Fox-IT and NCC Group investigated a Lazarus subgroup using three RATs—PondRAT5, ThemeForestRAT, and RemotePE—targeting financial and cryptocurrency organizations and identified 19 domains and two IP addresses as IoCs. WhoisXML API and IASC traffic analysis expanded the infrastructure findings to include additional malicious IPs, domain histories, and email-linked domains. #PondRAT5 #ThemeForestRAT
Keypoints
- Fox-IT and NCC Group analyzed three Lazarus RATs (PondRAT5, ThemeForestRAT, RemotePE) in a report titled “Three Lazarus RATs Coming for Your Cheese.”
- Researchers identified 19 domain IoCs and two IP IoCs tied to the campaigns, with detailed DNS and WHOIS histories.
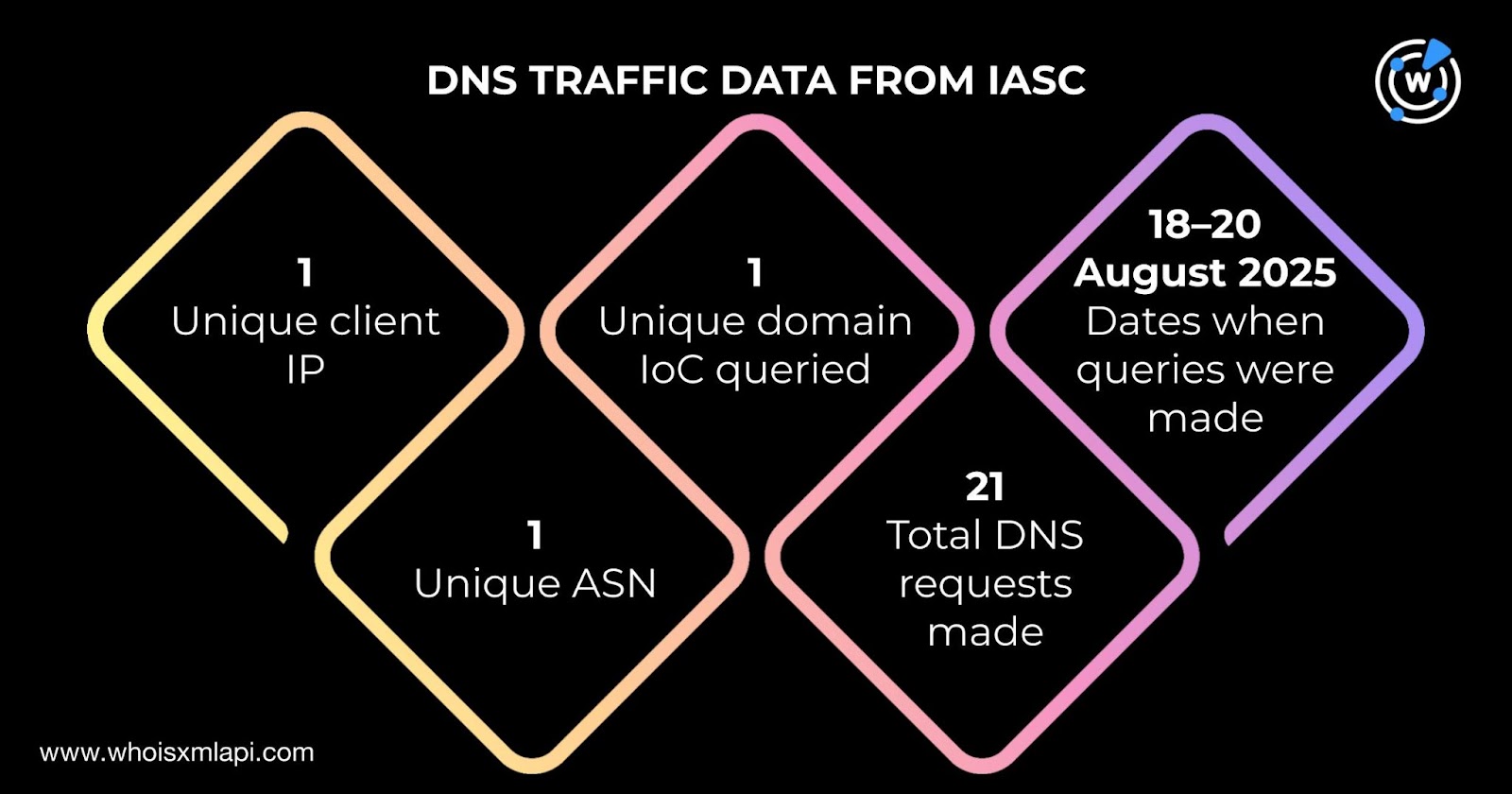
- IASC sample traffic showed one client IP queried a domain IoC via 21 DNS queries (18–20 Aug 2025) and two alleged victim IPs communicated with two IP IoCs under different ASNs.
