Check Point Research attributes a long-running campaign to the Iran-nexus APT group Nimbus Manticore (also tracked as UNC1549 / Smoke Sandstorm) that uses tailored spear-phishing and fake recruiting portals to deliver Multi-stage DLL side-loading malware variants including MiniJunk (an evolution of Minibike) and the MiniBrowse stealer, targeting defense, telecommunications, and aviation in Western Europe and the Middle East. The actor employs undocumented low-level NT APIs, heavy compiler-level obfuscation, code signing, Cloudflare/Azure-backed C2 infrastructure, and domain naming conventions to increase stealth and resiliency. #NimbusManticore #MiniJunk
Keypoints
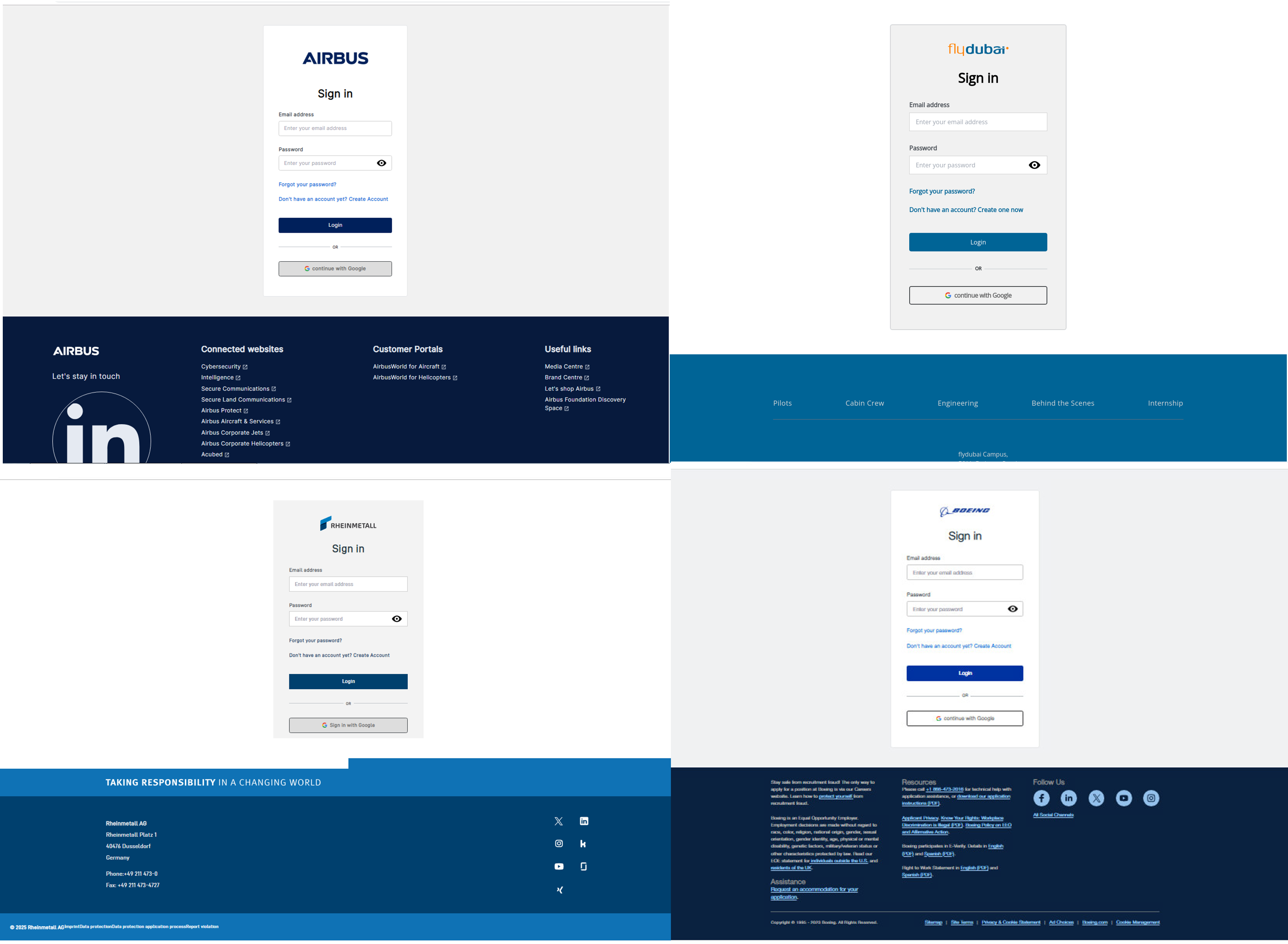
- Nimbus Manticore conducts highly targeted spear-phishing using fake career portals and pre-shared credentials to deliver malicious archives tailored per victim.
