Attackers are using HijackLoader—distributed via CAPTCHA-based phishing pages, fake installers, malvertising and pirated sites—to deliver multi-stage obfuscated PowerShell loaders that unpack and inject a packed .NET PE which downloads info-stealers such as NekoStealer, DeerStealer, and Lumma. Observed techniques include process doppelgänging, unhooking system DLLs, direct syscalls under WOW64, call-stack spoofing and extensive anti-VM checks. #HijackLoader #NekoStealer
Keypoints
- HijackLoader emerged in late 2023 and is commonly offered as Malware-as-a-Service, used primarily in financially motivated campaigns.
- Initial access frequently leverages CAPTCHA-based phishing (Clickfix), SEO-poisoned sites, malvertising, fake installers and pirated portals to deliver malicious .msi or HTA files.
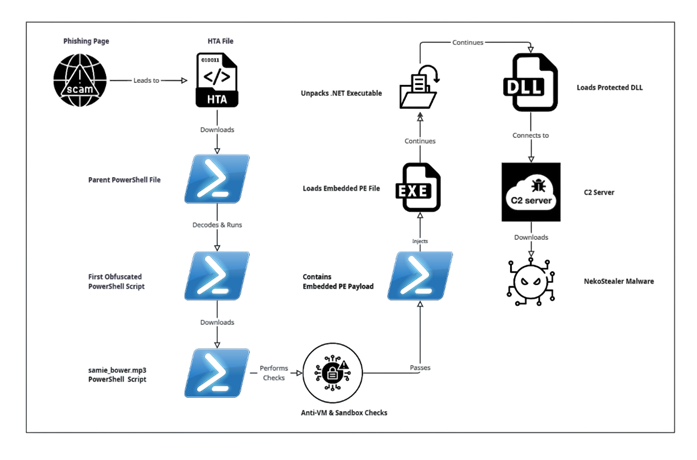
- Infection uses a multi-stage PowerShell chain: an HTA drops a downloader which runs heavily obfuscated PowerShell, downloads an MP3-named script (samie_bower.mp3) that contains the main loader, and ultimately decodes an embedded PE.
- Loaders employ strong obfuscation and anti-analysis measures (complex string reconstruction, Base64/XOR decoding, anti-VM checks inspecting VirtualBox identifiers, registry tampering) to evade detection and sandboxes.
- The final stage unpacks a packed .NET executable in-memory, loads a protected DLL, performs PE injection and attempts C2 communication to fetch info-stealers like NekoStealer, DeerStealer and Lumma.
- Notable evasion/tradecraft features include process doppelgänging with transacted sections, unhooking system DLLs, direct syscalls under WOW64, call-stack spoofing and anti-VM checks.
- Mitigation requires monitoring for initial access and intermediate stages (obfuscated scripts, suspicious HTA/PowerShell activity, unusual web downloads) rather than focusing solely on final payload detection.
MITRE Techniques
- [T1566.002] Phishing: Spearphishing Link – CAPTCHA phishing page used for social engineering (“CAPTCHA-Based Phishing Page for Social Engineering”).
- [T1189] Drive-by Compromise – Distribution via malvertising, SEO poisoning, fake installers and pirated portals (“distributed through fake installers, SEO-poisoned websites, malvertising, and pirated software/movie portals”).
- [T1059.001] Command and Scripting Interpreter: PowerShell – Multiple stages are PowerShell scripts including samie_bower.mp3 and staged PowerShell loaders (“This HTA file serves as the initial downloader, leading to the execution of a PowerShell file”).
- [T1027] Obfuscated Files or Information – Heavy multi-stage obfuscation and dynamic string reconstruction hinder static analysis (“heavily obfuscated, presenting a significant challenge to static analysis and signature-based detection”).
- [T1140] Deobfuscate/Decode Files or Information – Use of Base64 and XOR decoding to reveal embedded payloads (“performs Base64 decoding, XOR operations, and additional decryption routines”).
- [T1562.001] Impair Defenses: Disable or Modify Tools – Unhooking system DLLs to evade defensive instrumentation (“Unhooking system DLLs”).
- [T1070.004] Indicator Removal: File Deletion – Staged loaders likely perform file deletion as part of cleanup (“Indicator Removal: File Deletion (likely used in staged loaders)”).
- [T1211] Exploitation for Defense Evasion – Direct syscalls under WOW64 used to bypass user-mode hooks (“direct syscalls under WOW64”).
- [T1036] Masquerading – Use of misleading file extensions like .mp3 to hide PowerShell scripts (“fake extensions like .mp3 for PowerShell scripts”).
- [T1082] System Information Discovery – VM checks and registry queries to profile host environment (“inspecting the number of running processes and making changes to the registry keys”).
- [T1497.001] Virtualization/Sandbox Evasion: System Checks – Anti-VM checks targeting VirtualBox identifiers (“specifically target and read VirtualBox identifiers to determine if the script is running in a virtualized environment”).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys – Registry tampering to establish persistence (“Boot or Logon Autostart Execution: Registry Run Keys (registry tampering)”).
- [T1055] Process Injection – Loader performs PE injection routines to inject final payload into processes (“Intermediate PowerShell Script for PE Injection” and “PE injection routines”).
- [T1071.001] Application Layer Protocol: Web Protocols – C2 communication and payload download over HTTP/HTTPS (“attempts to connect to a URL to download a subsequent file” and C2 connection attempts to rs.mezi[.]bet).
- [T1105] Ingress Tool Transfer – Downloading additional payloads from remote servers (e.g., samie_bower.mp3 and subsequent payloads) (“downloading additional payloads”).
- [T1056 / T1005] Input Capture / Data from Local System – Final payload acts as an info-stealer collecting local system data (“info-stealer functionality of final payload” and references to NekoStealer, DeerStealer, Lumma).
Indicators of Compromise
- [File Hash] Embedded and payload hashes – examples: 1b272eb601bd48d296995d73f2cdda54ae5f9fa534efc5a6f1dab3e879014b57, 37fc6016eea22ac5692694835dda5e590dc68412ac3a1523ba2792428053fbf4 (and several other hashes listed).
- [URL/Domain] Malicious download hosts – example: hxxps[:]//rs[.]mezi[.]bet/samie_bower.mp3, hxxps[:]//1h[.]vuregyy1[.]ru/3g2bzgrevl[.]hta.
- [IP Address] Infrastructure endpoints – example: 91[.]212[.]166[.]51, 37[.]27[.]165[.]65:1477 (observed C2/hosting activity).
- [Domain] Related domains – example: cosi[.]com[.]ar (listed as associated domain).
- [URL/IP path] Additional host/path indicators – example: hxxp[:]//77[.]91[.]101[.]66/ and other referenced endpoints used during download attempts.