ESET Research discovered HybridPetya, a Petya/NotPetya copycat uploaded to VirusTotal in February 2025 that can install a UEFI bootkit to encrypt NTFS Master File Tables and, in one variant, weaponize CVE‑2024‑7344 (via a cloak.dat file) to bypass UEFI Secure Boot on vulnerable systems. ESET telemetry shows no active in-the-wild spread and the samples lack NotPetya’s aggressive network propagation. #HybridPetya #CVE-2024-7344
Keypoints
- HybridPetya samples resembling Petya/NotPetya were uploaded to VirusTotal in February 2025 and include multiple installer filenames such as notpetyanew.exe.
- The malware’s UEFI bootkit targets NTFS partitions and encrypts the Master File Table (MFT) to render files inaccessible at boot.
- One variant exploits CVE‑2024‑7344 using a specially crafted cloak.dat file to bypass UEFI Secure Boot and load an unsigned EFI application from the EFI System Partition.
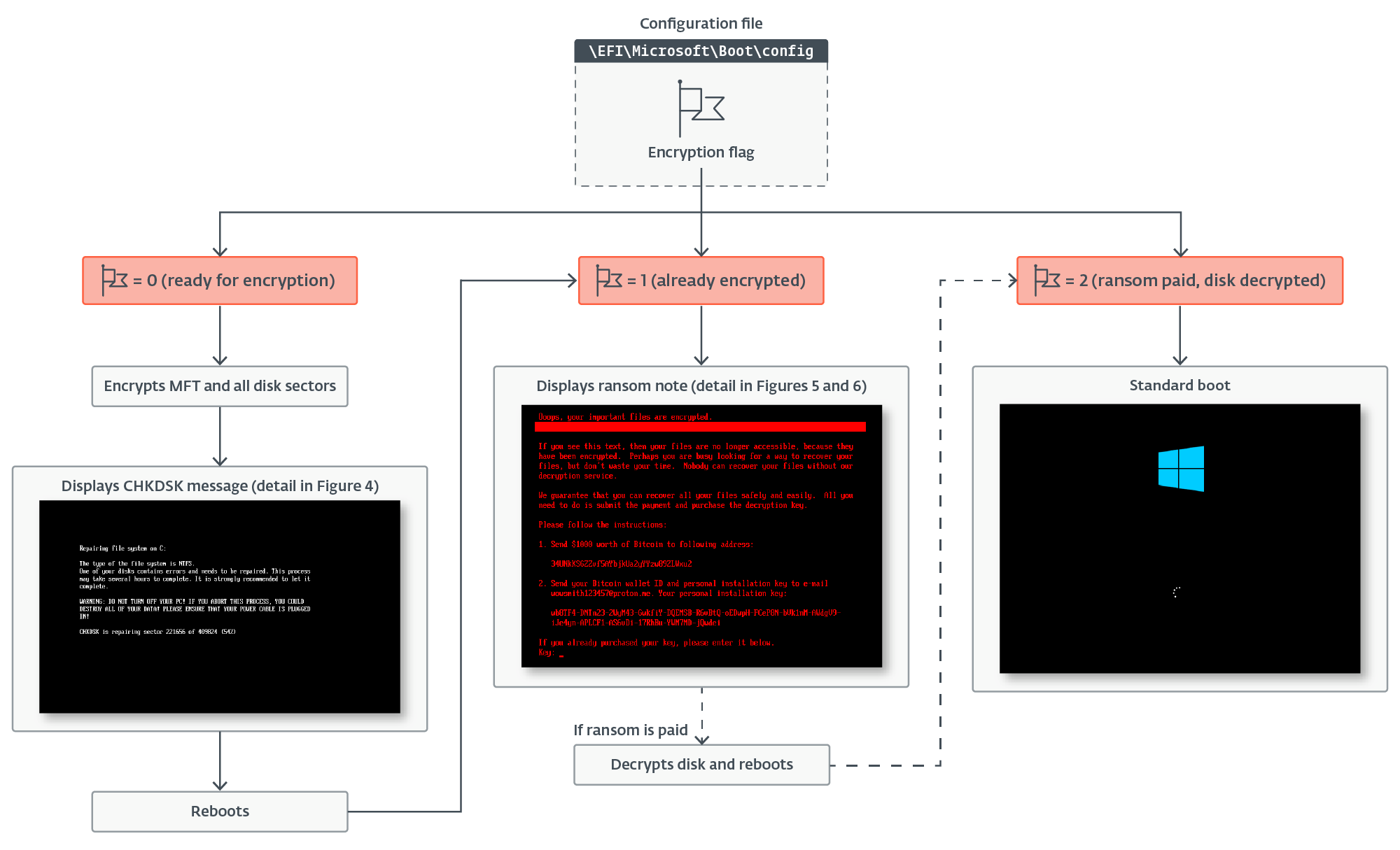
- Installers drop bootkit-related files to the EFI System Partition, back up legitimate bootloaders, set encryption flags and keys in EFIMicrosoftBootconfig, then trigger a BSOD to activate the bootkit on reboot.
