Black Lotus Labs uncovered SystemBC’s infrastructure: a botnet of over 80 C2s averaging 1,500 daily victims—mostly compromised VPS systems—used as high-volume proxies by multiple criminal services including REM Proxy. Lumen blocked related traffic and released IoCs to help defenders disrupt the operation. #SystemBC #REMProxy
Keypoints
- SystemBC operates a botnet of more than 80 C2 servers with ~1,500 daily bots, ~80% of which are compromised VPS systems from major commercial providers.
- Victimized VPSs are used as high-bandwidth proxies for numerous criminal services, enabling large-scale brute force, web scraping, spam, and ransomware support.
- REM Proxy consumes roughly 80% of the SystemBC network and sells tiered proxy packages (Mix-Speed, Mix-Mix, Mix-Economy) including Mikrotik-based and open proxies.
- SystemBC infections show many unpatched vulnerabilities per host (average ~20 CVEs; some with 160+), facilitating long infection lifetimes (≈40% persist >1 month).
- Lumen identified specific infrastructure (e.g., 104.250.164[.]214 and AS hosting ~80 C2s), blocked traffic across its global backbone, and published IoCs to aid defenders.
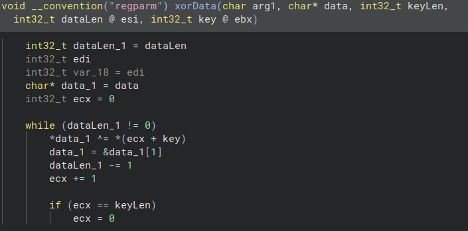
- SystemBC’s malware primarily provides proxy functionality; samples include a Linux variant with XOR + RC4 + XOR config/encryption and a 40-byte hardcoded key.
- Multiple criminal services and threat groups (Russian parsing services, VN5Socks, REM Proxy, TransferLoader/Morpheus ties) utilize SystemBC proxies despite high detection and blacklisting rates.
MITRE Techniques
- [T1071 ] Application Layer Protocol – SystemBC proxies traffic through high-numbered user entry ports to forward user connections to victims (“Users of the proxy network reach out to SystemBC C2s on high numbered ports, which then sends the user through to one of the victims.”)
- [T1105 ] Ingress Tool Transfer – C2 delivers shell script that forces download of many SystemBC samples (“…the new bot will call back on port 80 to download a shell script (with Russian comments) that forces the download over 180 samples of the SystemBC malware.”)
- [T1620 ] Reflective Code Loading (encryption/obfuscation technique) – Malware config and beacon are XOR/RC4/XOR encoded to hide configuration and communications (“The config is XOR encoded using a hardcoded 40-byte key… beacon is encrypted by first XORing the beacon with the key, RC4 encrypting with said key, and then XORing once again.”)
- [T1499 ] Endpoint Denial of Service (proxy abuse for high-volume traffic) – Compromised VPSs are used to generate very high proxy traffic volumes (example: “one 24-hour window we observed a particular IP address generate an excess of 16 gigabytes of proxy data”).
- [T1190 ] Exploit Public-Facing Application – Victim VPSs exhibited numerous unpatched CVEs exploited for initial access or recruitment (“each victim shows 20 unpatched CVEs and at least one critical CVE… one address shown as having over 160 unpatched vulnerabilities”).
- [T1588 ] Obtain Capabilities – Commoditization and sale of SystemBC bots to multiple services and forums, enabling other threat actors (“SystemBC is commoditized in underground forums and frequently used by a variety of criminal threat groups… REM Proxy is marketed in a dedicated criminal forum”).
Indicators of Compromise
- [IP Address ] recruitment and sample hosting – 104.250.164[.]214 (source of attacks to recruit victims and host malware samples)
- [IP Address ] REM Proxy C2 observed in netflow – 185.25.48[.]97 (observed as a REM Proxy C2 in Lumen netflow)
- [File Hash ] Linux SystemBC sample – 1c74b1195250632f2f1d1a9066f07f6e0a8c12dff40aeb3c1fe22440c97bc8ee (sample analyzed exhibiting XOR+RC4+XOR config encryption)
- [Domain ] REM Proxy screening/collection – honipsiops[.]in (used to identify new accessible IP addresses; ~3,000 IPs contact it daily)
- [Ports ] network context – example ports used: 443 (initial access attempts), 80 (callback/download), 51922 (Mikrotik SSH), 1080 and 8989 (open proxy ports)