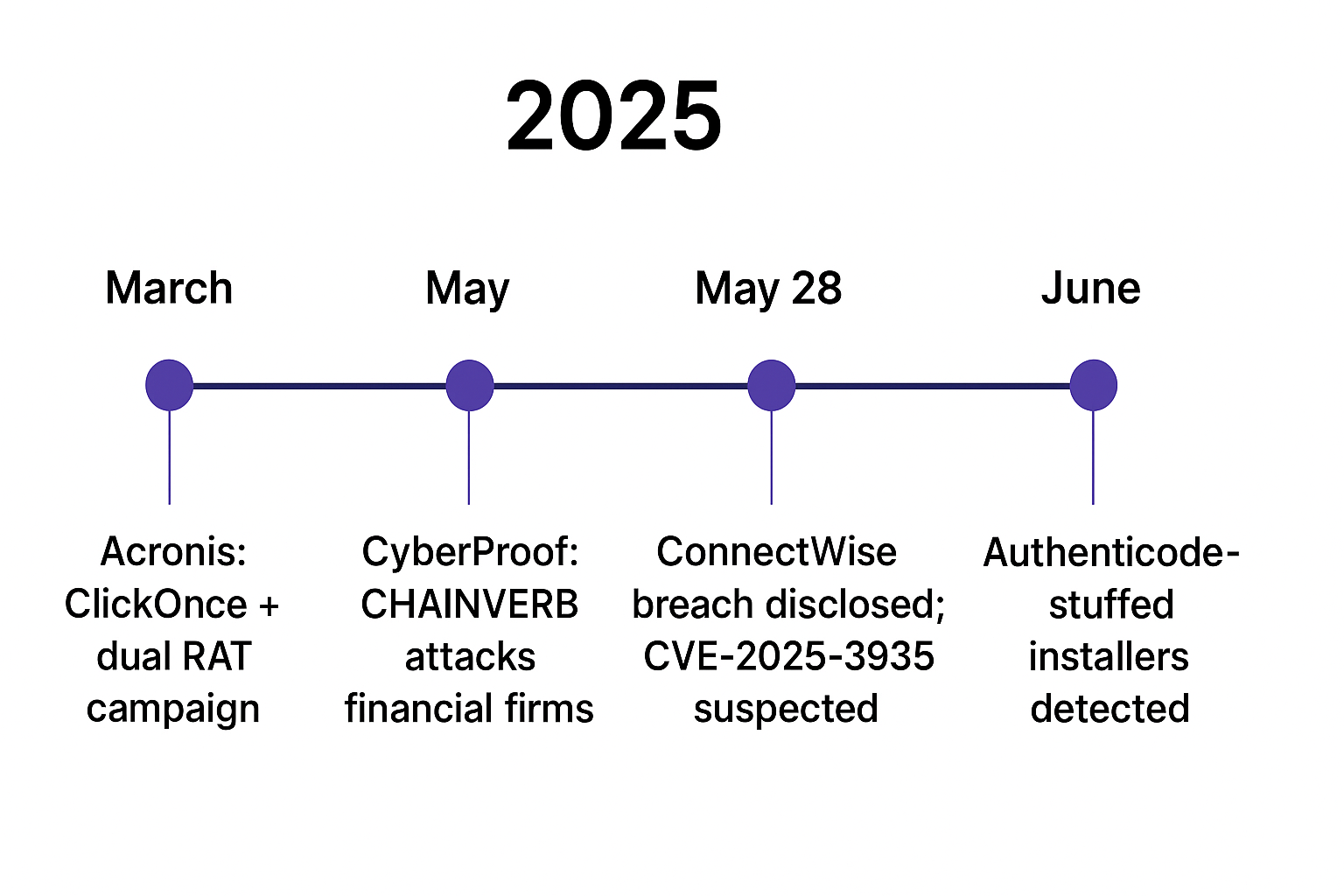
Attackers abused ConnectWise ScreenConnect installers and open directories to stage and deliver AsyncRAT and a custom PowerShell RAT using dual execution paths, repacked installers, and aggressive scheduled tasks for persistence. Infrastructure included multiple open-directory hosts, /Bin/ ClickOnce redirect chains, and high-ephemeral port C2s enabling resilient, evasive AsyncRAT operations. #AsyncRAT #ScreenConnect
Keypoints
- Threat actors trojanized ScreenConnect installers and staged payloads in open directories to deliver AsyncRAT and a custom PowerShell RAT.