- HybridPetya’s key-generation algorithm allows reconstruction of decryption keys from victims’ personal installation keys, making it able to function as recoverable ransomware (unlike destructive NotPetya).
- ESET found no telemetry indicating active use or aggressive network propagation; the authors may be a researcher or unknown actor and the samples could be proof-of-concept.
- A VirusTotal archive shows a bootkit variant bundled in cloak.dat and reloader.efi (vulnerable to CVE‑2024‑7344), with files like bootmgfw.efi and counter reflecting an already-encrypted system.
MITRE Techniques
- [T1587.001 ] Develop Capabilities: Malware – HybridPetya is a newly observed ransomware with UEFI compatibility and a UEFI bootkit component developed by unknown authors. Quote: ‘HybridPetya is new ransomware with UEFI compatibility and a UEFI bootkit component developed by unknown authors.’
- [T1587.004 ] Develop Capabilities: Exploits – The authors developed or repurposed an exploit for CVE‑2024‑7344 to enable Secure Boot bypass. Quote: ‘HybridPetya’s authors developed an exploit for the CVE‑2024‑7344 UEFI Secure Boot bypass vulnerability.’
- [T1203 ] Exploitation for Client Execution – HybridPetya exploits CVE‑2024‑7344 to execute an unsigned UEFI bootkit on systems with UEFI Secure Boot enabled. Quote: ‘HybridPetya exploits CVE‑2024‑7344 to execute an unsigned UEFI bootkit on outdated systems with UEFI Secure Boot enabled.’
- [T1106 ] Native API – Installers call NtRaiseHardError to crash the system and trigger bootkit execution on reboot. Quote: ‘HybridPetya installers use undocumented native API NtRaiseHardError to cause a system crash after the bootkit’s installation.’
- [T1542.003 ] Pre-OS Boot: Bootkit – Persistence is achieved via a bootkit component installed to the EFI System Partition supporting legacy and UEFI systems. Quote: ‘HybridPetya persists using the bootkit component. It supports both legacy and UEFI systems.’
- [T1574 ] Hijack Execution Flow – Installers replace or hijack the legitimate Windows bootloader to ensure the malicious bootkit runs at boot. Quote: ‘HybridPetya installers hijack the regular system boot process by replacing the legitimate Windows bootloader with a malicious one.’
- [T1068 ] Exploitation for Privilege Escalation – Exploitation of CVE‑2024‑7344 allows execution of the UEFI bootkit with high privileges during boot. Quote: ‘HybridPetya exploits CVE‑2024‑7344 to bypass UEFI Secure Boot and execute the malicious UEFI bootkit with high privileges during bootup.’
- [T1211 ] Exploitation for Defense Evasion – The CVE‑2024‑7344 exploit is used to bypass UEFI Secure Boot checks and load unsigned code. Quote: ‘HybridPetya exploits CVE‑2024‑7344 to bypass UEFI Secure Boot.’
- [T1620 ] Reflective Code Loading – Installers use reflective DLL loading techniques for payload execution. Quote: ‘HybridPetya installers use the reflective DLL loading technique.’
- [T1036 ] Masquerading – The bootkit displays a fake CHKDSK message during MFT encryption to mask malicious activity. Quote: ‘The HybridPetya bootkit displays fake CHKDSK messages on the screen during disk encryption to mask its malicious activity.’
- [T1486 ] Data Encrypted for Impact – The installer encrypts files by extension while the bootkit encrypts the NTFS MFT to impact data availability. Quote: ‘The HybridPetya installer encrypts files with specified extensions and the bootkit component encrypts MFT file on each NTFS-formatted partition.’
- [T1529 ] System Shutdown/Reboot – The malware reboots the device after MFT encryption to complete its bootkit-based impact. Quote: ‘HybridPetya reboots the device after MFT encryption.’
Indicators of Compromise
- [File Hash ] HybridPetya UEFI bootkit and components – BD35908D5A5E9F7E41A61B7AB598AB9A88DB723D (bootmgfw.efi UEFI bootkit), 9DF922D00171AA3C31B75446D700EE567F8D787B (extracted UEFI component).
- [File Hash ] Installers and payloads – 9B0EE05FFFDA0B16CF9DAAC587CB92BB06D3981B (Win32/Injector.AJBK), CDC8CB3D211589202B49A48618B0D90C4D8F86FD (core.dll, Win32/Filecoder.OSK).
- [Filename ] EFI System Partition files – EFIMicrosoftBootconfig (encryption config and flags), EFIMicrosoftBootverify (verification array), EFIMicrosoftBootcounter (encrypted cluster counter).
- [File Hash / Filename ] cloak.dat and related vulnerable files – D0BD283133A80B47137562F2AAAB740FA15E6441 (cloak.dat containing XORed bootkit), 98C3E659A903E74D2EE398464D3A5109E92BD9A9 (bootmgfw.efi reloader vulnerable to CVE‑2024‑7344).
- [Filename / Sample names ] VirusTotal submit names – notpetyanew.exe, notpetya_new.exe, improved_notpetyanew.exe (installer filenames observed on VirusTotal).