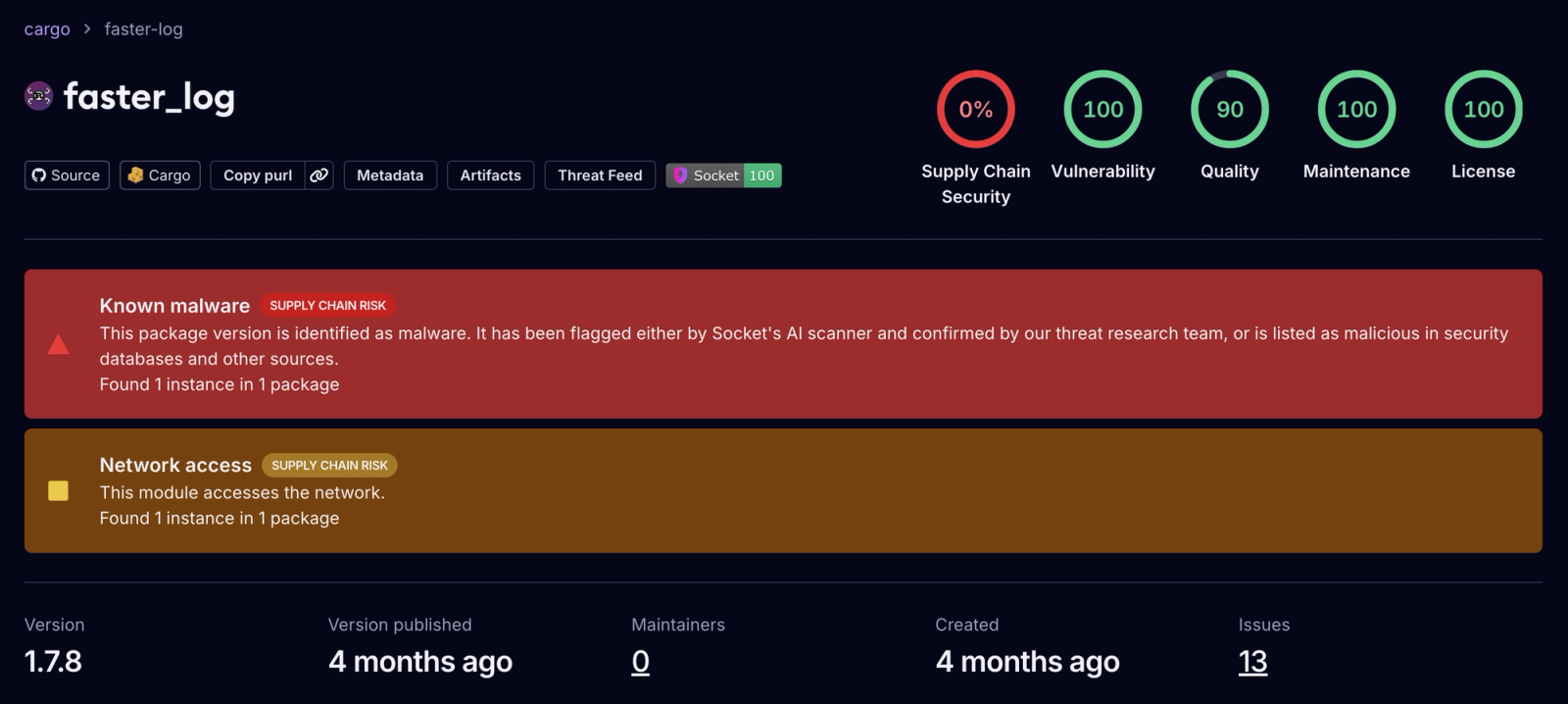
Two malicious Rust crates, faster_log and async_println, impersonated the legitimate fast_log logger and contained code that scanned Rust source files for Solana and Ethereum private keys, exfiltrating matches via HTTP POST to a hardcoded Cloudflare Workers C2 endpoint. The crates were published May 25, 2025, downloaded 8,424 times combined, and were removed and publisher accounts locked after Socket reported them to crates.io. #faster_log #async_println #fast_log #rustguruman #dumbnbased #mainnet.solana-rpc-pool.workers.dev
Keypoints
- Two malicious crates (faster_log and async_println) typosquatted the legitimate fast_log package, copying README and repository metadata to mislead developers.
- The crates contained functional logging code for cover and embedded routines that scanned Rust source files for Ethereum private keys (0x + 64 hex), Base58 tokens (Solana keys/addresses), and bracketed byte arrays, then exfiltrated matches via HTTPS POST to a hardcoded C2 endpoint.
- The hardcoded C2 endpoint (https://mainnet[.]solana-rpc-pool[.]workers[.]dev) is a Cloudflare Workers subdomain impersonating a blockchain RPC and was confirmed live during testing.
- Combined downloads for the two malicious crates were 8,424 (faster_log 7,181; async_println 1,243); they were published May 25, 2025 and had no downstream dependents.
- Socket reported the crates to crates.io; the Crates security team preserved files for analysis, removed listings, locked publisher accounts (rustguruman and dumbnbased), and published a security advisory within hours.
- The malicious code packaged each match with type, value, file path, and line number and sent batched JSON payloads using reqwest without authentication, enabling precise secret theft from developer machines or CI.
- Recommended mitigations include removing the crates, rotating any exposed secrets, adding file-level secret scanning, restricting egress from developer/CI networks, and creating detections for the observed patterns and POSTs to the C2.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – The crates impersonated a legitimate package and were published to crates.io to reach developer systems; quote: ‘This campaign shows how minimal code and simple deception can create a supply chain risk.’
- [T1036.005 ] Masquerading: Match Legitimate Resource Name or Location – The malicious packages typosquatted fast_log, copied README and repository links to mislead users; quote: ‘The crate typosquats the legitimate fast_log, reuses its README and repository link, and impersonates the project to mislead developers.’
- [T1552.004 ] Unsecured Credentials: Private Keys – The code searched for and collected private keys and key material (Ethereum private keys, Solana keys, byte arrays); quote: ‘Search for hex strings that might be keys/addresses’ and ‘Search for base58 strings (typical Solana addresses/keys)’.
- [T1005 ] Data from Local System – The crate recursively scanned project directories and .rs files to read source lines and extract secrets; quote: ‘Recurses into directories and processes every .rs file.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – Exfiltration of collected secrets was performed via HTTP POST over HTTPS to a hardcoded endpoint; quote: ‘All exfiltration goes here in a single POST.’
- [T1657 ] Financial Theft – The targeting of wallet private keys (Solana, Ethereum) enables theft of blockchain assets; quote: ‘The goal plainly: harvest secrets, especially Solana keys and Ethereum private keys.’
Indicators of Compromise
- [C2 Endpoint ] Exfiltration endpoint – https://mainnet[.]solana-rpc-pool[.]workers[.]dev (Cloudflare Workers subdomain used for POSTing harvested keys)
- [Crate names ] Malicious package names on crates.io – faster_log, async_println
- [Publisher accounts ] Malicious authors/publishers – rustguruman (https://github[.]com/rustguruman), dumbnbased (https://github[.]com/dumbnbased)
- [Patterns searched ] Payload-targeted file patterns – example patterns: “0x” + 64 hex (Ethereum private keys), quoted Base58 strings 32–44 chars (Solana keys), and bracketed byte arrays like [0x12, 0xAB, …]
- [Download counts ] Exposure metric – faster_log 7,181 downloads, async_println 1,243 downloads
Read more: https://socket.dev/blog/two-malicious-rust-crates-impersonate-popular-logger-to-steal-wallet-keys