Two malicious backdoors were found on a compromised WordPress site: a disguised plugin at ./wp-content/plugins/DebugMaster/DebugMaster.php that created a hidden admin, exfiltrated credentials to a C2, hid itself, and injected visitor scripts; and a root-level ./wp-user.php that ensured a hardcoded admin account named “help” was always present by recreating it if removed. These files provided layered persistence, data exfiltration, and visitor-script injection, enabling long-term attacker access and control. #DebugMaster #kickstar-xbloom
Keypoints
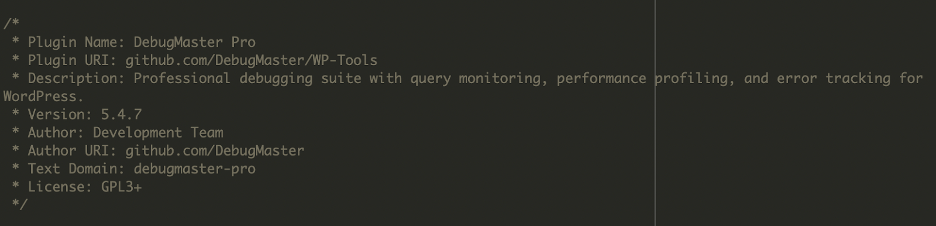
- Two malicious files were discovered: ./wp-content/plugins/DebugMaster/DebugMaster.php (a disguised plugin backdoor) and ./wp-user.php (a persistent admin-recreation script).
- DebugMaster created a secret administrator account (“help”), hid that account from plugin/user listings, and restored admin privileges if altered.
- DebugMaster exfiltrated generated admin credentials and site details to an attacker-controlled C2 endpoint (obfuscated as hxxps://kickstar-xbloom[.]info/collect[.]php).
- The malware injected external scripts into pages served to visitors (excluding admins or whitelisted IPs) and logged administrator IP addresses.
- wp-user.php enforced persistence by deleting and recreating the “help” admin with a known password whenever it ran, preventing removal by site owners.
- Indicators of compromise include the presence of the two files, unrecognized administrator accounts, and administrators being recreated after deletion.
- Recovery requires deleting the malicious files, auditing and removing the “help” account, resetting all credentials, updating software, and monitoring outbound connections.
MITRE Techniques
- [T1136 ] Create Account – The malware created a new administrator user named “help” and ensured it retained admin privileges. Quote: ‘This snippet forces WordPress to create a new user named help with the role of administrator. If the user already exists, the script ensures it has administrator privileges restored.’
- [T1218 ] Signed Binary Proxy Execution (plugin disguising) – The DebugMaster file masqueraded as a legitimate plugin to blend in with normal components. Quote: ‘This “DebugMaster Pro” plugin disguised itself as a legitimate developer tool, but its hidden functions created an administrator user with hardcoded credentials.’
- [T1071 ] Application Layer Protocol – The backdoor sent encoded JSON containing credentials and site info to a remote HTTP endpoint (C2). Quote: ‘It encodes the generated username, password, email, and the server’s IP into JSON, then Base64-encodes it… sends this information to a remote endpoint.’
- [T1573 ] Encrypted Channel (obfuscation/use of base64) – The endpoint URL and payloads were obfuscated with Base64 before transmission. Quote: ‘The endpoint URL is also obfuscated using base64 encoding which decodes to something like hxxps://kickstar-xbloom[.]info/collect[.]php.’
- [T1222 ] File and Directory Discovery (plugin hiding) – The plugin removed itself from plugin listings and filtered user queries to hide the malicious admin account. Quote: ‘To remain hidden, the plugin removed itself from plugin listings and filtered user queries to hide the newly created admin account.’
- [T1608 ] Stage Capabilities (injected scripts) – The malware injected external scripts into web pages for visitors and collected admin IPs for tracking. Quote: ‘The malware injects external code into your website… This code collects and logs the IP addresses of administrators.’
Indicators of Compromise
- [File path ] Malicious files discovered – ./wp-content/plugins/DebugMaster/DebugMaster.php, ./wp-user.php
- [Domain ] C2 / exfiltration endpoint – hxxps://kickstar-xbloom[.]info/collect[.]php (domain blocked on VirusTotal)
- [Account name ] Backdoor administrator – username “help” repeatedly created/recreated by the malware
- [Behavioral IOC ] Persistent admin recreation – unrecognized admin accounts reappearing after deletion (sign of wp-user.php behavior)
Read more: https://blog.sucuri.net/2025/09/hidden-wordpress-backdoors-creating-admin-accounts.html