- Investigations identified at least eight infrastructure hosts (e.g., 176.65.139[.]119, 45.74.16[.]71, 164.68.120[.]30) hosting multi-stage toolkits and payload containers.
- Attack chains used dual execution paths: in-memory .NET Assembly.Load on AV-guarded hosts and native injection via libPK.dll::Execute on others.
- Persistence achieved via aggressively scheduled tasks (SystemInstallTask every 2–10 minutes, 3losh every 2 minutes) and weaponized LNK/VBS/JS/PS1 loaders.
- Phishing redirect chains used ClickOnce-like droppers with a recurring /Bin/ pattern (e.g., dual.saltuta.com/Bin/event_support-pdf.Client.exe) across campaigns in 2024–2025.
- Operators rotated ports (standard 21/80/443 and high ephemeral 30,000–60,000) and repacked installers/certificates to evade signature-based detection.
- Payload containers (logs.ldk/logs.idk/logs.idr) and several hashes were not found on VirusTotal at capture, signaling fresh or repackaged artifacts.
MITRE Techniques
- [T1547] Boot or Logon Autostart Execution – Scheduled tasks “SystemInstallTask” and “3losh” created to maintain persistence (“…schedules Ab.vbs as a recurring task named SystemInstallTask…” / “creates a scheduled task named ‘3losh’ … trigger every two minutes”).
- [T1218] Signed Binary Proxy Execution – Trojanized/signed ScreenConnect installers used as an execution vector (“…trojanized ConnectWise ScreenConnect installers … repacked or re-signed the ScreenConnect installer to evade static detection”).
- [T1059.001] PowerShell – PowerShell loaders (Skype.ps1) reconstructed payloads and invoked native exports (“…Skype.ps1 … reconstructs or decodes an embedded payload blob, loads and invokes a native export named Execute from C:UsersPubliclibPK.dll”).
- [T1105] Ingress Tool Transfer – Open directories and /Bin/ URLs hosted staged payloads and ClickOnce droppers (“…open directories as staging points” / “dual.saltuta.com/Bin/event_support-pdf.Client.exe”).
- [T1027] Obfuscated Files or Information – Encoded blobs (1.txt, pe.txt, logs.*) and comma-separated numeric assemblies used to hide payloads (“…pe.txt … obfuscated assembly encoded as comma-separated numbers” / “reconstructs and loads 1.txt, another encoded blob”).
- [T1055] Process Injection – Native injection into AppLaunch.exe via libPK.dll::Execute for unprotected hosts (“…decoded payload … injected into AppLaunch.exe using a native DLL called libPK.dll … provides an exported function named Execute”).
- [T1204.002] User Execution: Malicious Link – HTML redirectors (police.html → galusa.ac.mz → dual.saltuta.com) used to trick users into executing ClickOnce droppers (“…police.html acts as a malicious redirector … forwards victims … to galusa.ac.mz/pdf … lands on dual.saltuta.com … delivers event_support-pdf.Client.exe”).
- [T1112] Modify Registry – (Implied) Weaponized LNK and scheduled task creation to achieve persistence via standard Windows mechanisms (“…weaponized Microsoft.lnk … invoke PowerShell with execution policy bypass … scheduling tasks”).
Indicators of Compromise
- [IP ] Open directory hosts serving staged payloads – 176.65.139[.]119, 45.74.16[.]71 (and 6 more hosts such as 164.68.120[.]30, 78.161.14[.]229, 78.162.57[.]179, 88.229.27[.]40, 185.208.159[.]71, 94.154.173[.]145)
- [Domain ] ClickOnce /Bin/ payload hosts and redirectors – dual[.]saltuta[.]com, verify[.]uniupdate[.]net (and 6 other /Bin/ URLs such as baquskreen.top/Bin/… and con.wolonman.com/Bin/…)
- [File name ] Loaders and staged artifacts observed – Skype.ps1, Ab.vbs/Ab.js, libPK.dll (examples: Skype.ps1, libPK.dll)
- [File hash ] Notable file hashes and ClickOnce dropper – event_support-pdf.Client.exe MD5: c596910b65fb3af81b9ca67ce11ebcc3; ScreenConnect trojanized binary hash 701e702f… (and multiple logs.* container hashes not found on VirusTotal)
- [Scheduled Task ] Persistence task names and intervals – SystemInstallTask (every 10m), 3losh (every 2m)
- [Filename pattern ] Payload container names and sizes – logs.ldk (60 KB–3 MB), logs.idr/logs.idk (multiple similar sizes) – repeated across directories
Read more: https://hunt.io/blog/asyncrat-screenconnect-open-directory-campaigns