Guardio uncovered ClickFix, a browser-based stealer that used fake CAPTCHA pages to trick users into executing a malicious PowerShell command and exfiltrate credentials, and published 172 IoCs including 156 domains and 16 IPs. WhoisXML API’s analysis expanded those IoCs—finding thousands of related domains, IPs, registrant- and email-linked domains, and early warnings for 30 domains—and linked broad DNS and WHOIS artifacts to the campaign. #ClickFix #Guardio
Keypoints
- ClickFix is a browser-based stealer that evolved from fake browser updates by presenting fake CAPTCHA pages which copy a malicious PowerShell command when users click “Verify.”
- Guardio published 172 IoCs for ClickFix comprising 156 domains and 16 IP addresses.
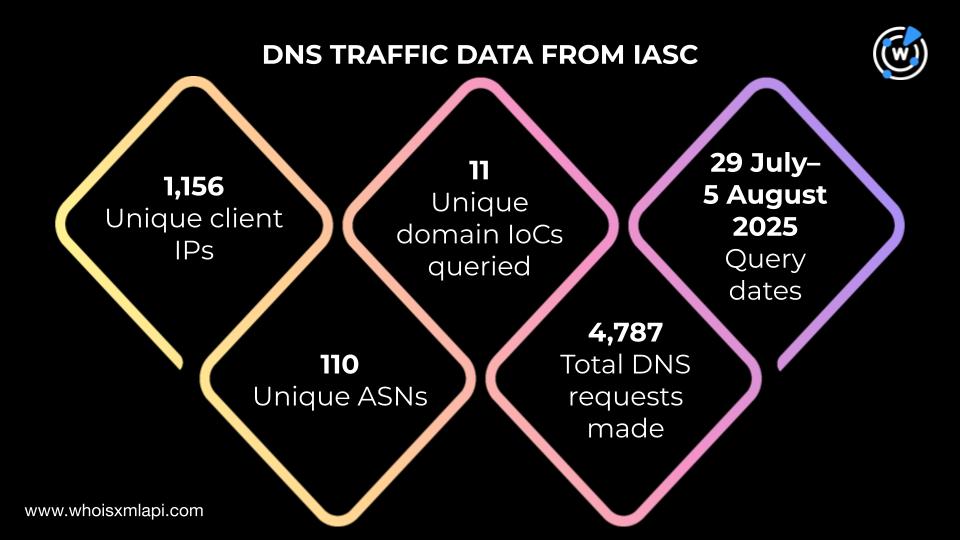
- WhoisXML API analysis of IASC DNS traffic found 1,156 unique client IPs communicating with 11 domain IoCs and two alleged victim IPs communicating with three IP IoCs.
- First Watch data showed 30 of the identified domain IoCs were flagged as likely-to-turn-malicious 51–209 days before formal reporting.
- WhoisXML API expanded the IoC set: 289 registrant-connected domains, 193 email-connected domains (one weaponized), 133 additional IPs (86 malicious), 1,037 IP-connected domains (28 malicious), and 3,412 string-connected domains (30 malicious).
- Most domain IoCs (88 of 125 with WHOIS) were newly registered in 2025, and top registrars included Namecheap and PDR; DNS Chronicle revealed extensive historical domain-to-IP and IP-to-domain resolutions for many IoCs.
- Cluster analysis found multiple IoCs resolving to Cloudflare IP addresses (example set 104.21.16.1–104.21.112.1) and several IPs first observed or configured in May 2025, indicating temporal commonalities.
MITRE Techniques
- [T1204] User Execution – The campaign relied on users clicking a fake CAPTCHA “Verify” button which resulted in a malicious PowerShell command being copied and executed: ‘…when users clicked the Verify button, which copied a malicious PowerShell command for its execution…’
- [T1059.001] Command and Scripting Interpreter: PowerShell – A malicious PowerShell command was executed on victims’ systems to perform theft and exfiltration: ‘…which copied a malicious PowerShell command for its execution.’
- [T1537] Transfer Data to Cloud Account / [T1041] Exfiltration Over C2 Channel – The payload exfiltrated account credentials and other data from victims’ computers: ‘…it exfiltrated victims’ account credentials and other data from their computers.’
- [T1078] Valid Accounts (credential harvesting) – The malware collected account credentials from infected systems: ‘…it exfiltrated victims’ account credentials…’
- [T1588] Acquire Infrastructure – Threat actors used large numbers of newly registered domains and multiple IPs/registrars to host the campaign infrastructure: ‘…a majority, 88 to be exact, were created in 2025, hinting that the threat actors preferred to use newly registered domains (NRDs).’
Indicators of Compromise
- [Domain ] ClickFix delivery and infrastructure examples – companystarlink[.]com, companybonuses[.]org (and 154 more domains identified by Guardio)
- [IP address ] Identified malicious hosts and resolutions – 181[.]174[.]164[.]117, 88[.]119[.]175[.]52 (and 14 more IPs)
- [Registrant-connected domains ] Domains sharing registrant names linked to IoCs – 289 registrant-connected domains discovered via Reverse WHOIS (examples include domains tied to 11 registrant names)
- [Email-connected domains ] Domains linked by WHOIS emails with one weaponized example – znm[.]lol, plus 192 other email-connected domains
- [Cloudflare IP set ] Shared hosting/resolution evidence – 104[.]21[.]16[.]1, 104[.]21[.]32[.]1 used by fepez[.]run, gfddx[.]run, homeeick[.]com in May 2025
- [Historical DNS resolutions ] Domains with long domain-to-IP histories – aasiwins[.]com (380 resolutions, first 5 Feb 2017), appmacosx[.]com (29 resolutions, first 5 Feb 2017)
Read more: https://circleid.com/posts/cross-examining-the-captchageddon-brought-on-by-clickfix