Trend Micro observed a surge in phishing campaigns that host fake CAPTCHA pages on AI-native platforms (Vercel, Netlify, Lovable) to trick users and evade automated scanners. These CAPTCHA gates delay suspicion and hide credential-harvesting redirects, enabling large-scale phishing using free, credible hosting domains. #Vercel #Netlify #Lovable
Keypoints
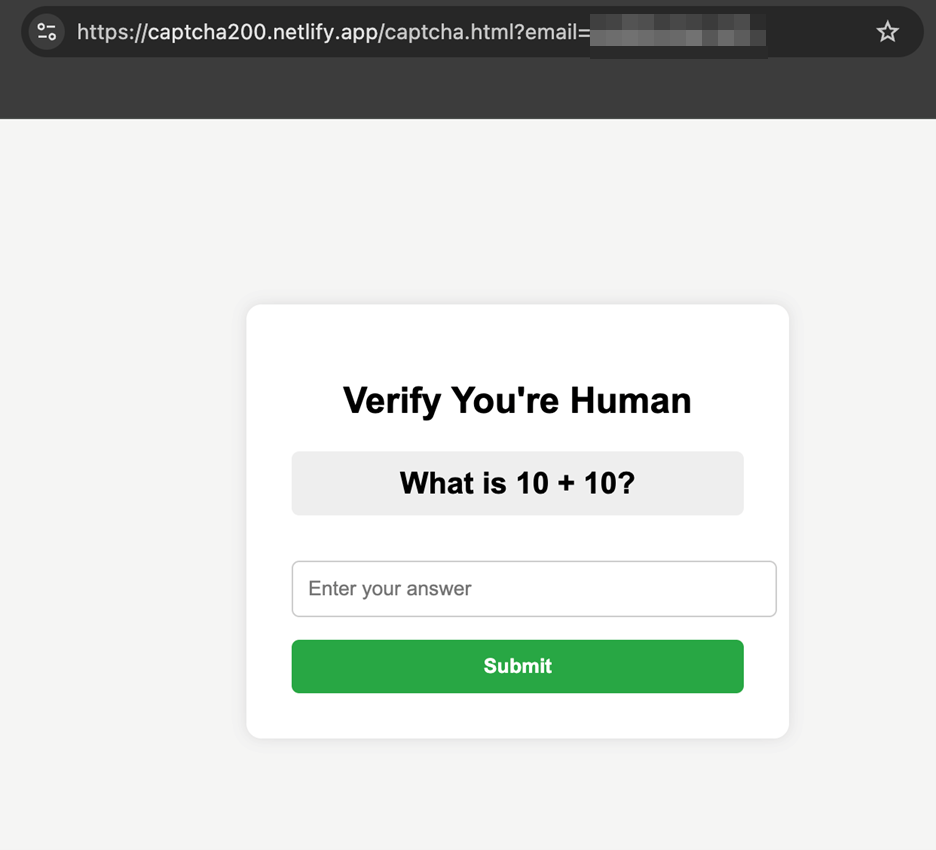
- Since January, attackers have deployed fake CAPTCHA challenge pages on AI-native hosting platforms to initiate phishing campaigns.
- Fake CAPTCHA pages lower victim suspicion and cause automated scanners to miss the underlying credential-harvesting redirect.
- Threat actors exploit ease of deployment, free hosting tiers, and credible platform branding (*.vercel.app, *.netlify.app, *.lovable.app) to scale attacks.
- Trend Micro observed distribution across platforms: Vercel.app (52 sites), Lovable.app (43 sites), Netlify.app (3 sites).
- Campaigns commonly begin with spam emails containing urgent themes (e.g., “Password Reset Required”, “USPS Change of Address Notification”) that link to CAPTCHA pages.
- Defensive recommendations include user training on CAPTCHA-based phishing, monitoring trusted hosting domains, following redirect chains, and deploying email and behavior-based protections.
- Activity increased sharply from February to April, dipped, and saw a renewed spike in August, indicating persistent abuse over months.
MITRE Techniques
- [T1566] Phishing – Attackers send spam emails with urgent messages like “Password Reset Required” or “USPS Change of Address Notification” to lure victims to fake CAPTCHA pages (“…Clicking the embedded URL directs the target to what appears to be a harmless captcha verification page…”).
- [T1192] Spearphishing Link – The campaigns use embedded URLs in emails that lead victims to platform-hosted CAPTCHA pages which then redirect to credential-harvesting forms (“…Clicking the embedded URL directs the target to what appears to be a harmless captcha verification page…”).
- [T1608] Abuse of Legitimate Services – Threat actors host fake CAPTCHA and phishing pages on legitimate AI-native platforms (Vercel, Netlify, Lovable) taking advantage of free hosting and trusted domains (“…Domains ending in *.vercel.app or *.netlify.app inherit credibility from the platform’s reputation…”).
- [T1036] Masquerading – The CAPTCHA challenge is used to appear as a benign verification step, reducing user suspicion (“…By presenting a captcha challenge first, victims are less likely to recognize the page as malicious, lowering their guard.”).
- [T1204] User Execution – The attack relies on users interacting with the CAPTCHA (solving it) to trigger the redirect to the phishing page where credentials are harvested (“…Once the captcha is completed, the victim is redirected to the actual phishing page…”).
Indicators of Compromise
- [Domain ] Hosted fake CAPTCHA/phishing pages – captcha200[.]netlify.app, adobepdfonlinereadercaptcharobot[.]netlify.app
- [Domain ] Vercel-hosted phishing pages – basvursana2025hemen[.]vercel.app, web-orpin-xi[.]vercel.app
- [Domain ] Lovable-hosted CAPTCHA/phishing pages – captcha-link-gateway[.]lovable.app, captcha-math-linker[.]lovable.app
- [Domain ] Additional example pages used in campaigns – captcha-office-redirect[.]lovable.app, get-new-pass[.]lovable.app