Shai-Hulud is a self-propagating npm worm that steals secrets, hijacks GitHub accounts and repositories, and backdoors popular packages by injecting a large malicious bundle.js and postinstall commands to publish infected package versions. Over 500 packages were infected — including widely used libraries such as @ctrl/tinycolor and multiple @crowdstrike packages — resulting in exposed private repos, stolen credentials, and automated propagation across the dependency chain. #Shai-Hulud #ctrl/tinycolor #CrowdStrike
Keypoints
- The Shai-Hulud worm executes on npm package installation by running a >3MB bundle.js that contains modules for AWS, GCP, TruffleHog, and GitHub API interaction.
- It checks for npm and GitHub tokens, then creates and runs bash scripts to exfiltrate secrets, create shai-hulud branches, and upload workflows that collect repository secrets.
- The worm automates making private organization repositories public and mirrors their contents to attacker-controlled locations to steal source code.
- For self-replication, Shai-Hulud enumerates the victim’s most downloaded npm packages, injects bundle.js, adds a postinstall (or preinstall) node bundle.js command, bumps versions, and republishes the packages.
- Collected secrets and system data are aggregated and uploaded to a repository named “Shai-Hulud” in the victim’s account, typically as a data.json file after double Base64 encoding.
- Over 500 packages were identified as compromised, including high-impact libraries like @ctrl/tinycolor (2M weekly downloads) and several @crowdstrike packages.
- Detection and remediation recommendations include auditing GitHub for shai-hulud artifacts, rotating tokens and cloud keys, scanning systems, and using supply-chain monitoring and endpoint protection (Kaspersky detections: HEUR:Worm.Script.Shulud.gen).
MITRE Techniques
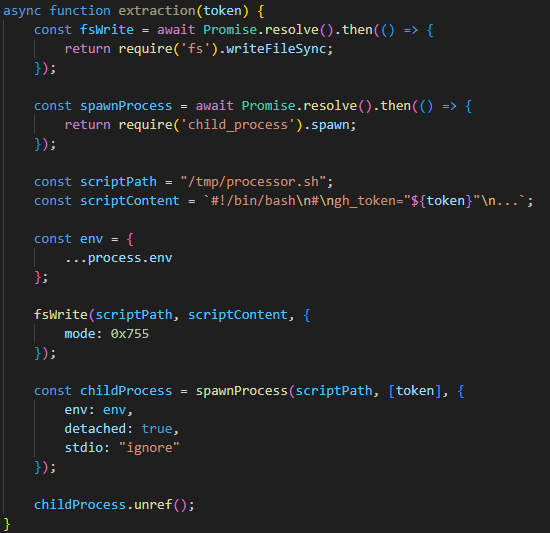
- [T1059] Command and Scripting Interpreter – The worm creates and runs temporary bash scripts (e.g., /tmp/processor.sh, /tmp/migrate-repos.sh) to interact with the GitHub API and perform repository operations: ‘creates a temporary executable bash script at /tmp/processor.sh and runs it as a separate process’.
- [T1537] Transfer Data to Cloud Account – Collected data is uploaded to a GitHub repository named “Shai-Hulud” as data.json: ‘creates a repository named “Shai-Hulud” in the victim’s profile. It then uploads the collected information to this repository as a data.json file.’
- [T1078] Valid Accounts – The malware uses stolen/npm and GitHub tokens to access repositories and publish packages: ‘collecting … npm token and authenticated GitHub user token in the environment’ and uses them to enumerate and modify packages.
- [T1119] Automated Collection – Uses TruffleHog and cloud modules to scan and harvest secrets from the local system and cloud environments: ‘uses modules for AWS and Google Cloud Platform (GCP) to scan for secrets’ and ‘uses TruffleHog to harvest secrets’.
- [T1609] Supply Chain Compromise – The worm modifies legitimate npm packages by injecting malicious bundle.js and postinstall commands, increments version, and republishes to npm: ‘The malicious bundle.js is added … A postinstall command is added … The package version number is incremented by 1’ to propagate.
- [T1490] Ingress Tool Transfer – Downloads utility releases (TruffleHog) from GitHub to the target system from official release URLs: ‘downloads the latest version of the utility from the original repository … https://github.com/trufflesecurity/trufflehog/releases/download/{utility version}/{OS-specific file}’.
- [T1036] Masquerading – The modified packages contain an atypical archive name (package.tar) and include legitimate open-source modules packaged with malicious code to blend in: ‘A distinctive characteristic … contain an archive named package.tar’ and bundle.js contains legitimate modules.
Indicators of Compromise
- [File] malicious filenames – bundle.js, shai-hulud-workflow.yml
- [String] artifact identifiers – “shai-hulud” (branch/workflow/repo names)
- [Hash] file hash – C96FBBE010DD4C5BFB801780856EC22878E701F42B76CCDE3F2678E548886860 (reported malicious file hash)
- [Network] webhook URL – https://webhook.site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7 (example of exfiltration endpoint)
- [Package] compromised npm packages – @ctrl/tinycolor (high-impact, ~2M weekly downloads), @crowdstrike/commitlint (8.1.1, 8.1.2) and many others (over 500 packages listed).
Read more: https://securelist.com/shai-hulud-worm-infects-500-npm-packages-in-a-supply-chain-attack/117547/