Admin By Request (ABR) provides temporary, audited local administrator access to enforce least privilege, and integrating it with Wazuh centralizes privilege elevation events for faster detection and response. This integration uses Wazuh custom rules to detect denied elevations, repeated requests, and changes to local admin membership, improving visibility into risky privilege activity. #AdminByRequest #Wazuh
Keypoints
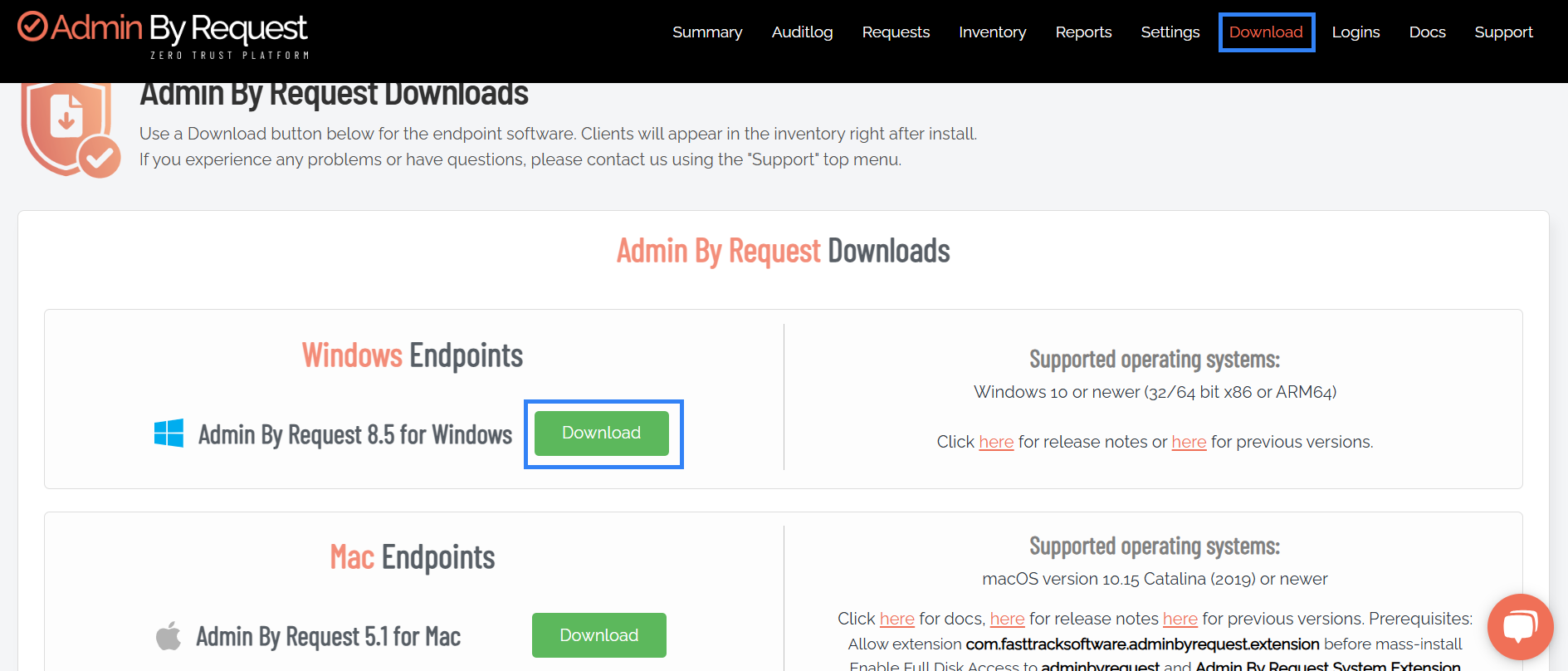
- Admin By Request eliminates permanent local administrator rights by enabling temporary, audited elevation requests to enforce least privilege.
- Integrating ABR with Wazuh centralizes privilege elevation logs from Windows Application event channel for correlation and alerting.
- Wazuh custom rules (IDs 100111–100116) detect denied elevations, multiple requests, approvals, and local admin group membership changes.
- Rules include both single-event detections and frequency-based detections (e.g., 5 events in 300 seconds) to flag suspicious activity.
- Test scenarios demonstrate detection for denied requests, repeated requests, granted admin sessions, and session end removals.
- Visualization in the Wazuh dashboard uses Threat Hunting filters by rule.id to view alerts corresponding to ABR events.
- Restarting the Wazuh manager is required after adding custom rule files to apply detection rules.
MITRE Techniques
- [T1548 ] Abuse Elevation Control Mechanism – Used to detect privilege elevation attempts and denials via ABR logs (“…denied…”)
- [T1548.002 ] Exploitation of Elevated Execution – Used to detect received elevation approval replies and multiple elevation requests (“…Received elevation approval reply…”)
- [T1136.001 ] Add Account to Local Group – Used to detect when ABR adds a user to the local administrators group (“… added to local administrators group”)
- [T1098 ] Account Manipulation – Used to detect when ABR removes a user from the local admin group (“… removed from local admins group”)
Indicators of Compromise
- [Log Source ] ABR event log messages in Windows Application channel – examples: “Received elevation approval reply”, “denied”, and multiple events matching those messages.
- [Wazuh Rule IDs ] Detection identifiers used in alerts – examples: 100111 (denied elevation), 100114 (multiple elevation requests); and other rule IDs 100112,100113,100115,100116.
- [File/System Paths ] Wazuh custom rule file path – example: /var/ossec/etc/rules/admin_by_request_rule.xml (contains the ABR detection rules).
Read more: https://wazuh.com/blog/integrating-admin-by-request-abr-with-wazuh/