DeceptiveDevelopment is a North Korea-aligned group using sophisticated social engineering—fake recruiter profiles and the ClickFix technique—to deliver multiplatform malware like BeaverTail, InvisibleFerret, WeaselStore, TsunamiKit, Tropidoor, and AkdoorTea targeting developers and crypto-related projects. Research links their operations to North Korean IT worker fraud campaigns (WageMole), showing shared tools, stolen identities, and operational overlap between malware-driven campaigns and employment-fraud schemes. #DeceptiveDevelopment #TsunamiKit
Keypoints
- DeceptiveDevelopment leverages fake recruiter profiles and staged coding challenges to deliver trojanized code repositories that trigger initial-stage malware like BeaverTail.
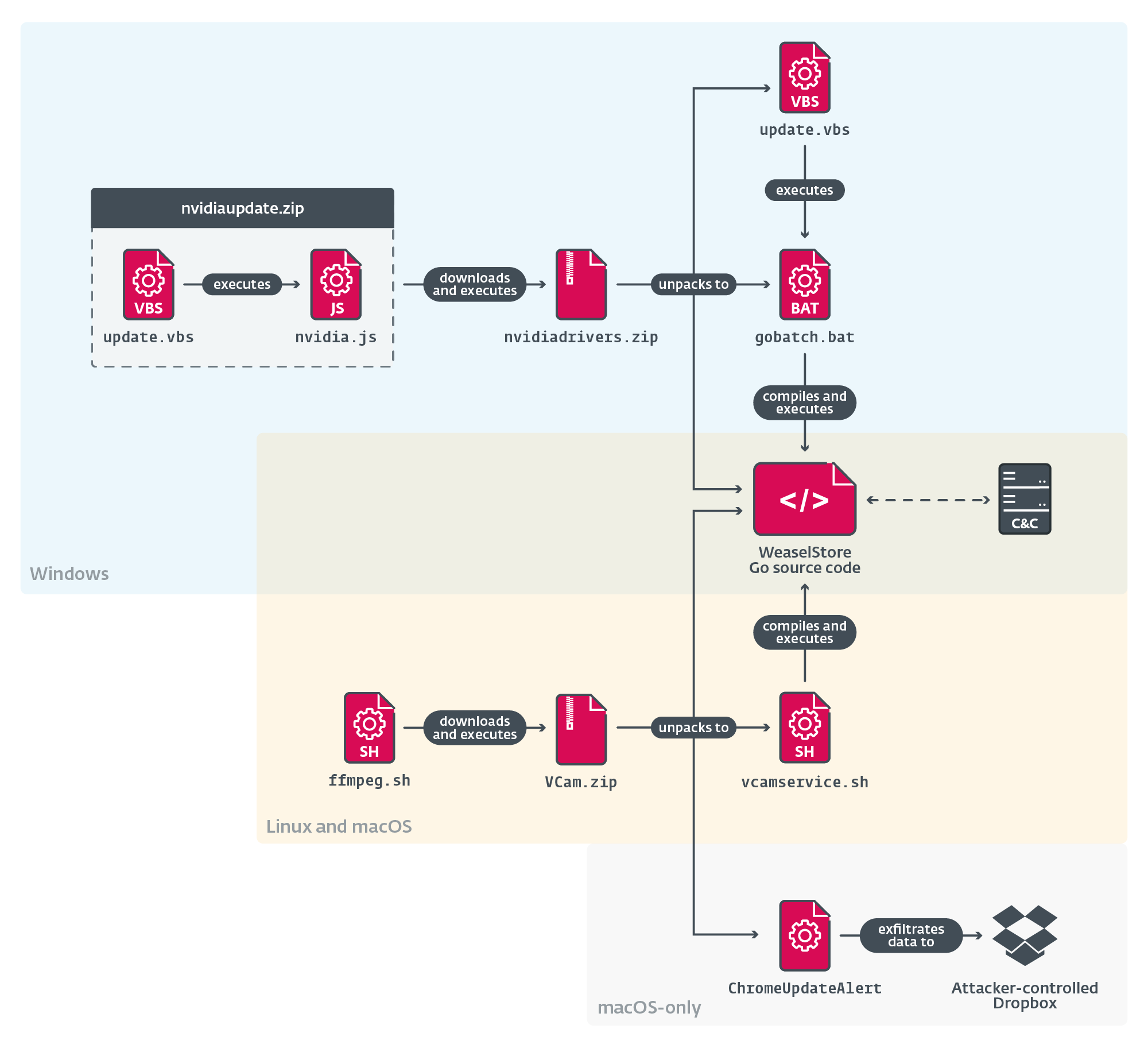
- The group uses a multiplatform toolset: BeaverTail, InvisibleFerret (Python RAT), WeaselStore (Go/Python infostealer/RAT), and the complex .NET TsunamiKit, plus Windows-native backdoors such as Tropidoor and AkdoorTea.
- ClickFix is a notable social-engineering initial-access technique that coerces victims into pasting commands that download and execute malware across macOS, Windows, and Linux.
- Operational links between DeceptiveDevelopment and North Korean IT worker campaigns (WageMole) are supported by shared accounts, stolen identities, and OSINT revealing recruitment, work schedules, and proxy interviewing practices.
- TsunamiKit appears to be a modification of an older dark web project (Nitro Labs) with cryptocurrency-mining and persistence features, predating DeceptiveDevelopment and indicating reuse of available codebases.