- The attacker leverages a novel multi-stage DLL side-loading technique by abusing undocumented NT API fields (DllPath) to force legitimate binaries to load malicious DLLs from archive folders.
- Core malware includes MiniJunk (evolved Minibike backdoor) and MiniBrowse (browser credential stealer), both featuring heavy obfuscation and modular C2 communication.
- Operator TTPs: use of valid code signing (SSL.com), large padded binaries, junk-code inflation, and Cloudflare + Azure App Service for resilient, rotating C2 infrastructure.
- MiniJunk supports typical backdoor functions (file read/write, process creation, DLL load, named pipes) with encoded network data and multiple hardcoded C2s for redundancy.
- A related but distinct cluster (dxgi.dll) shows similar targeting and commands but smaller payloads, simpler obfuscation, and WinHTTP-based communications, suggesting shared codebase access.
- Geographic focus has expanded to Western Europe (Denmark, Sweden, Portugal) while continuing traditional Middle East targets (Israel, UAE) within aerospace, defense, telecom, and aviation sectors.
MITRE Techniques
- [T1566] Phishing – Spear-phishing with fake recruiting portals and pre-shared credentials directing victims to unique login URLs (“the attacker uses tailored spear‑phishing from alleged HR recruters directing victims to fake career portals”).
- [T1204] User Execution – Victim runs Setup.exe from a malicious ZIP archive disguised as hiring software, initiating the infection chain (“the victim runs Setup.exe from the archive”).
- [T1218] Signed Binary Proxy Execution – Abuse of legitimate Windows Defender binary SenseSampleUploader.exe to sideload malicious DLLs (“userenv.dll uses low-level ntdll API calls to execute … SenseSampleUploader.exe … exploited to sideload the xmllite.dll”).
- [T1574] Hijack Execution Flow (DLL Search Order Hijacking) – Multi-stage DLL side-loading by manipulating process DLL search path and exploiting relative DLL loading (“the malware abuses … DllPath parameter … when the dll is not found next to SenseSampleUploader.exe, it will be loaded from the archive directory”).
- [T1547] Boot or Logon Autostart Execution – Persistence via copying binaries to %AppData%LocalMicrosoftMigAutoPlay and creating a scheduled task / autorun registry key (“creates a working folder … copies … MigAutoPlay.exe … and then adds an auto-run registry key”).
- [T1105] Ingress Tool Transfer – Delivery of malicious archives and DLLs via lure websites and downloadable ZIP files from fake career portals (“After entering credentials … the user downloads a malicious archive with the malware”).
- [T1071] Application Layer Protocol – C2 communication over HTTPS/HTTP using Windows APIs and encoded payloads (“The backdoor uses regular HTTPS requests using the Windows API” and “MiniBrowse sends data in JSON payload”).
- [T1027] Obfuscated Files or Information – Heavy compiler-level obfuscation, junk code, opaque predicates, and per-string encryption to evade analysis (“heavy compiler‑level code obfuscation … junk code insertion, control‑flow obfuscation, opaque predicates, obfuscated function calls, and encrypted strings”).
- [T1112] Modify Registry – Creation of autorun registry keys as part of persistence (“it … adds an auto-run registry key to execute the benign executable”).
- [T1497] Virtualization/Sandbox Evasion (size/padding evasion) – Inflating binary sizes and using signing to reduce detection and evade sandbox/static detection limits (“Large malware files … padding pushes discriminative byte patterns past those limits” and “started to use the service SSL.com to sign their code”).
Indicators of Compromise
- [File Hash] Malicious archives – examples: 23c0b4f1733284934c071df2bf953a1a894bb77c… (malicious zip), 0b2c137ef9087cb4635e110f8e12bb0ed43b6d6e… (malicious zip), and several more hashes.
- [File Hash] MiniBrowse samples – examples: ffeacef025ef32ad092eea4761e4eec3c96d4ac46… (Minibrowse large blob), 9b186530f291f0e6ebc981399c956e1de3ba26b0… (Minibrowse).
- [Domain] Azure / Cloud lure and C2 domains – examples: services-update-check.azurewebsites[.]net, send-feedback-413.azurewebsites[.]net; and other azurewebsites[.]net app service domains used as C2s and lures.
- [Domain] Fake recruiting / lure domains – examples: telespazio-careers[.]com, boeing-careers[.]com; plus many career-themed domains like arabiccountriestalent[.]com and check-backup-service-288.azurewebsites[.]net.
- [File Name] Sideloaded DLLs / binaries – examples: userenv.dll (malicious backdoor DLL), xmllite.dll (loader DLL), MigAutoPlay.exe (persisted benign executable used to launch backdoor).
Read more: https://research.checkpoint.com/2025/nimbus-manticore-deploys-new-malware-targeting-europe/