- WhoisXML API and First Watch data found one domain (keondigital[.]com) flagged likely to turn malicious 189 days before its formal tagging on 1 Sept 2025.
- WHOIS queries revealed eight of the 19 domains had current records, created between 18 Aug 2023 and 18 Jul 2025, with clustering of creation dates suggesting campaign linkage.
- DNS Chronicle showed the 19 domains had 665 domain-to-IP resolutions since 2017, and the two IP IoCs had 685 IP-to-domain resolutions, indicating long-term infrastructure use.
- Additional artifact discovery returned one email-connected domain, nine additional IP addresses (eight flagged malicious), 57 IP-connected domains, and 259 string-connected domains.
MITRE Techniques
- [T1105 ] Ingress Tool Transfer – The RATs were delivered and managed via infrastructure and artifacts including domains and IPs used to transfer and stage remote access tools (“Three Lazarus RATs Coming for Your Cheese”).
- [T1071 ] Application Layer Protocol – C2 communications observed in DNS queries and network traffic (IASC sample: “one unique client IP address … queried one unique domain IoC via 21 DNS queries between 18 and 20 August 2025”).
- [T1588 ] Obtain Capabilities – Use of multiple RAT variants (PondRAT5, ThemeForestRAT, RemotePE) and related tooling indicates capability acquisition and reuse across campaigns (“uses different remote access Trojans (RATs) known as ‘PondRAT5,’ ‘ThemeForestRAT,’ and ‘RemotePE’”).
- [T1583 ] Acquire Infrastructure – Actors registered and reused domains, IPs, and hosting services across years; WHOIS and DNS histories show domain creation and resolution patterns supporting infrastructure acquisition (“They had 665 domain-to-IP resolutions over time since 5 February 2017”).
- [T1598 ] Phishing for Information / External Remote Services – Email-connected domain discovery and historical WHOIS email ties suggest use of email-linked infrastructure for victim engagement or registration (“14 had 24 unique email addresses in their historical WHOIS records … one email-connected domain—kmc-ksa[.]com”).
Indicators of Compromise
- [Domains ] RAT and campaign infrastructure – keondigital[.]com, pypilibrary[.]com, arcashop[.]org (and 16 more domains)
- [IP addresses ] C2 and hosting – 192[.]52[.]166[.]253, (second IP listed in report) and 9 additional IPs (eight flagged malicious)
- [File/Artifact names ] RAT family names as artifact markers – PondRAT5, ThemeForestRAT, RemotePE
- [Email addresses ] Registrant/historical WHOIS emails – one public email linked to kmc-ksa[.]com and 23 other historical emails across IoCs
- [Autonomous System Numbers (ASNs) ] Network context from IASC traffic – single ASN for client IP queries and two unique ASNs for alleged victim IP communications
Read more: https://circleid.com/posts/deep-dive-3-lazarus-rats-caught-in-our-dns-trap