A newly discovered Android trojan named RatOn combines NFC relay attack capabilities (via NFSkate), remote access features, overlay-based ransom/deception pages, and automated money transfer (ATS) functionality targeting a Czech bank and several cryptocurrency wallets. The campaign used adult-themed domains to deliver a multi-stage dropper that abuses Accessibility and Device Admin privileges to automate transfers, extract wallet recovery phrases, and perform device locking; #RatOn #NFSkate
Keypoints
- RatOn is a previously unreported Android banking trojan discovered in a campaign linked to NFSkate-related activity, first seen between 5 July 2025 and 29 August 2025.
- The malware is multi-stage: a dropper installs a second-stage payload that requests Accessibility and Device Admin privileges, then may deploy a third-stage NFSkate payload for NFC relay attacks.
- Attackers used adult-themed domains (e.g., TikTok18+ names) targeting Czech and Slovak-speaking users to host the malicious dropper APKs.
- RatOn supports HTML/WebView overlays (URL-based or inline HTML) to display ransom notes or bait victims into opening apps and revealing PINs or phrases.
- Automated money transfer (ATS) functionality targets a Czech bank application (George Česko), auto-navigating UI elements and injecting PINs to confirm transactions.
- Cryptocurrency wallet targeting includes MetaMask, Trust Wallet, Blockchain.com, and Phantom; RatOn can auto-unlock wallets and extract recovery phrases via Accessibility and keylogging.
- The trojan exposes an extensive JSON-commandable bot interface covering screen casting, overlays, simulated input, SMS sending, ringtone changes, app launching, NFSkate control, and money transfer operations.
MITRE Techniques
- [T1204] User Execution – Malicious dropper hosted on adult-themed domains trick victims into installing a third-party installer via a WebView and an install button (“…the web page can call the installApk function if the victim presses corresponding button…”).
- [T1476] Install Root Certificate (similar capability via Accessibility abuse to alter system settings) – The dropper requests permission to install apps from unknown sources and the payload requests System Settings management to change ringtone and other settings (“…will request the permission from the victim to install applications from third party sources…”).
- [T1547] Boot or Logon Autostart Execution – The trojan registers Accessibility service and Device Admin privileges to persist and operate in the background (“…ask for two main permissions…Accessibility service access and Device Admin privilege…starting from this moment, the trojan will start working in background…”).
- [T1110] Brute Force (credential access via intercepted PINs and forcing unlock) – The malware forces victims to re-enter unlock credentials by expiring passwords and disabling biometric fallback to capture PINs (“…Set current device unlock pin/pattern/password to expired…victim will have to immediately change it. So, it would be intercepted by attacker.”).
- [T1056] Input Capture – Keylogging and Accessibility-driven input capture to record wallet PINs and recovery phrases (“…The keylogger component will record revealed data and will send it to control server.”).
- [T1190] Exploit Public-Facing Application (abuse of WebView/HTML overlays) – Overlays hosted via WebView are used to present HTML/JS templates (ransom notes or bait pages) to deceive victims (“…Both types of overlays will be created by using WebView either by providing the URL or by providing corresponding HTML code.”).
- [T1021] Remote Services (remote control) – RatOn provides remote access capabilities including screen casting, sending screen state, and executing remote commands via JSON objects (“…screen_live Start sending current screen state… Each command comes as JSON object…”).
- [T1606] Forge Web Credentials (UI Automation to perform fraudulent transfers) – Automated money transfers are performed by programmatically interacting with bank app UI elements, auto-typing PINs and clicking buttons (“…the trojan will launch bank application and initiate payment by auto clicking on application interface elements…it will automatically type in the digital PIN code to confirm the transaction.”).
- [T1429] Service Stop (disable keyguard and lock device) – The malware can lock the device using Device Admin and disable biometric keyguard forcing PIN entry (“…Lock the device using Device administrator access…Force victim to unlock the device using PIN/Pattern or password instead of using biometrical authentication.”).
Indicators of Compromise
- [Domain ] Control server / dropper hosting – marvelcore.top, evillab.world (also www-core.top, tiktok18.world)
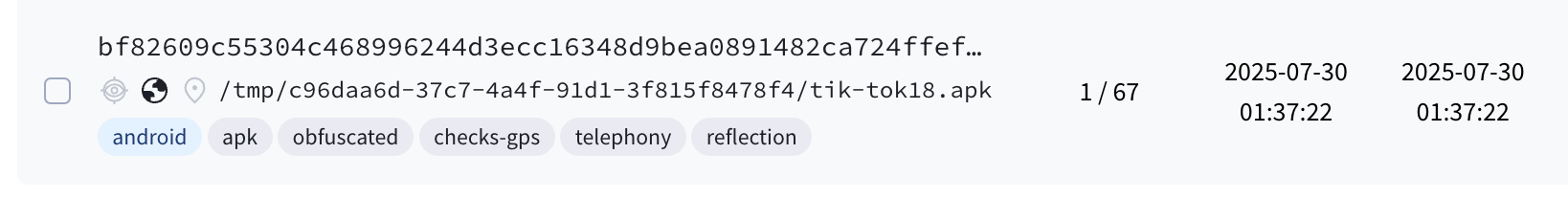
- [SHA256 ] Malware payload hashes – bf82609c55304c468996244d3ecc16348d9bea0891482ca724ffefcfaded8b66, bba15ecc8404698530761a122d3f03310b5e775f2e1552b645135fefd27e625c (and 17 more hashes)
- [App package names ] Targeted cryptocurrency wallets – io.metamask (MetaMask), com.wallet.crypto.trustapp (Trust), piuk.blockchain.android (Blockchain.com)
- [UI strings ] Banking app UI texts used for automation – Czech texts like “Nová platba” (New payment), “Domácí číslo účtu” (Domestic account number) used to locate elements during ATS
Read more: https://www.threatfabric.com/blogs/the-rise-of-raton-from-nfc-heists-to-remote-control-and-ats