ESET researchers discovered two undocumented Android spyware families—Android/Spy.ProSpy and Android/Spy.ToSpy—that impersonate Signal and ToTok to trick users into manually installing malicious APKs from deceptive websites, with confirmed targeting of users in the United Arab Emirates. Both families persist on devices and exfiltrate sensitive data (including ToTok .ttkmbackup files) to active C2 servers, and known samples/domains and hashes have been shared. #Android/Spy.ProSpy #Android/Spy.ToSpy
Keypoints
- Two previously undocumented Android spyware families were identified: Android/Spy.ProSpy (impersonating Signal plugin and ToTok Pro) and Android/Spy.ToSpy (impersonating ToTok).
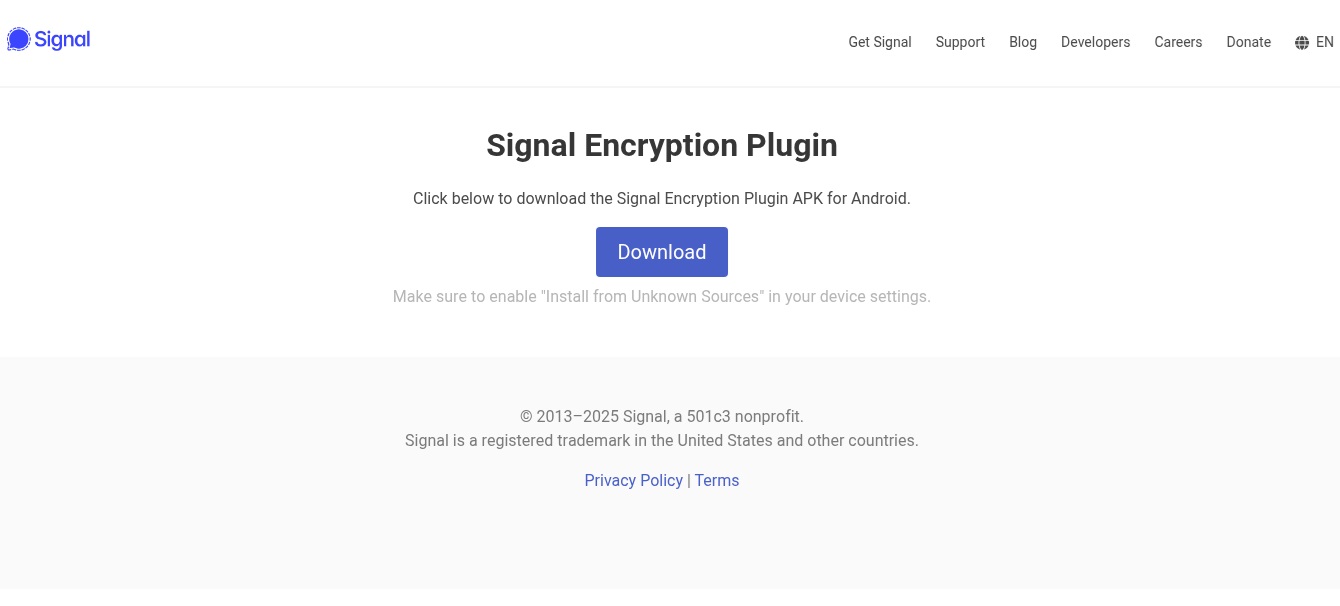
- Both families are distributed only via manual installation from deceptive third‑party websites (phishing pages and fake app stores), not official app stores.
- ProSpy and ToSpy request broad permissions (contacts, SMS, storage) and exfiltrate device info, contacts, SMS (ProSpy), installed apps (ProSpy), and many file types including ToTok .ttkmbackup files (ToSpy).
- Both families implement persistence via foreground services, AlarmManager-based restart, and BOOT_COMPLETED broadcast handling to survive reboots and service termination.
- ToSpy uses AES‑CBC with a hardcoded key (p2j8w9savbny75xg) to encrypt exfiltrated data and contacts C2 endpoints over HTTPS; several C2 and distribution domains remain active, indicating ongoing campaigns.
