The article reveals a critical Entra ID vulnerability driven by undocumented impersonation tokens called Actor tokens, enabling cross-tenant access and full control of any tenant via the legacy Azure AD Graph API. Microsoft fixed the flaw within days and rolled out mitigations, but the token design created logging gaps and potential undetected abuse across Microsoft 365 and Azure services. #EntraID #AzureADGraph #MicrosoftGraph #B2BTrust #MSRC
Keypoints
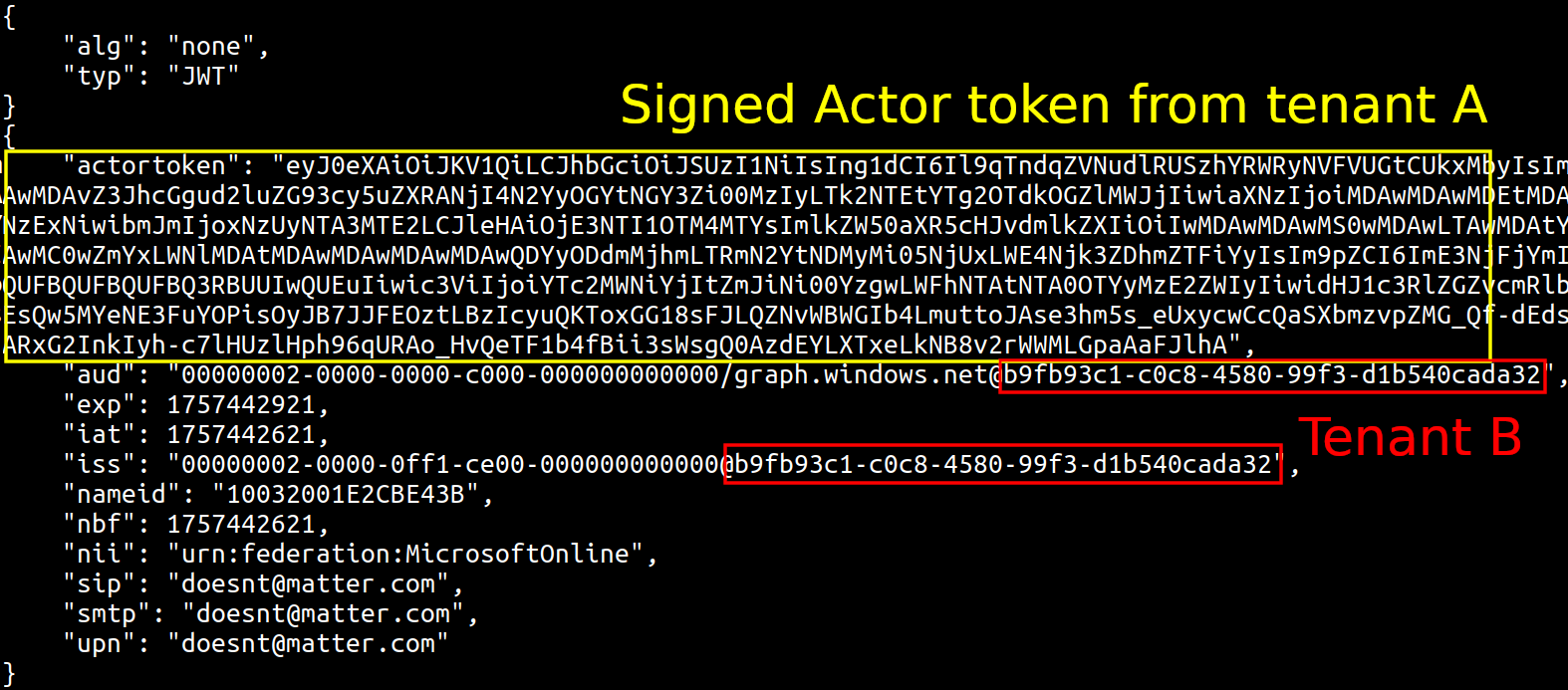
- Actor tokens enable impersonation across Entra ID tenants without Conditional Access policies.
- These tokens can be used to impersonate any user, including Global Admins, in any tenant.
- Cross-tenant access can be leveraged via the legacy Azure AD Graph API and B2B guest trusts.
- Brute-forcing netId could enable rapid targeting of tenants with little to no logs.
- Microsoft issued CVE-2025-55241 and rolled out mitigations to block Actor tokens for Graph API and improve logging.
https://dirkjanm.io/obtaining-global-admin-in-every-entra-id-tenant-with-actor-tokens