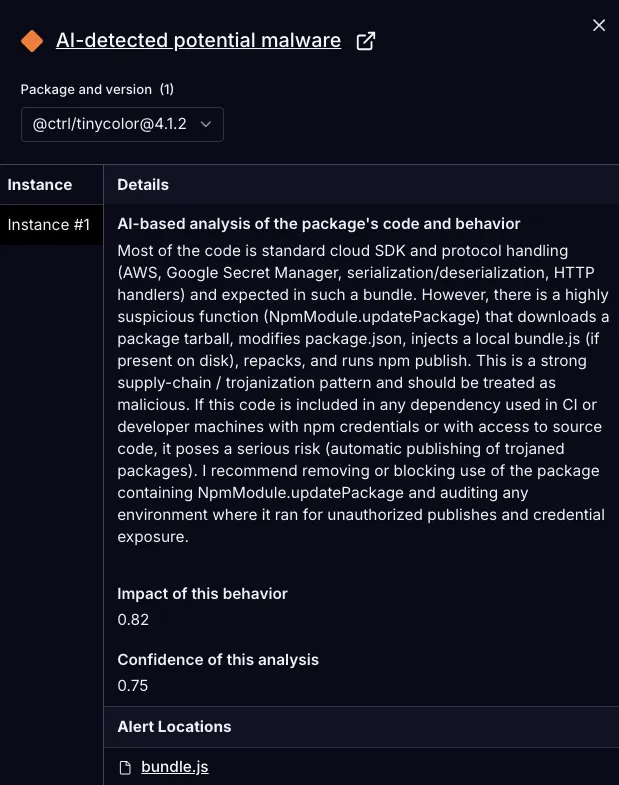
A malicious update to @ctrl/tinycolor and over 40 other npm packages injected a trojanized installer that modifies package archives to include a bundled script (bundle.js) which runs on install to scan for secrets, validate tokens, create GitHub Actions workflows, and exfiltrate findings to a hardcoded webhook. The campaign uses an automated repack-and-publish routine (NpmModule.updatePackage) to propagate across downstream packages and has been flagged by researchers and automated detection systems. #TruffleHog #@ctrl/tinycolor
Keypoints
- More than 40 npm packages across multiple maintainers were trojanized in a supply-chain campaign that repackages and republishes compromised packages.
- Compromised packages include a function (NpmModule.updatePackage) that downloads a tarball, modifies package.json, injects bundle.js, repacks, and republishes to npm.
- The injected bundle.js executes automatically on install, downloads a platform-matching TruffleHog binary, and scans the filesystem and repos for high-entropy strings and credential patterns.
- Collected secrets are validated (e.g., npm whoami) and, when possible, used to create GitHub Actions workflows in repositories to persist and exfiltrate data during CI runs.
- Exfiltration is performed to a hardcoded webhook endpoint (hxxps://webhook[.]site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7), and the script probes cloud metadata endpoints to capture short-lived credentials.
- bundle.js SHA-256 is 46faab8ab153fae6e80e7cca38eab363075bb524edd79e42269217a083628f09; immediate actions include uninstalling or pinning, auditing environments, and rotating exposed tokens.
- tinycolor (2.2M weekly downloads) is a highly visible affected package but was not the original source; analysis and distribution investigation are ongoing.
MITRE Techniques
- [T1609] Container and Resource Discovery – The malware profiles the platform and accesses cloud metadata endpoints to discover credentials (“http://169[.]254[.]169[.]254”, “http://metadata[.]google[.]internal”) used for credential theft.
- [T1059] Command and Scripting Interpreter – bundle.js executes downloaded scanner binaries and shell snippets (de-minified shows execSync usage and a bash block writing workflows) to run TruffleHog and persist workflows (“…execSync(cmd…)… FILE_NAME=’.github/workflows/shai-hulud-workflow.yml’”).
- [T1078] Valid Accounts – The script searches for and validates developer CI tokens and npm tokens (fetch to “https://registry.npmjs.org/-/whoami” and “https://api.github.com/user”) to leverage existing credentials for further actions (“Authorization: `Bearer ${process.env.NPM_TOKEN}`”).
- [T1537] Transfer Data to Cloud Account – Collected findings are exfiltrated to a hardcoded webhook endpoint (“hxxps://webhook[.]site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7”).
- [T1195] Supply Chain Compromise – The attack injects malicious bundle.js into package tarballs and republishes them via an automated NpmModule.updatePackage function, trojanizing downstream packages (“downloads a package tarball, modifies package.json, injects a local script (bundle.js), repacks the archive, and republishes it”).
- [T1098] Account Manipulation (CI/CD Pipeline) – The malware writes a GitHub Actions workflow into repositories to persist access and trigger exfiltration during CI runs (“writes a GitHub Actions workflow into .github/workflows” and the workflow contains a run step that posts findings to the webhook).
Indicators of Compromise
- [File Hash] malicious bundle.js – SHA-256: 46faab8ab153fae6e80e7cca38eab363075bb524edd79e42269217a083628f09
- [Domain/Endpoint] exfiltration webhook – hxxps://webhook[.]site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7
- [File Path / Filename] persisted CI workflow – .github/workflows/shai-hulud-workflow.yml (workflow created by the malware to exfiltrate findings)
- [Package Name] trojanized npm package – @ctrl/tinycolor (compromised release), plus 40+ additional npm packages affected (tinycolor highlighted due to 2.2M weekly downloads)
- [Network Targets] cloud metadata endpoints probed – http://169[.]254[.]169[.]254 (AWS IMDSv4), http://[fd00:ec2::254] (IMDSv6), http://metadata[.]google[.]internal (GCP metadata)
Read more: https://socket.dev/blog/tinycolor-supply-chain-attack-affects-40-packages