetenopoate[.]com and similar variants) and multiple C2 servers to download and execute additional payloads in memory.
- Current evidence suggests the campaign’s primary objective is widespread distribution rather than data theft or encryption, though similar Brazilian campaigns have targeted financial data previously.
- Defensive recommendations include disabling auto-downloads in WhatsApp, restricting file transfers from personal apps on managed devices, strong user awareness training, and using endpoint controls and app whitelisting.
MITRE Techniques
- [T1204] User Execution – Malicious ZIP attachments and social-engineered messages prompt users to “baixa o zip no PC e abre” (download the ZIP on PC and open it) to initiate the infection.
- [T1202] Indirect Command Execution – .LNK shortcut files launch command-line or PowerShell scripts that retrieve and execute payloads from attacker-controlled domains: “…decrypted command retrieves a malicious script from a specified URL and executes it in memory using the Invoke-Expression (IEX) function.”
- [T1105] Ingress Tool Transfer – The PowerShell/BAT scripts download additional payloads and components from C2 servers and attacker domains using Net.WebClient and execute them in memory: “…the script downloads content from this address, which is then immediately executed in memory via Invoke-Expression.”
- [T1547.001] Boot or Logon Autostart Execution: Registry/Startup Folder – The BAT persistence mechanism copies itself into the Windows Startup folder to run automatically at boot.
- [T1071] Application Layer Protocol – Malware leverages active WhatsApp Web sessions (web-based application protocol usage) to propagate by sending the malicious ZIP to all contacts and groups.
- [T1036] Masquerading – Use of benign-looking filenames (e.g., “RES-20250930_112057.zip”, “ORCAMENTO_114418.zip”) and typo-squatted domains (e.g., sorvetenopotel variants) to blend malicious infrastructure with legitimate traffic.
- [T1027] Obfuscated Files or Information – Use of Base64 encoded PowerShell (-enc), encoded/obfuscated commands, and hidden window execution (-windowstyle hidden) to evade detection: “…runs in hidden mode (-w hidden) … with its parameters provided in Base64 encoded form (-enc) for added obfuscation.”
Indicators of Compromise
- [Domain ] Malicious delivery/C2 domains – sorvetenopoate[.]com, sorvetenoopote[.]com (and several typo-squatted variants such as etenopote[.]com, expahnsiveuser[.]com)
- [File Name ] Malicious attachment examples – RES-20250930_112057.zip, ORCAMENTO_114418.zip (also observed: COMPROVANTE_20251001_094031.zip and ComprovanteSantander-75319981.682657420.zip)
- [File Type ] Dropped/executed artifacts – .LNK shortcut files that execute obfuscated commands, and .BAT batch files that establish persistence (examples: LNK shortcut inside ZIP, BAT downloaded/executed by LNK)
- [IP Address ] Hunting/outbound connections referenced – dst:109.176.30.141, dst:165.154.254.44 (Trend Vision One hunting query also lists dst:23.227.203.148 and dst:77.111.101.169)
- [Email Subject/Sender ] Phishing email lures – subjects such as “Documento de Rafael B”, “Zip”, “Extrato” and senders used with names mimicking legitimate sources (example: emails distributing COMPROVANTE_20251001_094031.zip)
Read more: https://www.trendmicro.com/en_us/research/25/j/self-propagating-malware-spreads-via-whatsapp.html