- Tropidoor shares substantial code overlap with Lazarus-era PostNapTea, suggesting code sharing or reuse among North Korea-aligned actors and raising ties to more APT-oriented toolsets.
- DeceptiveDevelopment operations emphasize scale and creative social engineering over pure technical sophistication, blurring lines between cybercrime and APT-style activity.
MITRE Techniques
- [T1589 ] Gather Victim Identity Information – DeceptiveDevelopment steals victims’ credentials to be used by WageMole in consequent social engineering. Quote: ‘DeceptiveDevelopment steals victims’ credentials to be used by WageMole in consequent social engineering.’
- [T1585.001 ] Establish Accounts: Social Media Accounts – Fake recruiter accounts created on LinkedIn, Upwork, Freelancer.com, etc. Quote: ‘Fake recruiter accounts created on LinkedIn, Upwork, Freelancer.com, etc.’
- [T1586 ] Compromise Accounts – Hijacked GitHub and social media accounts used to distribute malware. Quote: ‘Hijacked GitHub and social media accounts used to distribute malware.’
- [T1566.001 ] Phishing: Spearphishing Attachment – Fake job offers include attachments or links to malicious projects. Quote: ‘Fake job offers include attachments or links to malicious projects.’
- [T1566.002 ] Phishing: Spearphishing Link – ClickFix technique uses deceptive links to fake troubleshooting guides. Quote: ‘ClickFix technique uses deceptive links to fake troubleshooting guides.’
- [T1204.001 ] User Execution: Malicious Link – Victims are lured to fake job interview sites (e.g., ClickFix) that initiate malware download. Quote: ‘Victims are lured to fake job interview sites (e.g., ClickFix) that initiate malware download.’
- [T1204.002 ] User Execution: Malicious File – Trojanized coding challenges contain variants of BeaverTail. Quote: ‘Trojanized coding challenges contain variants of BeaverTail.’
- [T1059 ] Command and Scripting Interpreter – DeceptiveDevelopment uses VBS, Python, JavaScript, and shell commands for execution. Quote: ‘DeceptiveDevelopment uses VBS, Python, JavaScript, and shell commands for execution.’
- [T1078 ] Valid Accounts – WageMole reuses stolen identities and credentials, especially for fake recruiter and GitHub accounts. Quote: ‘WageMole reuses stolen identities and credentials, especially for fake recruiter and GitHub accounts.’
- [T1027 ] Obfuscated Files or Information – Obfuscated malicious scripts are hidden in long comments or outside IDE view. Quote: ‘Obfuscated malicious scripts are hidden in long comments or outside IDE view.’
- [T1055 ] Process Injection – TsunamiKit uses injection techniques in its execution chain. Quote: ‘TsunamiKit uses injection techniques in its execution chain.’
- [T1036 ] Masquerading – Malware disguised as legitimate software (e.g., conferencing tools, NVIDIA installers). Quote: ‘Malware disguised as legitimate software (e.g., conferencing tools, NVIDIA installers).’
- [T1497 ] Virtualization/Sandbox Evasion – TsunamiKit includes environment checks and obfuscation to evade analysis. Quote: ‘TsunamiKit includes environment checks and obfuscation to evade analysis.’
- [T1056.001 ] Input Capture: Keylogging – InvisibleFerret includes clipboard and keylogging modules. Quote: ‘InvisibleFerret includes clipboard and keylogging modules.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – AkdoorTea, BeaverTail, and Tropidoor communicate with C&C servers over HTTP/S. Quote: ‘AkdoorTea, BeaverTail, and Tropidoor communicate with C&C servers over HTTP/S.’
- [T1105 ] Ingress Tool Transfer – BeaverTail downloads second-stage payloads like InvisibleFerret, TsunamiKit, or Tropidoor. Quote: ‘BeaverTail downloads second-stage payloads like InvisibleFerret, TsunamiKit, or Tropidoor.’
Indicators of Compromise
- [File Hash ] Samples and trojanized projects – E34A43ACEF5AF1E5197D940B94FC37BC4EFF0B2A (nvidiadrivers.zip containing WeaselStore), 90378EBD8DB757100A833EB8D00CCE13F6C68E64 (img_layer_generate.dll downloader of Tropidoor), and many more hashes.
- [Filename ] Malicious archive and executables – nvidiaRelease.zip (contains BeaverTail and AkdoorTea), drivUpdate.exe / drvUpdate.exe (AkdoorTea TCP RAT).
- [File ] Scripts and loaders – main.js (obfuscated BeaverTail script), ClickFix-1.bat (initial-stage BAT that downloads nvidiaRelease.zip), run.vbs (executes AkdoorTea and shell.bat).
- [Domain ] Remote storage and C2 hosting – driverservices[.]store (199.188.200[.]147) used for remote storage, www.royalsevres[.]com (116.125.126[.]38) as remote storage.
- [Onion ] Tor C2 ] TsunamiClient C&C – n34kr3z26f3jzp4ckmwuv5ipqyatumdxhgjgsmucc65jac56khdy5zqd[.]onion (TsunamiClient C&C server).
- [IP ] C2 infrastructure – 103.231.75[.]101 (AkdoorTea C&C), 45.159.248[.]110 (BeaverTail C&C), 45.8.146[.]93 and 86.104.72[.]247 (Tropidoor C&C servers).