An Indonesian and Vietnamese Android-targeted banking trojan campaign disguises malicious apps as legitimate payment and government identity tools. The operators rely on spoofed Google Play pages, WebSocket-based APK delivery, and shared infrastructure to evade detection and operate during Eastern Asia’s daytime hours. #BankBotRemo #BankBot #M-Pajak #IdentitasKependudukanDigital #IndonesianVietnameseAndroid
Keypoints
- Targeted Android users in Indonesia and Vietnam are being targeted with banking trojans disguised as legitimate apps.
- Attackers reuse TLS certificates and group domains to resolve to the same IP addresses, indicating a shared infrastructure footprint.
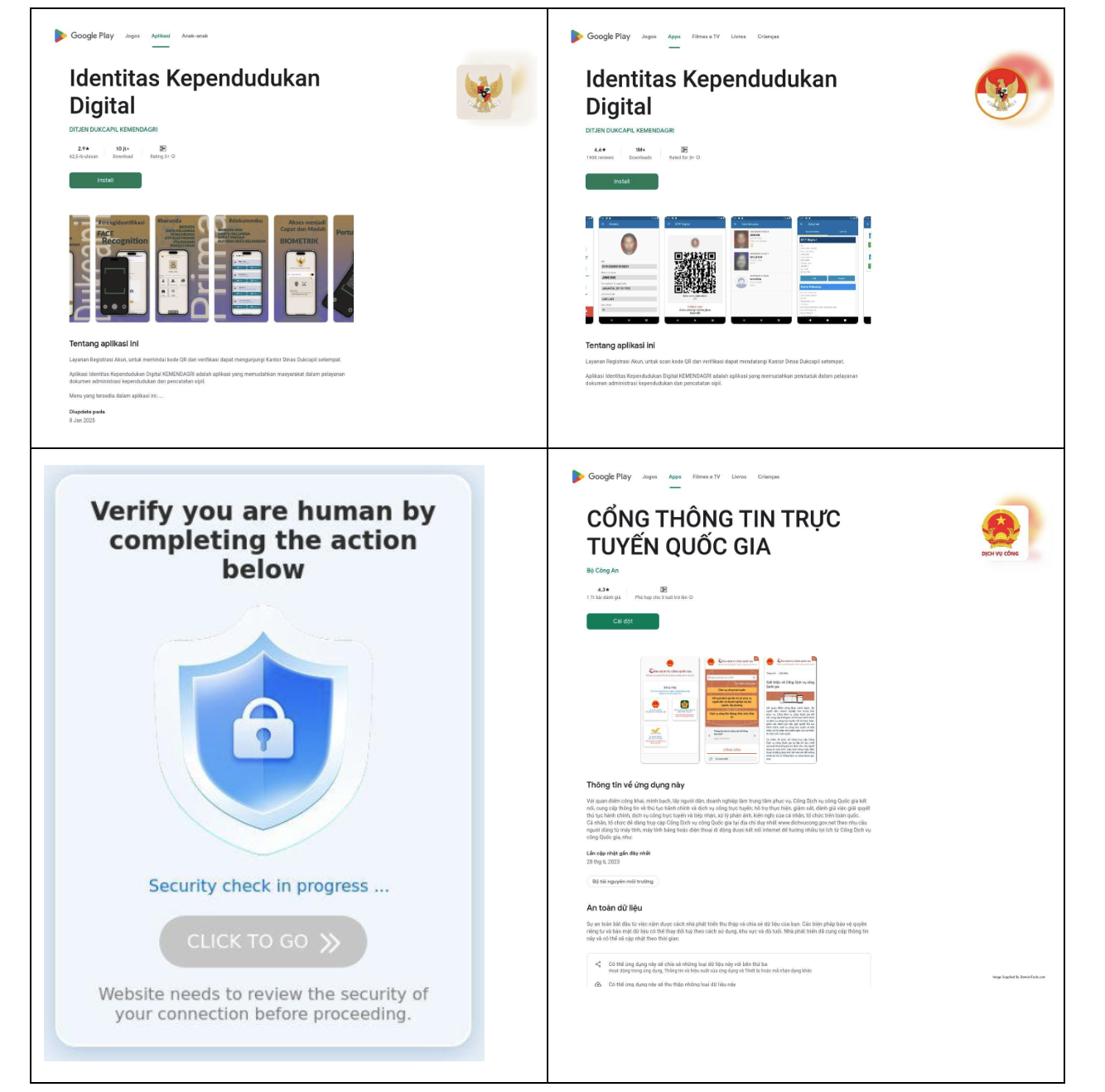
- Phishing-like spoofing of Google Play/App Store pages is used to encourage infections and downloads.
- Malware delivery leverages WebSocket-based transfers to deliver APKs and to obfuscate traffic.
- Some browsers flag suspicious downloads, but the operation relies on infrastructure patterns such as Alibaba ISP and shared DNS to remain resilient.
MITRE Techniques
- [T1036] Masquerading – The malicious campaign spoofs legitimate app stores to lure installs (‘The page contains fake buttons for Google Play Store and App Store application downloads.’).
- [T1071.001] Web Protocols – Uses WebSocket-based delivery and C2 to transfer the APK (‘This initiates a WebSocket connection: socket.emit(‘startDownload’, …). The server responds by sending the .apk file back to the browser in many small chunks.’).
- [T1027] Obfuscated/Compressed Files and Information – Obfuscation wrapper used to hide file transfers (‘The site uses an obfuscation wrapper with Socket.IO library, which enables real-time, bidirectional communication with a server.’).
- [T1204] User Execution – User clicks on spoofed store page initiating the download (‘Clicking the Google Play starts an on-page download progression bar and then prompts for a file store download location on device.’).
- [T1105] Ingress Tool Transfer – Payload delivered to the user as APK chunks during transfer (‘The server responds by sending the .apk file back to the browser in many small chunks.’).
Indicators of Compromise
- [Domain] Malicious distribution and C2 domains – asdrjswer678.com, twmlwcs.cc, indiemusicacademi.com
- [SHA256] Hashes of payloads – 0b7f4c3be1d0b0f0b53495ff33e8c4b22adf122e01f8c72d705c489a975fe498a9358048b5f6e8e7c4b47bebd41991f9e33ccea6e9eb88d1c33dc6079ceb06b6d4937d30853932bc0bf840bac79121e027ec7078395ec2c50d6392f1fed528f11f9253092c5a2abdb7bc3d93fccad85f23ce5bfde38377c792a242f045afcdb54be32b6417ee32b9da0b81e487f9e26503bd7086d95a4fb5fd8dd8ac1f328e5ddb0c223bc08108694e8185e0d8bcd32684e56ba251fb63a544c7eff2932580799e38cc89cf22ff8f5a566c2069702dd89f55bc3f8a3caf96f0d9327256bdc791e29c4a157ac2e1a233f9a59e63cb203fd8eac0595c452d93ed9b72e264dbc8f92386baafae215fee4c27b955dd6786a7d70d32e5d6eff54cfd8a1353d3d1b473ec5b55d4829d043ed3998cc90f633fab5d37bcf5476c6b274eeba85b9f5baaa7e9d3f6211d4ebbe0c5c564b234903fbf5a0dd3f531b518e13ef0dcc8bedc4a6d0de69fad50b9e0800ba0120fe2b2f7ebb414e1ae335149a77dae3544b0a4613968fb18d67bb2314ff70a0f
https://dti.domaintools.com/banker-trojan-targeting-indonesian-and-vietnamese-android-users