- ESET observed regional targeting toward the UAE (domain name cues, sample metadata, telemetry), and multiple samples share developer certificates and code reuse suggesting a single actor per family.
- ESET shared findings with Google (Play Protect blocks known versions); users are advised not to enable unknown-source installs or download apps outside official stores.
MITRE Techniques
- [T1660 ] Phishing – Android ToSpy and ProSpy have been distributed using dedicated websites impersonating legitimate services. [‘Android ToSpy and ProSpy have been distributed using dedicated websites impersonating legitimate services.’]
- [T1603 ] Scheduled Task/Job – Android ToSpy and ProSpy use AlarmManager to restart the foreground service. [‘It uses Android’s AlarmManager to repeatedly restart the foreground service…’]
- [T1398 ] Boot or Logon Initialization Scripts – Android ToSpy and ProSpy receive the BOOT_COMPLETED broadcast intent to activate at device startup. [‘Boot Persistence with BroadcastReceiver for BOOT_COMPLETED: The component tracks system boot events.’]
- [T1541 ] Foreground Persistence – Android ToSpy and ProSpy use foreground persistence to keep a service running. [‘The spyware runs a foreground service that displays persistent notification and is treated by Android as a priority process.’]
- [T1420 ] File and Directory Discovery – Android ToSpy and ProSpy can list files and directories on external storage. [‘Android ToSpy and ProSpy can list files and directories on external storage.’]
- [T1418 ] Software Discovery – Android ProSpy obtains a list of installed apps. [‘Installed apps: List of all installed applications.’]
- [T1426 ] System Information Discovery – Android ProSpy can extract information about the device, including device model, device ID, and common system information. [‘Device Information: Extracts hardware, OS details, and public IP address retrieved via a request to ip-api.com/json.’]
- [T1533 ] Data from Local System – Android ToSpy and ProSpy can exfiltrate files from a device. [‘ToSpy and ProSpy search for and exfiltrate files and categorize them based on MIME types…’]
- [T1636.003 ] Protected User Data: Contact List – Android ToSpy and ProSpy can extract the device’s contact list. [‘Contact list: Harvests names, phone numbers, and other contact metadata.’]
- [T1636.004 ] Protected User Data: SMS Messages – Android ProSpy can extract SMS messages. [‘Stored SMS messages: Collects all accessible SMS messages.’]
- [T1521.001 ] Standard Cryptographic Protocol: Symmetric Cryptography – Android ToSpy encrypts exfiltrated data using AES encryption. [‘All exfiltrated data is encrypted using AES encryption in CBC (Cipher Block Chaining) mode with a hardcoded key (p2j8w9savbny75xg).’]
- [T1646 ] Exfiltration Over C2 Channel – Android ToSpy and ProSpy exfiltrate data using HTTPS. [‘The data is then sent to a C&C server using an HTTPS POST request.’]
Indicators of Compromise
- [File Hash ] Malicious APK samples – 03FE2FCF66F86A75242F6112155134E66BC586CB (e18683bc061e888f…e326a.apk), B22D58561BB64748F0D2E57B06282D6DAF33CC68 (totok_v1.8.8.411.apk).
- [File Hash ] Additional malicious APKs – CE378AE427E4BD70EAAED204C51811CD74F9A294 (v1_8_7_408_totok.apk), 154D67F871FFA19DCE1A7646D5AE4FF00C509EE4 (signal-encryption-plugin.apk), and several more hashes listed in ESET’s repo (and multiple other hashes).
- [Domain ] Distribution/C2 domains – spiralkey[.]co (ToSpy update/C2), store.appupdate[.]ai (ToSpy distribution mimicking Galaxy Store), signal.ct[.]ws (ProSpy distribution).
- [IP Address ] Known infrastructure – 152.89.29[.]73 (spiralkey[.]co C2), 5.42.221[.]106 (store.latestversion[.]ai distribution domain), 86.105.18[.]13 (noblico[.]net ToSpy C2).
- [File Name / Extension ] Targeted filenames/extensions – .ttkmbackup (ToTok backup files targeted by ToSpy), totok_pro_release_v2_8_8_10330.apk (example malicious APK filename).