Validin introduced Dashboard Feeds (Threat Indicator Feed and Project Updates Feed) to surface newly reported IOCs and team activity directly on the homepage, improving analyst workflows and situational awareness. They also added daily PTR (reverse DNS) scanning across IPv4 to capture short-lived reverse DNS entries, illustrated by detection of rotating PTR records for 91.247.36[.]102, including free.friendhosting[.]net. #91.247.36.102 #free.friendhosting.net
Keypoints
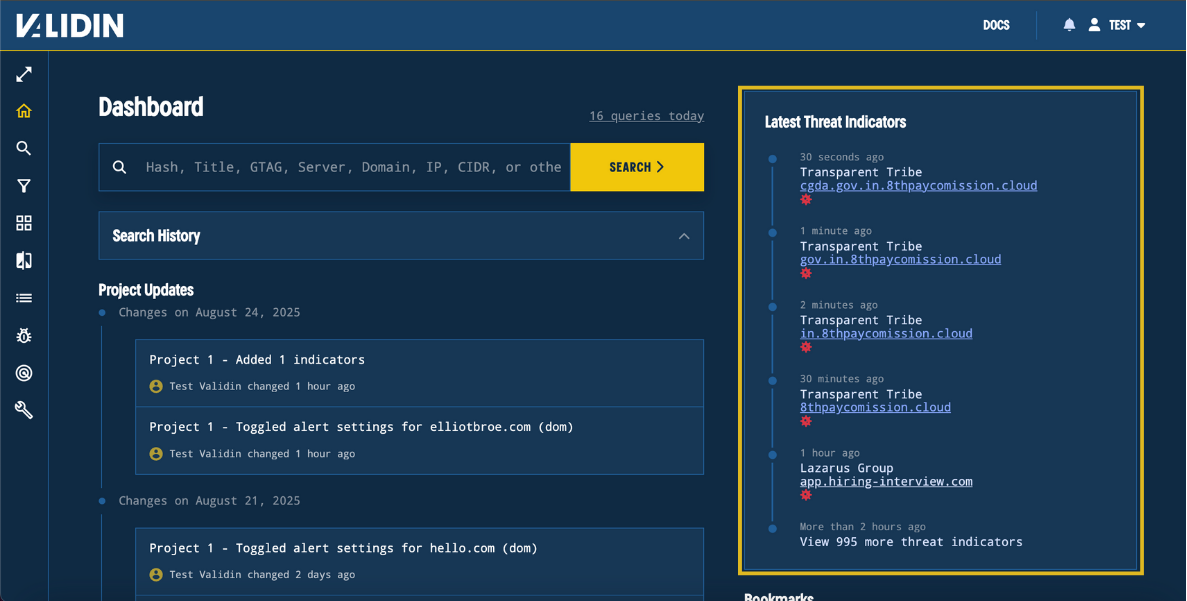
- Validin launched Dashboard Feeds that show newly reported threat indicators and project activity on the homepage to speed analyst triage.
- The Threat Indicator Feed surfaces the most recent IOCs tied to threat groups and links to indicator and group profiles for investigation.
- The Project Updates Feed consolidates project changes, showing which project changed, what changed, who changed it, and when.
- Validin added daily PTR (reverse DNS) scanning across the IPv4 space to complement existing A, AAAA, and NS record scans.
- Daily PTR scanning captures short-lived or fast-changing reverse DNS entries, improving visibility into hosting, infrastructure clusters, and naming conventions.
- An example highlights IP 91.247.36[.]102 rotating PTR records including occasional free.friendhosting[.]net entries, which were detected after daily scanning began.
- These updates aim to enhance threat-hunter workflows and enable more complete DNS-based discovery and pivoting inside the platform.
MITRE Techniques
- [T1566 ] Phishing – PTR records are used as a trust check by email servers to confirm message origin (“this kind of lookup is often used as a trust check, for example, email servers will use PTR records to confirm that a message is really coming from the domain it claims”).
- [T1588 ] Obtain Capabilities – Use of DNS infrastructure and PTR records to reveal hosting providers or infrastructure clusters (“PTR records can reveal hosting providers, infrastructure clusters, or even adversary naming conventions”).
- [T1592 ] Gather Victim Identity Information – Reverse DNS lookups used to map IPs to domain names for attribution and discovery (“it takes an IP address and shows which domain name it belongs to”).
- [T1614 ] Credentials from Password Stores – (Implied investigative technique) Using increased scanning frequency to capture short-lived indicators that expose OPSEC mistakes (“capture more short-lived or fast-changing reverse DNS entries… provide new opportunities to catch OPSEC mistakes”).
Indicators of Compromise
- [IPv4 ] example of rotating PTR behavior – 91.247.36[.]102 (observed cycling PTR records and brief setting to free.friendhosting[.]net)
- [Domain / PTR ] reverse DNS example – free.friendhosting[.]net (observed as a brief PTR for 91.247.36[.]102)
- [Record types ] scanned DNS records – A, AAAA, NS (previously scanned) and PTR (newly added daily scanning)
Read more: https://www.validin.com/blog/dashboard_feeds_daily_ptr/